Open VSX Supply Chain Attack: How a Compromised Dev Account Spread GlassWorm Malware to 22,000+ Users
📋 Executive Summary
On January 30, 2026, a sophisticated supply chain attack hit the Open VSX Registry, a popular open-source marketplace for VS Code extensions. Attackers compromised a legitimate developer account (oorzc) and published malicious updates to four widely used extensions. These poisoned versions, collectively downloaded over 22,000 times, delivered the GlassWorm malware loader, designed to steal credentials, crypto wallets, and sensitive developer data.
This beginner-friendly breakdown walks you through the entire attack chain, maps it to MITRE ATT&CK® techniques, and provides clear, actionable steps to defend against such threats, whether you're a developer, security student, or IT professional. Understanding this Open VSX supply chain attack is crucial in today's interconnected software ecosystem.
📑 Table of Contents
🌐 Real-World Scenario: When Trusted Tools Turn Toxic
Imagine you're a developer starting your day. You run ext install oorzc.ssh-tools to sync files via FTP, a tool you've trusted for two years. But this time, the update quietly installs a hidden malware loader. That's exactly what happened to thousands of developers in the Open VSX supply chain attack.
The attacker didn't create new, suspicious extensions, they hijacked established, legitimate ones from the publisher oorzc. This made the malicious updates blend in perfectly. The four extensions targeted were:
- FTP/SFTP/SSH Sync Tool (oorzc.ssh-tools version 0.5.1)
- I18n Tools (oorzc.i18n-tools-plus version 1.6.8)
- vscode mindmap (oorzc.mind-map version 1.0.61)
- scss to css (oorzc.scss-to-css-compile version 1.3.4)
These extensions had a combined history of over 22,000 downloads before the incident, making the supply chain compromise exceptionally effective.
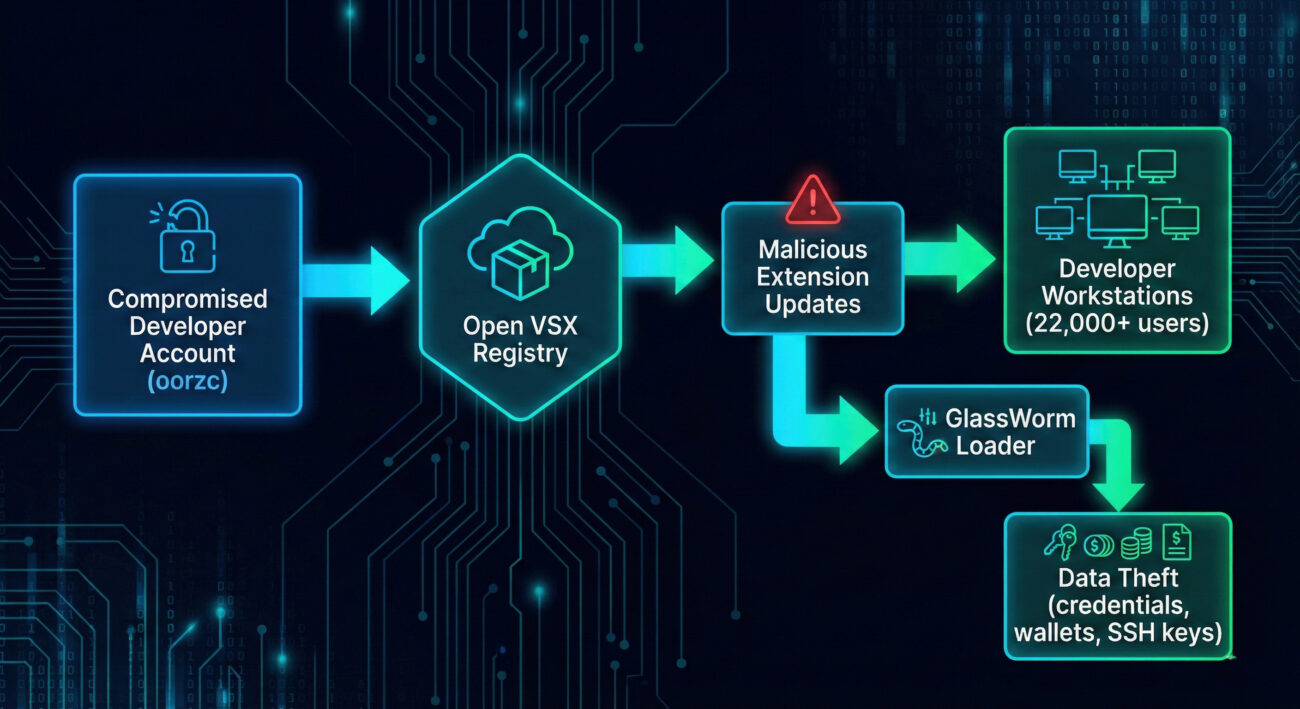
🔍 Step-by-Step: How the Open VSX Supply Chain Attack Unfolded
Step 1: Account Compromise (Initial Access)
The attackers gained unauthorized access to the oorzc publisher account on Open VSX. This was achieved via a leaked token or credential theft exact method unknown, but it falls under Valid Accounts (T1078) in MITRE ATT&CK.
Step 2: Malicious Extension Publication (Supply Chain Compromise)
Using the compromised account, attackers uploaded new versions of four existing extensions. The code was modified to include an obfuscated GlassWorm loader. These updates were signed and pushed as routine maintenance, bypassing any manual review.
Step 3: User Execution (T1204)
Developers with auto-update enabled or those who manually updated received the malicious versions. The extensions still functioned normally, so no immediate red flags were raised.
Step 4: Malware Loader Activation (Defense Evasion)
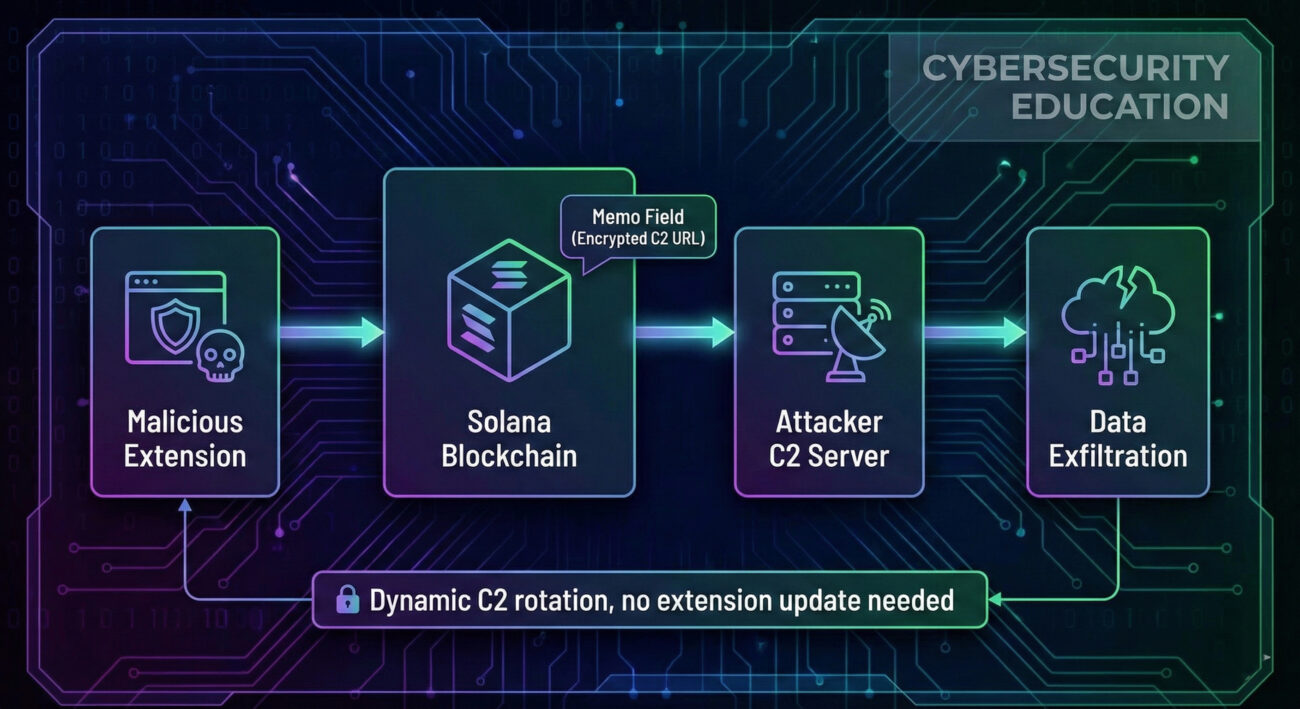
The malicious code used runtime decryption (T1027 - Obfuscated Files or Information) to unpack the final payload. It also employed EtherHiding: it fetched the real command-and-control (C2) addresses from Solana blockchain memos a clever way to rotate infrastructure without updating the extension (T1102 - Web Service).
Step 5: Reconnaissance & Evasion
Before deploying the full data-stealing payload, the malware checked the system locale. If it matched a Russian region, it would abort a classic sign of Russian-affiliated threat actors avoiding domestic prosecution (T1497 - Virtualization/Sandbox Evasion).
Step 6: Data Exfiltration
The final GlassWorm payload harvested:
- Browser data (logins, cookies, history, MetaMask wallets) from Chromium and Firefox.
- Documents from Desktop, Documents, Downloads.
- FortiClient VPN configs.
- Developer credentials:
~/.aws,~/.ssh, npm_authToken, GitHub tokens.
This data was exfiltrated over the C2 channel (T1041).
📌 MITRE ATT&CK Techniques Used in This Attack
Mapping the Open VSX supply chain attack to the MITRE ATT&CK framework helps us understand the adversary's playbook and build better defenses.
| Tactic | Technique ID | Name | How It Was Used |
|---|---|---|---|
| Initial Access | T1078.004 | Valid Accounts: Cloud Accounts | Compromised Open VSX publisher account |
| Execution | T1204.002 | User Execution: Malicious File | Users installed the trojanized extension |
| Persistence | T1195.002 | Supply Chain Compromise | Malicious updates in trusted extensions |
| Defense Evasion | T1027 | Obfuscated Files or Information | Loader decrypted at runtime |
| Defense Evasion | T1140 | Deobfuscate/Decode Files | Runtime decryption of payload |
| Command and Control | T1102 | Web Service | EtherHiding using Solana memos for C2 |
| Credential Access | T1555.003 | Credentials from Web Browsers | Stealing browser logins and cookies |
| Credential Access | T1552 | Unsecured Credentials | Scraping AWS, SSH, npm, GitHub tokens |
| Collection | T1005 | Data from Local System | Documents from user folders |
| Exfiltration | T1041 | Exfiltration Over C2 Channel | Stolen data sent to attacker server |
| Discovery/Evasion | T1497 | Virtualization/Sandbox Evasion | Locale check to avoid infecting Russian systems |
⚔️ Red Team vs Blue Team: Attacker Mindset vs Defender Actions
🔴 Red Team (Threat Actor) View
- Goal: Infiltrate developer ecosystems to steal credentials and intellectual property.
- Tactic: Compromise a trusted account (oorzc) to piggyback on existing reputation.
- Evasion: Use EtherHiding (blockchain) for resilient C2, avoiding hardcoded IPs.
- Payload: Multi-stage loader that checks for Russian locale before detonating.
- Targets: npm tokens, AWS keys, SSH, browser wallets high-value assets for lateral movement.
🔵 Blue Team (Defender) View
- Challenge: Detecting malicious updates in trusted extensions requires behavioral analysis.
- Action: Monitor for unusual outbound connections (e.g., to blockchain nodes).
- Response: Rapid takedown of malicious versions (done by Open VSX team).
- Hunt: Look for processes accessing browser profile data or SSH keys unexpectedly.
- Fix: Encourage MFA and token rotation for all publisher accounts; use runtime integrity checks.
⚠️ Common Mistakes & Best Practices
Mistakes (What Went Wrong)
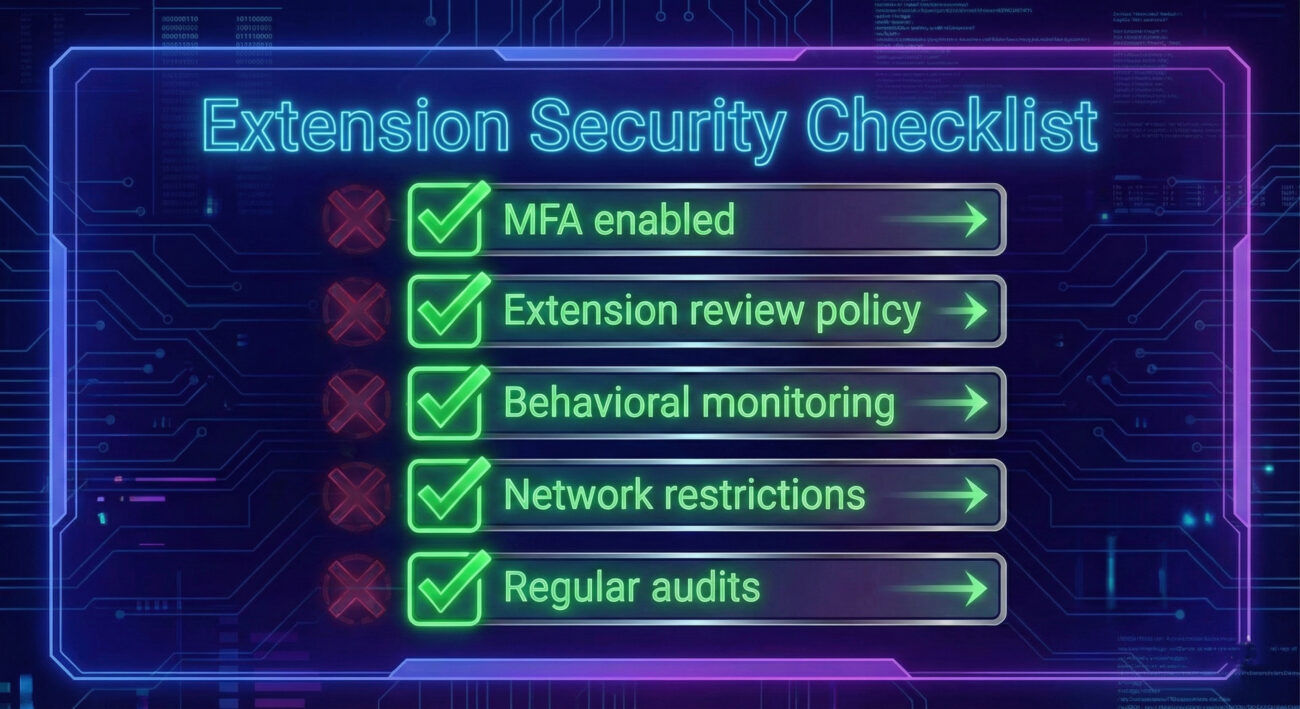
- No MFA enforcement on the Open VSX publisher account (likely).
- Extensions were not cryptographically signed in a way that prevents tampering.
- Users and organizations lacked visibility into extension behavior (no runtime monitoring).
- Assumption that "established" extensions are safe attackers exploit this trust.
- No immediate rollback mechanism: even after removal, infected versions persist until a clean update is published.
Best Practices (How to Defend)
- Enforce MFA and short-lived tokens for all extension publishers.
- Use extension allowlisting and only install from verified publishers after review.
- Monitor for suspicious behavior: unexpected network calls (especially to blockchain), file access to credential folders.
- Implement runtime application self-protection (RASP) or endpoint detection rules for credential access.
- Regularly audit installed extensions and compare hashes with known-good versions.
- For developers: use dedicated development environments or sandboxes to limit blast radius.
- Stay informed: follow security feeds like Socket.dev or The Hacker News for IoCs.
❓ Frequently Asked Questions
1. What is Open VSX and why was it targeted?
Open VSX is an open-source registry for VS Code extensions, used by platforms like Eclipse Theia and Gitpod. It's a prime target because compromising it can affect many developer tools downstream.
2. How does EtherHiding work?
EtherHiding uses blockchain transactions (like Solana memos) to store encrypted C2 addresses. The malware reads these memos to find where to send stolen data, making the infrastructure dynamic and hard to block.
3. Could this happen to the official VS Code Marketplace?
Yes, similar risks exist. Microsoft enforces more security (like code signing), but supply chain attacks via compromised accounts are always possible. Always verify publisher reputation and use additional tools.
4. How can I check if I'm affected?
Check your installed extensions against the list of malicious versions: versions 0.5.1 (ssh-tools), 1.6.8 (i18n-tools-plus), 1.0.61 (mind-map), 1.3.4 (scss-to-css). If you have them, assume compromise and rotate all credentials immediately.
5. What is GlassWorm malware?
GlassWorm is a sophisticated information stealer that targets developer machines. It steals browser credentials, crypto wallets, cloud tokens, and VPN configs, often used for lateral movement into corporate networks.
✅ Key Takeaways
- The Open VSX supply chain attack highlights that trusted accounts can be weaponized.
- Attackers use advanced evasion like EtherHiding and runtime decryption to avoid detection.
- Both publishers and consumers must adopt defense-in-depth: MFA, behavioral monitoring, and credential hygiene.
- MITRE ATT&CK mapping helps us understand adversary behavior and prioritize defenses (e.g., monitor T1102, T1552).
- Even after malicious extensions are removed, affected systems remain compromised until cleaned response must be swift.
🚀 Next Steps for Your Security Journey
Stay ahead of threats like this Open VSX supply chain attack by continuously learning and implementing proactive measures.
👉 Bookmark these resources for deeper dives:
- Socket's detailed analysis (External)
- MITRE ATT&CK® Framework
- Open VSX Registry (External)
- The Hacker News (External)
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































