🔓 Critical OpenClaw Remote Code Execution: One-Click Exploit Puts AI Assistants at Risk
📋 Table of Contents
🚨 Executive Summary: One-Click Takeover
A newly disclosed critical vulnerability in OpenClaw (CVE-2026-25253, CVSS 8.8) allows attackers to achieve remote code execution with just one click on a malicious link. OpenClaw, an open‑source AI personal assistant running locally on user devices, became an overnight sensation with over 149,000 GitHub stars. However, its Control UI trusts unvalidated URL parameters and automatically sends authentication tokens, enabling cross‑site WebSocket hijacking. An attacker can steal the token, disable sandboxing, and execute arbitrary commands on the host machine. This post breaks down the OpenClaw remote code execution flaw, how to defend against it, and why every user must update to version 2026.1.29 immediately.
The flaw was discovered by Mav Levin of depthfirst and patched on January 30, 2026. Even instances bound to localhost are vulnerable because the victim’s browser acts as a bridge. Below we dissect the exploit from both a beginner and professional perspective.
⚙️ Technical Breakdown: How OpenClaw RCE Works
The Root Cause: Trusting the Gateway URL
OpenClaw’s Control UI reads the gatewayUrl directly from the query string without any validation. When the page loads, it automatically establishes a WebSocket connection to that URL, sending the stored gateway token in the payload. Because the server does not validate the WebSocket Origin header, any website can initiate a cross-origin WebSocket connection to the victim’s local OpenClaw instance.
This token exfiltration lets an attacker’s site receive the token, then use it to authenticate as the victim. The token carries privileged scopes like operator.admin and operator.approvals, allowing the attacker to modify configuration and disable security guardrails.
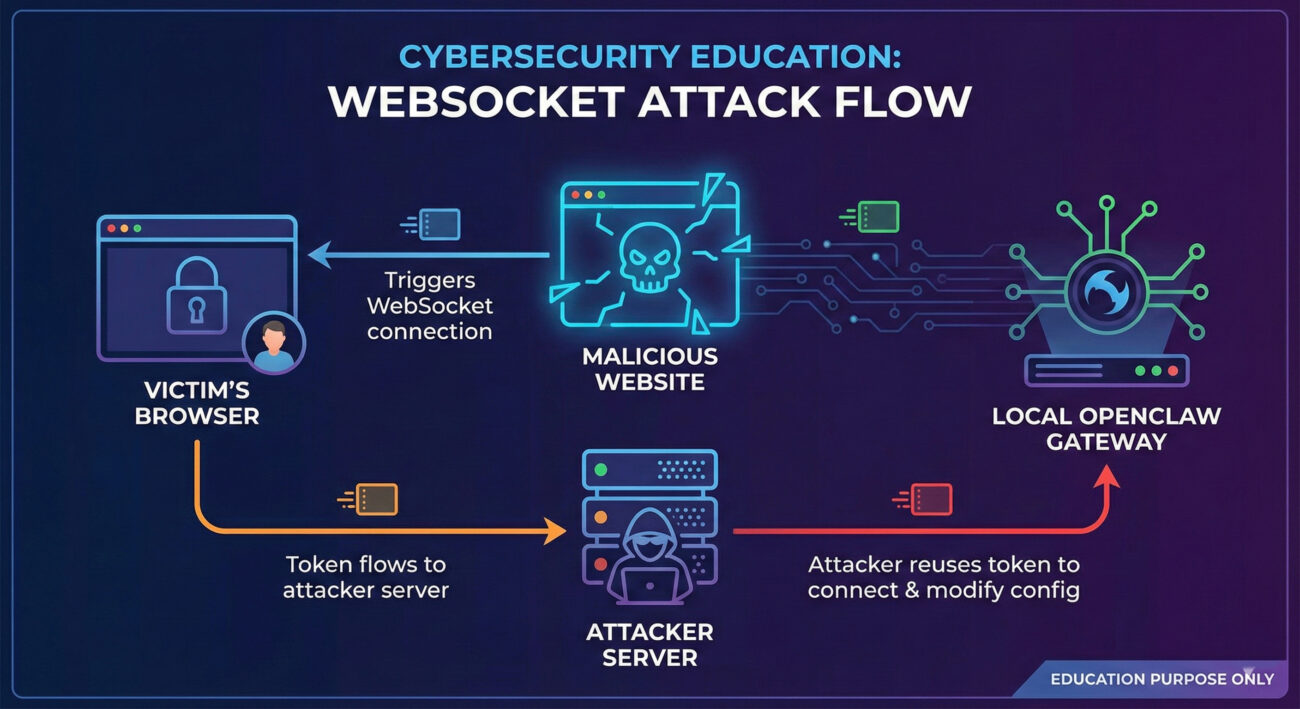
The Exploit Chain: From Click to Host Compromise
Once the attacker has the token, they can:
- Connect to the victim’s gateway API using the stolen token.
- Disable user confirmation by setting
exec.approvals.setto "off". - Escape the Docker container by setting
tools.exec.hostto "gateway" – forcing commands to run directly on the host. - Execute arbitrary system commands via
node.invokerequests.
The entire chain takes milliseconds and works even if OpenClaw listens only on loopback, because the browser initiates the outbound connection.
🌐 Real-World Scenario: Attack in Action
Imagine a cybersecurity professional, Alex, who installed OpenClaw to help automate tasks. Alex receives a direct message on social media with a link promising a free AI tool. The link points to a seemingly harmless webpage. Upon clicking, the page silently executes JavaScript that exploits the OpenClaw bug.
Without any visible effect, the attacker now has full control over Alex’s OpenClaw instance. They disable the sandbox and run a reverse shell, gaining persistent access to Alex’s laptop. Sensitive files, credentials, and internal network resources are now exposed. All from a single click.
🧩 Step-by-Step Exploit Chain (For Beginners)
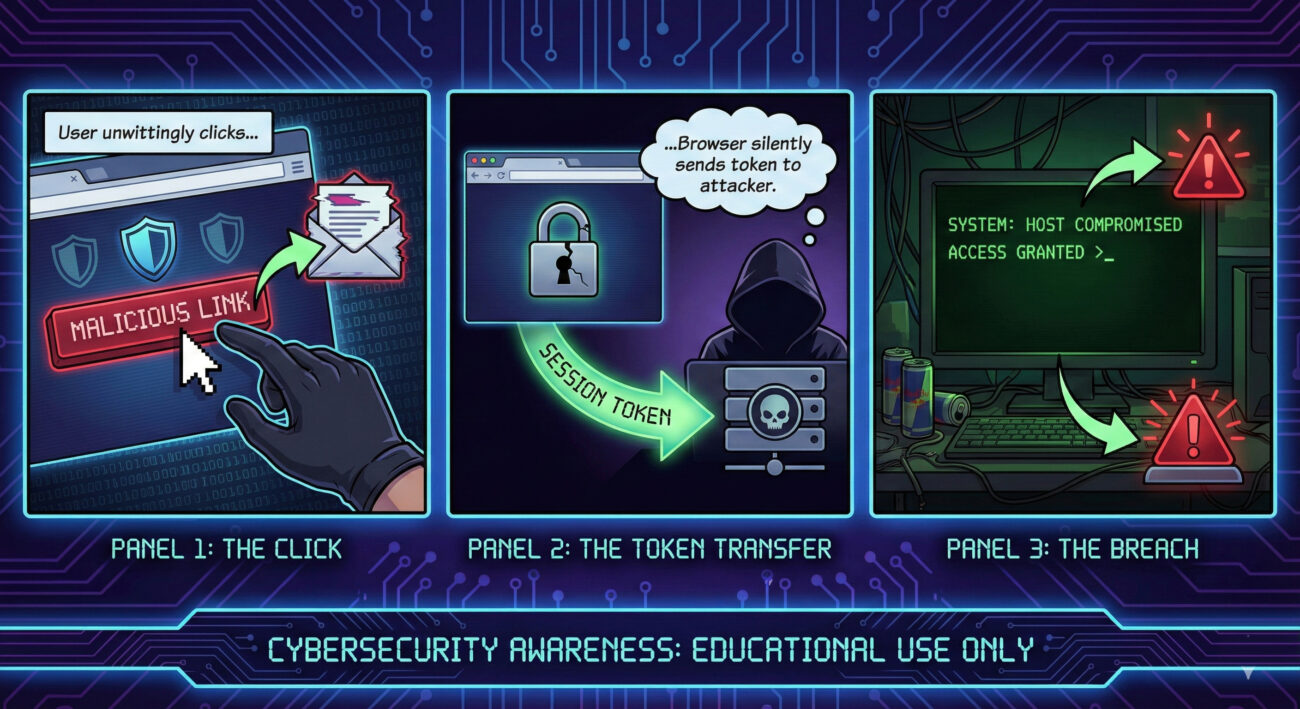
Step 1: Victim clicks a malicious link
The link leads to a page controlled by the attacker. It could be a phishing site, an ad, or a link in a chat.
Step 2: Malicious page sends WebSocket request
JavaScript on the page sends a WebSocket connection to the victim's OpenClaw gateway (usually localhost:8080 or similar). The browser automatically includes any stored authentication token because the OpenClaw server doesn't check the Origin header.
Step 3: Attacker captures the token
The token is sent to the attacker’s server (the same malicious site can receive it via WebSocket or separate exfiltration).
Step 4: Attacker impersonates the victim
Using the stolen token, the attacker connects to the victim’s OpenClaw API from their own machine, now with operator privileges.
Step 5: Disable security & escape container
The attacker changes settings to turn off user approval and forces tools to run on the host (bypassing Docker).
Step 6: Remote code execution
Finally, the attacker invokes node.invoke with arbitrary commands, achieving full RCE on the host machine.
📌 MITRE ATT&CK Mapping
This attack aligns with several MITRE ATT&CK techniques. Understanding them helps defenders build better detections.
| Tactic | Technique ID | Technique Name | How it applies |
|---|---|---|---|
| Initial Access | T1189 | Drive-by Compromise | Victim visits malicious website → one-click exploit. |
| Credential Access | T1539 | Steal Web Session Cookie / Token | Token exfiltration via cross-site WebSocket. |
| Defense Evasion | T1562.001 | Impair Defenses: Disable or Modify Tools | Attacker turns off user approval and sandbox. |
| Execution | T1059.008 | Command and Scripting Interpreter: Network Device CLI | Using node.invoke to run system commands. |
| Command and Control | T1105 | Ingress Tool Transfer | Attacker sends commands via WebSocket/API. |
✅ Common Mistakes & Best Practices
🔴 Mistakes (what users/admins do wrong)
- Assuming localhost is safe – The attack works via browser, bypassing localhost restrictions.
- Not updating OpenClaw immediately after patches are released.
- Clicking untrusted links on devices running OpenClaw.
- Disabling security features for convenience (e.g., turning off approval prompts).
🟢 Best Practices (how to protect)
- Update to OpenClaw version 2026.1.29 or later – contains the fix.
- Use a browser with strict origin isolation and disable WebSocket to localhost from remote sites (if possible).
- Implement network segmentation: run OpenClaw on a separate VLAN or with firewall rules blocking unexpected outbound WebSocket.
- Educate users about phishing links even for seemingly "internal" tools.
- Monitor for unusual API calls or config changes (e.g.,
exec.approvals.set).
⚔️ Red Team vs Blue Team View
🔴 Red Team (Attacker)
- Craft a malicious page with JavaScript that initiates WebSocket to
localhost:<port>. - Exfiltrate token via same-origin or separate server.
- Use token to connect, disable sandbox, and execute commands.
- Pivot to internal network.
🔵 Blue Team (Defender)
- Apply patch immediately (version 2026.1.29).
- Monitor WebSocket connections from browsers to local services.
- Detect token reuse from unexpected IPs.
- Alert on config changes like
exec.approvals.set. - Use EDR to watch for
node.invokespawning shells.
🛠️ Implementation Framework: Patching & Mitigation
OpenClaw maintainer Peter Steinberger released a fix on January 30, 2026. Here’s a quick framework to secure your deployment:
- Identify all instances of OpenClaw (version < 2026.1.29).
- Update immediately using the official GitHub repository or package manager.
- Verify the patch: ensure the Control UI now validates
gatewayUrland checks WebSocket Origin headers. - Harden configuration: if possible, disable automatic WebSocket connections or require explicit user consent.
- Monitor logs for any suspicious activity (e.g., tokens used from external IPs).
For temporary mitigation before patching, consider blocking outbound WebSocket connections from browsers to localhost using browser extensions or group policies, but patching is the only complete fix.
❓ Frequently Asked Questions
A: Visiting a malicious page is enough – no interaction beyond the page load is required. Hence "one‑click" (actually zero‑click after navigation).
A: If you haven’t updated to the patched version, an attacker could access your files, run commands, and steal data. Update now.
A: Yes. The victim’s browser runs on the same machine, so it can connect to 127.0.0.1. The attacker’s page initiates the connection from the browser, making it a local connection.
A: Look for unexpected changes in OpenClaw configuration (e.g., sandbox disabled), unknown outbound connections, or processes spawned by node. Also check logs for token reuse from unusual IPs.
A: No, it’s a web security flaw in the Control UI. However, the sandbox bypass makes any subsequent AI prompt injection far more dangerous.
🔑 Key Takeaways
- OpenClaw CVE-2026-25253 allows one-click remote code execution via malicious links.
- The root cause is unvalidated WebSocket origin and token exfiltration.
- Even loopback-only instances are vulnerable – the browser bridges the attack.
- Update to version 2026.2.13 immediately.
- Defenders should monitor for config changes and unexpected API calls.
- This attack maps to T1189, T1539, and others in MITRE ATT&CK.
🔒 Secure Your AI Assistant Now
Don't wait for a breach. Update OpenClaw, share this post with fellow developers, and review your endpoint security.
⬇️ Download Patched Version📚 Learn more about WebSocket security (internal guide) | AI security best practices (blog)
🔗 External Resources
- NIST NVD CVE-2026-25253 (official record).
- MITRE ATT&CK® – technique reference.
- OWASP WebSocket Hijacking – learn more about the attack class.
- OpenClaw GitHub – official repository.
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































