RustyWater RAT
Unmasking MuddyWater's Latest Cyber Threat Explained Simply
Table of Contents
- Executive Summary: The RustyWater RAT Emerges
- Attack Breakdown: How the RustyWater RAT Infiltrates
- MITRE ATT&CK Mapping: The Hacker's Playbook
- Technical Perspective: Inside the RustyWater RAT
- Red Team vs. Blue Team: Attackers vs. Defenders
- Defense Framework: A 5-Step Action Plan
- Common Mistakes & Best Practices
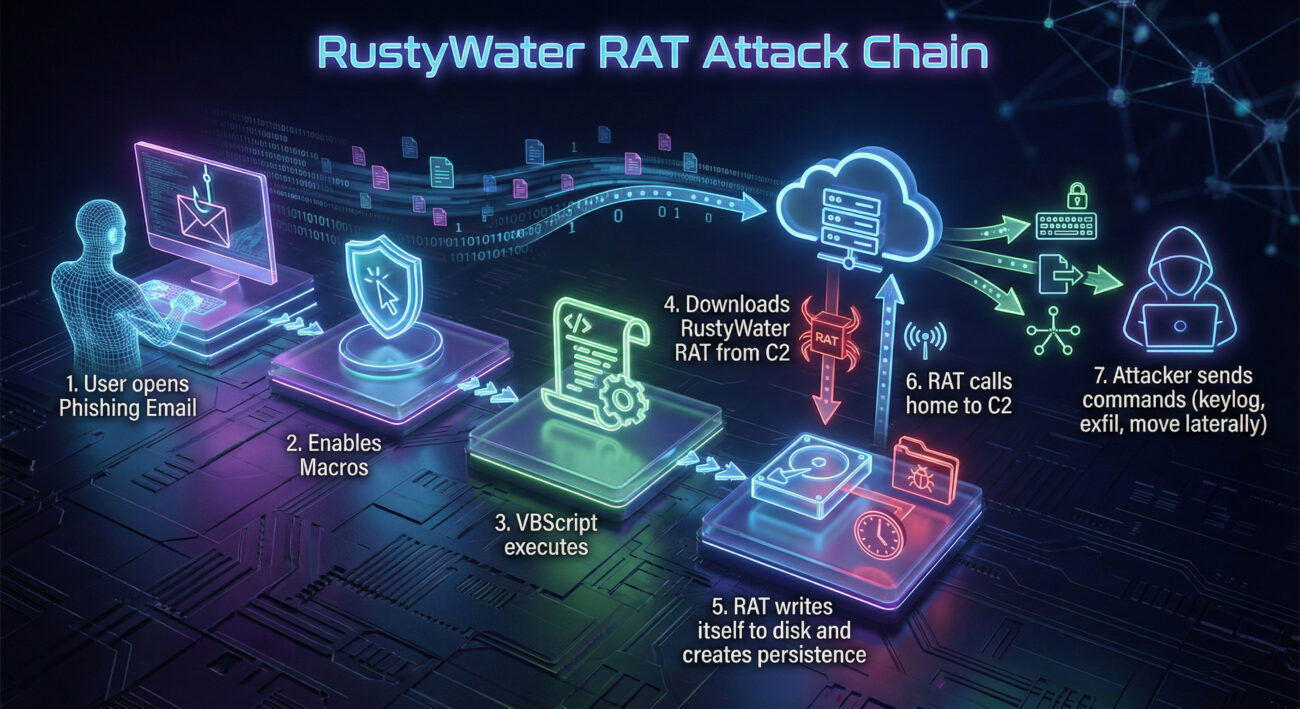
- Visual Aid: The RustyWater Attack Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Your Next Step: Call to Action
Executive Summary: The RustyWater RAT Emerges
The cybersecurity landscape has witnessed a significant evolution in the tools used by advanced persistent threat (APT) groups. In early 2026, the Iranian state-sponsored group known as MuddyWater (also tracked as MERCURY, Static Kitten, or TA450) unveiled a new weapon in its arsenal: a Remote Access Trojan (RAT) written in the Rust programming language, dubbed "RustyWater." This marks a strategic shift for the group, which has traditionally relied on PowerShell-based scripts and VBScript malware. The RustyWater RAT represents a more sophisticated, evasive, and persistent threat, primarily delivered through spear-phishing campaigns targeting government, telecommunications, and IT service organizations across the Middle East and Europe.
For beginners, understanding this attack is crucial. A RAT is a type of malware that gives an attacker remote administrative control over a victim's computer. By rewriting their tools in Rust, threat actors gain advantages like improved performance, memory safety (which ironically reduces detection signatures), and the ability to cross-compile for multiple operating systems. This breach vector underscores the continuous cat-and-mouse game in cybersecurity, where defenders must understand not just the "what," but the "how" and "why" of evolving hacker techniques.
Attack Breakdown: How the RustyWater RAT Infiltrates
The RustyWater RAT campaign follows a multi-stage, highly evasive infection chain designed to bypass traditional security measures. Let's break down the step-by-step process of how this attack unfolds, from the initial phishing email to full system compromise.
Step 1: The Phishing Hook
The attack begins with a carefully crafted spear-phishing email. The email appears to come from a trusted source, such as a regional telecommunications authority or a known business partner. It contains a malicious Microsoft Office attachment (like a .DOCX file) or a link to a compromised website. The email's subject and body are tailored to the target, increasing the likelihood of it being opened.
Step 2: Exploiting Trust & Macros
Once the victim opens the attachment, they are prompted to "Enable Content" or enable macros to view the document properly. This is a classic social engineering trick. Enabling macros allows the embedded malicious VBScript or PowerShell code to execute. This initial payload is not the RustyWater RAT itself but a lightweight downloader or dropper.
Step 3: The Dropper Fetches the Payload
The initial script (the dropper) connects to a hacker-controlled server (Command & Control or C2) and downloads the second-stage payload. In this case, it fetches the RustyWater RAT binary. The use of Rust allows this binary to be compiled as a standalone executable with no external dependencies, making it easier to run on the victim's machine without raising immediate suspicion.
Step 4: Persistence & Evasion
The RAT establishes persistence on the infected host. It may achieve this by creating scheduled tasks, modifying registry run keys, or dropping a shortcut file in the startup folder. Crucially, the Rust language's memory management makes the RAT harder to detect with signature-based antivirus tools. The RAT also employs basic obfuscation and may use legitimate Windows processes to mask its network communications (a technique called living-off-the-land).
Step 5: Remote Control & Data Theft
With the RAT firmly installed, the attackers have full remote control. They can now perform various malicious activities, including:
- Credential Harvesting: Using keyloggers or dumping credentials from browser memory and the Windows Credential Manager.
- Lateral Movement: Using stolen credentials to move laterally across the network, infecting other systems.
- Data Exfiltration: Stealing sensitive documents, emails, and intellectual property, sending them back to the C2 server.
- Dropping Additional Tools: Deploying other malware, like ransomware or crypto-miners, to further exploit the compromised environment.
MITRE ATT&CK Mapping: The Hacker's Playbook
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques based on real-world observations. Mapping the RustyWater RAT campaign to this framework helps defenders understand the specific methods used and plan effective countermeasures.
| MITRE ATT&CK Tactic | Technique ID & Name | How RustyWater Uses It |
|---|---|---|
| Initial Access | T1566.001 - Phishing: Spearphishing Attachment | Delivers the initial dropper via a malicious Office document attached to a targeted email. |
| Execution | T1059.005 - Command and Scripting Interpreter: Visual Basic | Uses VBScript macros within the Office document to execute the initial payload. |
| Persistence | T1547.001 - Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder | Adds entries to the Windows Registry or startup folder to ensure the RAT runs after every reboot. |
| Defense Evasion | T1027 - Obfuscated Files or Information | Uses Rust's inherent characteristics and potential packing to evade signature-based detection. |
| Command and Control (C2) | T1071.001 - Application Layer Protocol: Web Protocols | Communicates with its C2 server using HTTPS, blending traffic with normal web traffic. |
| Collection | T1005 - Data from Local System | Scans the local file system for documents of interest (PDF, DOCX, XLSX) to exfiltrate. |
| Exfiltration | T1041 - Exfiltration Over C2 Channel | Sends stolen data back to the attacker over the same established C2 channel. |
Technical Perspective: Inside the RustyWater RAT
From a technical standpoint, the shift to Rust by a group like MuddyWater is noteworthy. Rust is a systems programming language praised for its speed and memory safety (it prevents common bugs like buffer overflows). For threat actors, these features are a double-edged sword: they create more stable, less crash-prone malware that is also harder for traditional antivirus to spot, as it doesn't exhibit the "messy" memory patterns of C/C++ malware.
Key Technical Characteristics:
- Static Compilation: The RAT is compiled into a single executable with all libraries included, requiring no installation of the Rust runtime on the target machine.
- Reduced Forensic Footprint: Memory safety means fewer anomalous memory allocations that might trigger Endpoint Detection and Response (EDR) alerts.
- Cross-Platform Potential: Rust can be easily cross-compiled to target Windows, Linux, or macOS, broadening the potential victim pool.
- Obfuscation: While the core binary might be in Rust, attackers can still employ packers or runtime crypters to further obfuscate the code and hinder static analysis.
Below is a simplified pseudocode representation of how the dropper might fetch and execute the RustyWater RAT. This illustrates the logic, not the actual malicious code.
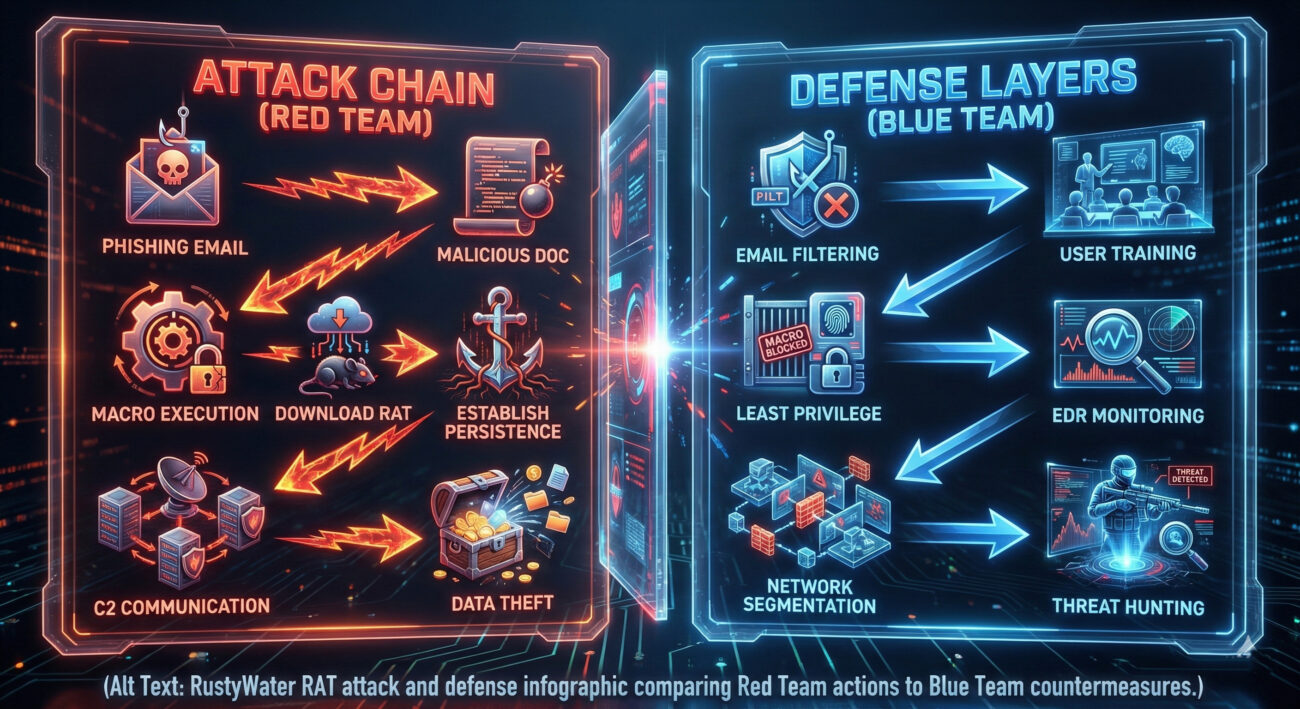
Red Team vs. Blue Team: Attackers vs. Defenders
The Red Team (MuddyWater's View)
Objectives: Establish long-term access, steal specific data, maintain stealth.
- Leverage Social Engineering: Spend time crafting believable phishing lures tailored to the industry and roles of targets.
- Embrace Legitimate Tools: Use built-in system tools (like PowerShell, wmic, net) for post-exploitation to avoid dropping additional files.
- Invest in Development: Shift to modern, efficient languages like Rust to lower the detection rate and improve malware reliability.
- Operate Slowly & Quietly: Use low-and-slow data exfiltration and minimal C2 communication to avoid triggering network thresholds.
The Blue Team (Defender's View)
Objectives: Prevent initial infection, detect anomalous behavior, contain breaches, eradicate threats.
- Harden the Human Layer: Implement ongoing, realistic phishing simulations and security awareness training.
- Disable Office Macros by Default: Use Group Policy to block macros from the internet, a critical mitigation for this attack vector.
- Deploy Behavior-Based EDR: Move beyond signatures. Use EDR solutions that monitor for suspicious process chains (e.g., winword.exe spawning powershell.exe).
- Enforce Network Segmentation: Limit lateral movement by segmenting networks, making it harder for a RAT to access critical servers.
- Implement Application Allowlisting: Only allow pre-approved applications to run, preventing unknown RATs from executing.
Defense Framework: A 5-Step Action Plan
Here is a practical, step-by-step framework any organization can implement to defend against threats like the RustyWater RAT.
Step 1: Email Security & User Training
Deploy advanced email security gateways that use sandboxing and URL analysis. More importantly, conduct regular, engaging security awareness training that teaches users how to identify and report phishing attempts. Make reporting easy with a dedicated email button.
Step 2: Endpoint Hardening
Configure endpoints securely. This includes:
- Disabling Office macros for files from the internet.
- Applying the principle of least privilege (PoLP) so users don't run with administrator rights.
- Enabling Windows Defender Attack Surface Reduction (ASR) rules, particularly those blocking executable content from email and Office apps.
Step 3: Advanced Endpoint Protection
Move beyond traditional antivirus. Implement a modern Endpoint Detection and Response (EDR) or Extended Detection and Response (XDR) platform. These tools monitor for behavioral anomalies, such as a Word document spawning a scripting engine, which is a key indicator of this attack chain.
Step 4: Network Monitoring & Segmentation
Monitor outbound network traffic for connections to known-bad IPs/domains (via threat intelligence feeds) and for unusual data transfers. Segment your network to contain any potential breach. Critical servers should only be accessible from specific, authorized workstations.
Step 5: Threat Intelligence & Proactive Hunting
Subscribe to threat intelligence feeds to stay updated on the latest indicators of compromise (IOCs) for groups like MuddyWater. Don't just wait for alerts; empower your security team to conduct proactive threat hunting. Look for the TTPs (Tactics, Techniques, and Procedures) mapped in the MITRE ATT&CK table above within your own environment.
Common Mistakes & Best Practices
Common Mistakes (What to Avoid)
- Allowing users to run with local administrator privileges by default.
- Having a "set and forget" mentality with security tools without tuning alerts.
- Treating security awareness training as a yearly checkbox exercise.
- Relying solely on perimeter defenses like firewalls, ignoring insider and lateral movement threats.
- Not having an incident response plan tested and ready.
Best Practices (What to Implement)
- Enforce the principle of least privilege (PoLP) across all systems and users.
- Adopt a zero-trust security model, verifying every access request.
- Conduct engaging, simulated phishing campaigns quarterly.
- Implement multi-factor authentication (MFA) on all critical accounts and services.
- Maintain regular, tested backups of critical data, stored offline or in an immutable format.
- Establish a Security Operations Center (SOC) or use a Managed Detection and Response (MDR) service for 24/7 monitoring.
Visual Aid: The RustyWater Attack Flow
Frequently Asked Questions (FAQ)
Q: Why is MuddyWater using Rust now? Isn't that more work for them?
A: Yes, it requires more development skill. However, the payoff is significant: Rust-based malware is more stable, harder to reverse-engineer, and crucially, has a much lower detection rate by traditional antivirus due to its clean memory patterns and the relative novelty of Rust in the malware space. It's a long-term investment in operational security.
Q: As a small business, are we a target for this kind of sophisticated attack?
A: While APT groups often target governments and large corporations, they frequently use smaller businesses in the supply chain as a stepping stone. If you are a managed service provider (MSP), IT vendor, or hold data valuable to a larger target, you could be at risk. The defense principles (user training, MFA, backups) are scalable and vital for organizations of all sizes.
Q: What's the single most effective defense against this specific attack?
A> There is no "silver bullet," but if we had to choose one, it would be disabling Office macros for documents originating from the internet via Group Policy. This breaks the initial execution chain for this and countless other malware campaigns. Combine this with user training to explain why this policy is in place.
Q: Where can I find Indicators of Compromise (IOCs) for RustyWater?
A> Reputable threat intelligence platforms and blogs from cybersecurity companies often publish IOCs (hashes, IPs, domains) following major disclosures. Always consult multiple sources. For educational purposes, you can review reports on sites like Palo Alto Networks Unit 42, CrowdStrike Blog, or Mandiant Blog.
Key Takeaways
1. Evolution is Constant: Threat actors like MuddyWater are continuously evolving, adopting modern programming languages like Rust to create stealthier, more resilient malware.
2. The Human Element is Critical: The attack starts with a phishing email. A well-trained user is your most effective first line of defense.
3. Defense in Depth is Non-Negotiable: No single tool can stop every threat. You need layered security: email filtering, endpoint hardening, EDR, network controls, and proactive hunting.
4. Know the Adversary's Playbook: Using frameworks like MITRE ATT&CK helps you anticipate attacker moves and validate your defenses against real-world techniques.
5. Actionable Steps Exist: From disabling internet macros to implementing EDR and MFA, there are clear, actionable measures you can take today to significantly raise your security posture against threats like the RustyWater RAT.
Your Next Step: Call to Action
Don't Wait for a Breach to Act
The technical details of the RustyWater RAT highlight a clear trend towards more sophisticated attacks. Your defense must be equally sophisticated and proactive.
This Week: Check your Group Policy or endpoint management console. Ensure macros from the internet are blocked. Schedule a 15-minute security awareness email for your team about phishing.
This Month: Review your endpoint security. Are you using next-gen EDR, or just traditional antivirus? Begin a pilot if needed. Test your backups.
Stay Informed: The cybersecurity landscape changes daily. Follow trusted resources to keep learning:
The Hacker News |
Krebs on Security |
CISA Alerts |
MITRE ATT&CK Framework
Remember: Cybersecurity is a journey, not a destination. Start building your defense layers today.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































