PluggyApe Malware Exposed
How Hackers Weaponize Signal for Silent Attacks Explained Simply
In the ever-evolving landscape of cyber threats, a new sophisticated malware named PluggyApe has emerged, showcasing a dangerous trend: the abuse of legitimate, encrypted communication services for command and control (C2). Unlike traditional malware that uses easily blocked domains or IP addresses, PluggyApe covertly leverages apps like Signal and Telegram to receive instructions and exfiltrate data, slipping past conventional network defenses. This post provides a comprehensive, beginner-friendly breakdown of the PluggyApe malware, its operational mechanics mapped to the MITRE ATT&CK framework, and actionable steps for defenders.
Table of Contents
- Executive Summary: The Stealthy Threat
- What is PluggyApe Malware?
- How PluggyApe Works: A Technical Deep Dive
- Mapping PluggyApe to MITRE ATT&CK
- Real-World Attack Scenario
- Red Team vs. Blue Team Perspective
- Common Mistakes & Best Practices
- Defense Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action
Executive Summary: The Stealthy Threat
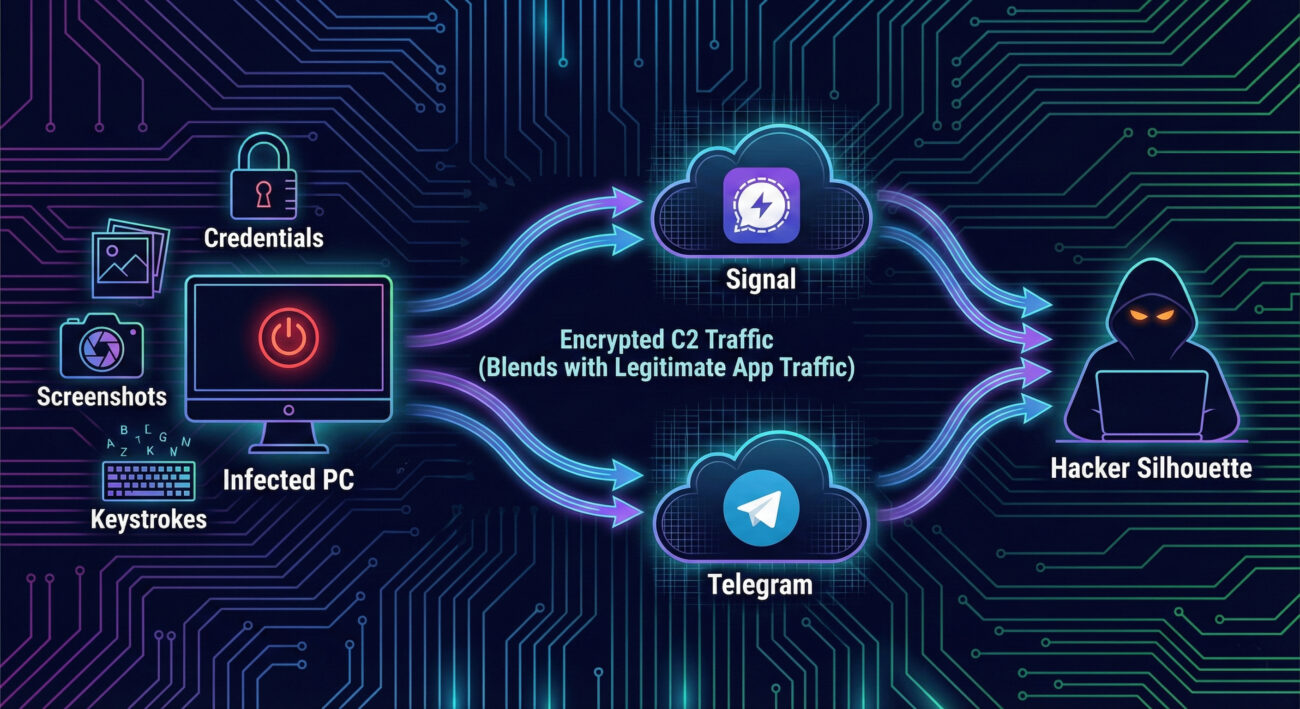
PluggyApe represents a significant shift in malware tradecraft. Its primary innovation is using end-to-end encrypted (E2EE) messaging platforms, specifically Signal's API and Telegram's Bot API, as its C2 channel. This technique, known as "living off the land" for network traffic, makes detection exceptionally difficult because the traffic appears as legitimate, encrypted communication to popular services. The PluggyApe malware is primarily an information stealer and backdoor, capable of harvesting credentials, capturing screenshots, logging keystrokes, and providing persistent remote access to compromised systems.
What is PluggyApe Malware?
Discovered in early 2026, PluggyApe is a modular malware written in C++. It functions as a full-featured remote access trojan (RAT) and data theft tool. The name "PluggyApe" derives from its use of "pluggable" transport mechanisms for C2 communications and its "ape"-like behavior of mimicking legitimate processes.
Its core capabilities include:
- Credential Theft: Harvests passwords from browsers, email clients, and system vaults.
- Keystroke Logging: Records every key pressed on the infected machine.
- Screen Capture: Takes periodic or on-demand screenshots.
- File Exfiltration: Searches for and steals specific document types.
- Persistence: Installs itself to survive reboots via registry keys or scheduled tasks.
- Evasion: Uses process hollowing to run malicious code inside legitimate-looking processes.
How PluggyApe Works: A Technical Deep Dive
The attack begins with a user being tricked into executing a malicious file, often delivered via spear-phishing emails or disguised as a software update. Once executed, PluggyApe deploys its multi-stage payload.
Step 1: Initial Compromise & Execution
The user executes a dropper, often a downloaded `.exe` or `.js` file. This dropper is heavily obfuscated to avoid signature-based detection. It decrypts and loads the main PluggyApe payload into memory.
Step 2: Persistence & Evasion Installation
The malware establishes persistence by creating a scheduled task (e.g., via `schtasks.exe`) or setting a Run registry key. It then uses a technique called Process Hollowing: it starts a legitimate, suspended Windows process (like `svchost.exe`), unmaps its memory, and injects its own malicious code before resuming it. This makes the malware appear as a trusted system process.
Step 3: Establishing C2 via Encrypted Apps
This is the hallmark of PluggyApe. The malware does not connect to a suspicious IP. Instead, it uses the official, public APIs of Signal and Telegram.
- Signal Method: It uses Signal's "Note to Self" feature or a controlled Signal account, sending encrypted messages that contain base64-encoded commands. The malware acts as a Signal client, checking for new messages at regular intervals.
- Telegram Method: It communicates with a Telegram Bot using the Bot API token. Commands are sent via `getUpdates`, and data is exfiltrated via `sendDocument` or `sendMessage`.
All this traffic is wrapped in TLS, identical to normal app traffic, making it nearly impossible to distinguish on the network level without deep behavioral analysis.
Step 4: Data Theft & Exfiltration
Upon receiving commands from the C2 channel, PluggyApe executes its modules. Stolen data (credentials, files, screenshots) is compressed, encrypted, and broken into chunks. These chunks are then uploaded as "messages" or "files" through the same Signal or Telegram channels, blending in with normal app data flow.
Mapping PluggyApe to MITRE ATT&CK
The MITRE ATT&CK framework is a knowledge base of adversary tactics and techniques. PluggyApe employs a wide range of these, making it a potent threat.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How PluggyApe Uses It |
|---|---|---|
| Initial Access | T1566.001 - Phishing: Spearphishing Attachment | Delivered via targeted emails with malicious attachments. |
| Execution | T1059.003 - Command and Scripting Interpreter: Windows Command Shell | Uses cmd.exe to execute commands for discovery and lateral movement. |
| Persistence | T1547.001 - Boot or Logon Autostart Execution: Registry Run Keys | Adds an entry to HKCU\Software\Microsoft\Windows\CurrentVersion\Run. |
| Defense Evasion | T1055.012 - Process Injection: Process Hollowing | Injects code into a legitimate svchost.exe process to hide. |
| Command & Control | T1071.001 - Application Layer Protocol: Web Protocols | Uses HTTPS to communicate with Signal/Telegram APIs (legitimate web services). |
| Command & Control | T1102.002 - Web Service: Bidirectional Communication | Uses Telegram Bot API and Signal as two-way communication channels. |
| Exfiltration | T1048.003 - Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted Non-C2 Protocol | Exfiltrates data over the encrypted but "legitimate" protocols of Signal/Telegram. |
| Collection | T1056.001 - Input Capture: Keylogging | Logs keystrokes to capture credentials and other sensitive input. |
Real-World Attack Scenario
Imagine a mid-sized financial company. An accountant receives an email seemingly from a tax software provider about a "critical security update." The attached file, `Update_2026.exe`, is the PluggyApe dropper.
- The accountant runs the file. The malware installs silently.
- PluggyApe establishes persistence and begins beaconing to a Telegram Bot, with traffic looking like normal web browsing to `api.telegram.org`.
- The attacker, from anywhere in the world, sends a command via Telegram to start keylogging and search for files containing "tax" or "invoice."
- The malware harvests saved credentials from the accountant's browser, including access to the company's online banking portal.
- Over the next days, sensitive financial documents and login credentials are slowly exfiltrated in small chunks via Signal messages, completely bypassing the company's firewall which allows traffic to signal.org.
- The breach goes unnoticed until fraudulent transactions are detected weeks later.
Red Team vs. Blue Team Perspective
Red Team (Threat Actor) View
Advantages:
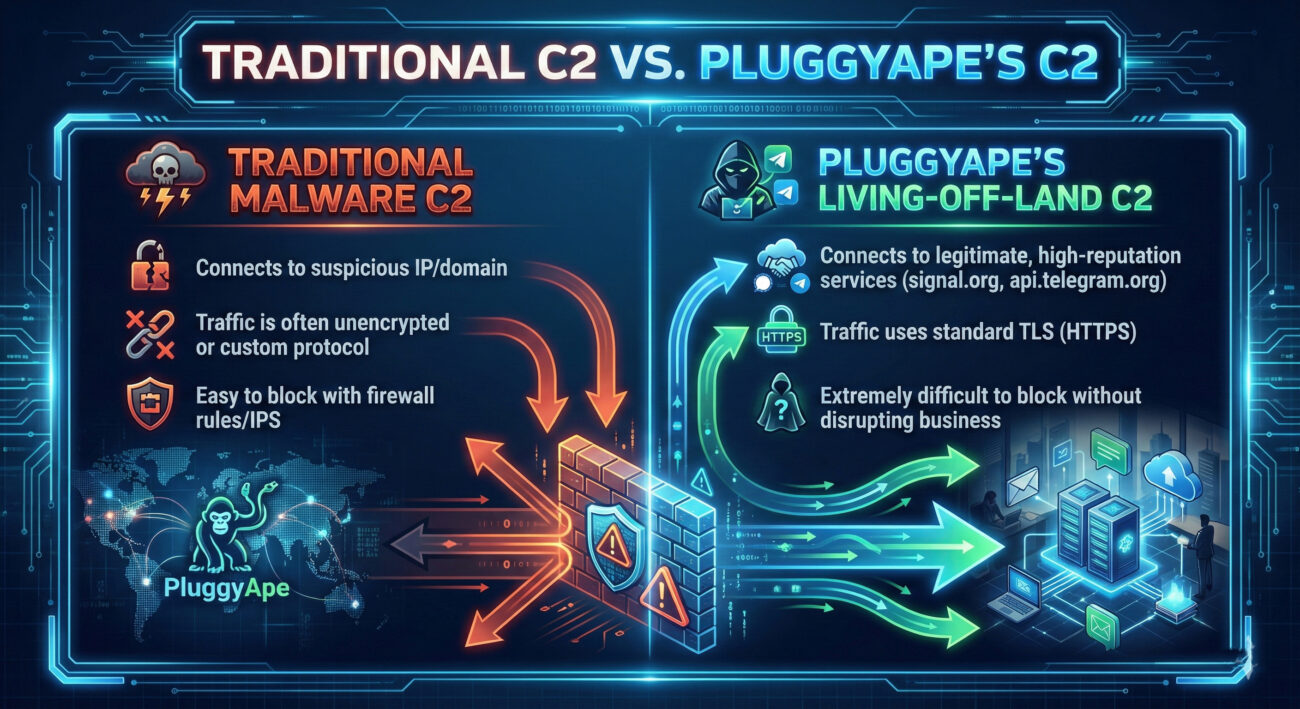
- Stealth: C2 traffic is indistinguishable from legitimate app use to most security tools.
- Reliability: Using major, highly available services ensures the C2 channel is almost never down.
- Bypassing Egress Filters: Most corporate firewalls allow outbound HTTPS to domains like `signal.org`.
- Low Cost & Easy Setup: Creating Telegram Bots or Signal accounts is free and simple.
Challenges:
- API Rate Limits: Telegram Bots have limits on message frequency.
- Need for Code Signing: To evade initial execution defenses, the dropper may need to be signed.
- Behavioral Detection: Unusual process activity (e.g., svchost making web calls) can still raise alerts.
Blue Team (Defender) View
Detection Challenges:
- Signature-Based Failure: AV won't catch unique or obfuscated payloads.
- Network Blind Spot: Blocking signal.org or api.telegram.org is often not a business-feasible option.
- Encryption: TLS 1.3 prevents inspection of packet contents without decryption.
Defensive Opportunities:
- Endpoint Detection & Response (EDR): Can spot malicious behavior like process hollowing and anomalous child processes from `svchost`.
- User Entity Behavior Analytics (UEBA): Can flag if a user's machine starts sending abnormal volumes of data to web APIs.
- Strict Application Allowlisting: Preventing unauthorized executables from running stops the initial infection.
- Network Traffic Analysis (NTA): While content is encrypted, patterns (beaconing timing, payload sizes) can be anomalous for these services.
Common Mistakes & Best Practices
Common Mistakes (To Avoid)
- Relying solely on traditional antivirus and firewall deny lists.
- Allowing users to run executables from downloads or emails without restriction.
- Not monitoring outbound traffic to "benign" SaaS and social media domains for anomalous patterns.
- Lack of multi-factor authentication (MFA) on critical accounts, making stolen passwords immediately useful.
- Failing to segment networks, allowing a single initial compromise to access sensitive data.
Best Practices (To Implement)
- Implement application allowlisting to prevent unauthorized programs from executing.
- Deploy a robust Endpoint Detection and Response (EDR) solution focused on behavioral analysis.
- Enforce MFA universally, especially for email, cloud, and financial accounts.
- Use a secure web gateway (SWG) or similar to inspect and log all outbound web traffic, even to trusted domains.
- Conduct regular security awareness training focused on identifying sophisticated phishing attempts.
- Adopt the principle of least privilege for both user accounts and system processes.
Defense Implementation Framework
Build your defense in layers using the "Defense-in-Depth" strategy:
- Prevent (Layer 1):
- Email filtering with advanced sandboxing for attachments.
- Strict application control/allowlisting policies.
- Regular patching of operating systems and software.
- Detect (Layer 2):
- Deploy EDR with 24/7 monitoring for techniques like process hollowing (T1055.012).
- Implement a SIEM to correlate logs from endpoints, network, and identity systems.
- Create alerts for unusual outbound data volumes to cloud service APIs from non-browser processes.
- Respond (Layer 3):
- Have an incident response plan that includes isolating infected hosts.
- Maintain and practice forensics capabilities to analyze memory and disk for IOCs.
- Ensure ability to revoke sessions and rotate credentials quickly.
Frequently Asked Questions (FAQ)
Q: Can I just block Signal and Telegram at my firewall to stop this malware?
A: Technically yes, but it's often impractical. These are legitimate business communication tools for many organizations. A better approach is behavioral monitoring on the endpoint and network to detect malicious use of these services, rather than outright blocking.
Q: Is my personal Signal/Telegram account at risk if I use these apps?
A: No. PluggyApe does not compromise the Signal or Telegram apps themselves. It uses their public APIs as a channel. Your personal messages remain end-to-end encrypted. The risk is to the infected machine, not your account on the service.
Q: As a beginner, what's the single most important thing I can do to protect against threats like PluggyApe?
A: Cultivate a mindset of zero-trust. Do not blindly trust emails, links, or attachments. Enable MFA everywhere possible, and keep your software updated. For system administrators, implementing application allowlisting is a highly effective first technical control.
Q: Where can I find more technical indicators (IOCs) for PluggyApe?
A: Follow trusted cybersecurity research blogs and threat intelligence platforms. For analysis on this specific threat, refer to the original article on The Hacker News. For general IOC databases, check resources like AlienVault OTX or VirusTotal.
Key Takeaways
- PluggyApe malware exemplifies the "living-off-the-land" trend, abusing trusted services like Signal and Telegram for stealthy C2 communications.
- Its techniques are comprehensively mapped in the MITRE ATT&CK framework, including Defense Evasion (Process Hollowing) and Command & Control (Web Services).
- Traditional signature-based defenses and simple network blocking are ineffective against this threat.
- The primary defense shift must be towards behavioral detection on endpoints (EDR) and sophisticated network traffic analysis.
- Fundamental security hygiene, application control, principle of least privilege, and user training, remains critically important.
Call to Action
Threats like PluggyApe are not theoretical, they are active and evolving. Begin strengthening your defenses today.
Your Action Plan:
- Assess: Review your current security controls. Do you rely mostly on antivirus and basic firewalls?
- Educate: Share this analysis with your IT team. Discuss the MITRE ATT&CK techniques mentioned.
- Implement: Choose one improvement from the Best Practices list, perhaps enabling MFA on all admin accounts or exploring EDR solutions, and act on it this week.
For continuous learning, bookmark reputable cybersecurity resources like SANS Blog, CISA Alerts, and The Hacker News.
Stay vigilant, stay informed, and build your defenses layer by layer.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































