Sitecore Zero-Day Exploit
How APTs Breach CMS Defenses Explained Simply
Table of Contents
- Executive Summary: The Sitecore Zero-Day Threat
- The Attack in Detail: From Zero-Day to WEBC2 Backdoor
- MITRE ATT&CK Framework Mapping
- Red Team vs Blue Team: Attack and Defense Perspectives
- Common Mistakes & Best Practices for CMS Security
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call-to-Action: Fortify Your Defenses
Executive Summary: The Sitecore Zero-Day Threat
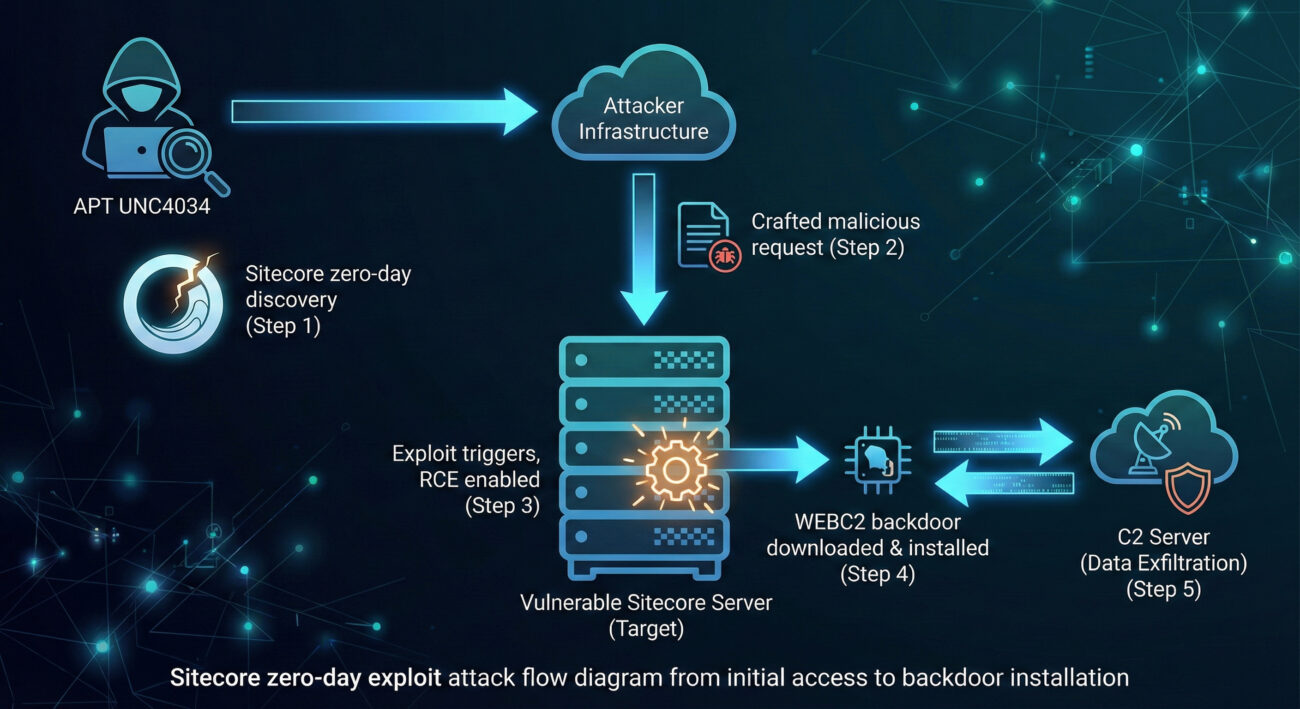
In early 2026, cybersecurity researchers uncovered a sophisticated attack campaign where a China-linked Advanced Persistent Threat (APT) group, tracked as UNC4034, successfully exploited a previously unknown zero-day vulnerability in the Sitecore Experience Platform (XP). This critical vulnerability (CVE-2026-XXXXX) allowed the threat actors to gain initial access to target networks and deploy a stealthy backdoor called WEBC2. The campaign primarily focused on organizations in Australia and Southeast Asia, aiming for espionage and long-term access.
This exploit serves as a stark reminder that even enterprise-grade Content Management Systems (CMS) like Sitecore are not immune to targeted zero-day attacks. For cybersecurity beginners and professionals alike, understanding the anatomy of this breach is crucial for building effective defenses. This analysis will break down the attack chain, map it to the MITRE ATT&CK framework, and provide actionable defense strategies.
The Attack in Detail: From Zero-Day to WEBC2 Backdoor
The core of this exploit was a critical vulnerability within Sitecore XP's serialization and deserialization processes. In simple terms, serialization is how an application converts complex data (like an object) into a format that can be easily stored or transmitted. Deserialization is the reverse process. The vulnerability existed because Sitecore did not properly validate or sanitize this serialized data during the deserialization step.
Technical Breakdown of the Vulnerability
The attackers sent a specially crafted, malicious serialized object to a vulnerable Sitecore endpoint. Because the system trusted this input without sufficient checks, during deserialization, the malicious payload was executed. This is known as an Insecure Deserialization flaw, leading to Remote Code Execution (RCE). This gave the hacker the ability to run any command on the underlying server with the same permissions as the Sitecore application.
Step 1: Reconnaissance & Weaponization
APT UNC4034 identified targets using Sitecore XP and likely researched its architecture. They developed or acquired an exploit for the undisclosed deserialization flaw, weaponizing it into a deliverable payload.
Step 2: Delivery & Exploitation
The group sent an HTTP request containing the malicious serialized data to the target's Sitecore server. The vulnerable code path processed this request, triggering the exploit and granting RCE.
Step 3: Installation & Persistence
Using the RCE capability, the attackers downloaded and installed the WEBC2 backdoor onto the compromised server. WEBC2 is designed to blend in with normal web traffic, often masquerading as a legitimate DLL or web module, ensuring persistent access.
Step 4: Command & Control (C2)
The WEBC2 backdoor established a communication channel with the attacker's C2 server, waiting for further instructions such as data theft, lateral movement, or deploying additional malware.
MITRE ATT&CK Framework Mapping
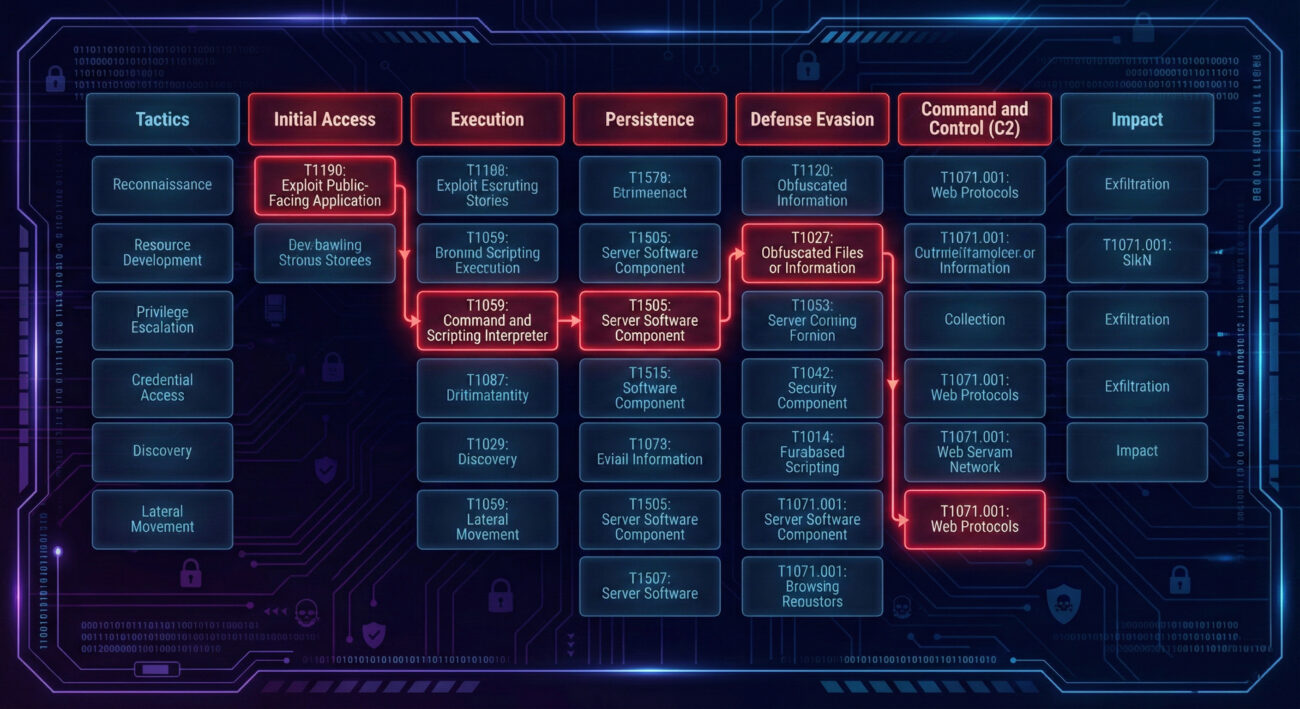
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques. Mapping this attack helps defenders understand and counter the threat. Here’s how UNC4034's activities align:
| MITRE ATT&CK Tactic | Technique (ID) | How UNC4034 Applied It |
|---|---|---|
| Initial Access | Exploit Public-Facing Application (T1190) | They exploited the Sitecore XP zero-day vulnerability, which was a public-facing web application. |
| Execution | Command and Scripting Interpreter (T1059) | The RCE exploit allowed them to execute arbitrary system commands on the server. |
| Persistence | Server Software Component (T1505) | The WEBC2 backdoor was installed as a malicious component within the Sitecore web server environment. |
| Defense Evasion | Masquerading (T1036) & Obfuscated Files or Information (T1027) | WEBC2 is designed to look like a legitimate web file and uses encryption for C2 communication to avoid detection. |
| Command & Control | Web Protocols (T1071.001) | The backdoor communicates with the attacker's infrastructure using standard HTTPS traffic, blending in with normal web traffic. |
Red Team vs Blue Team: Attack and Defense Perspectives
Understanding both sides of this cyber attack is key to building resilience. Let's examine the viewpoints of the threat actors (Red Team) and the defenders (Blue Team).
Red Team (APT UNC4034) View
- Objective: Gain stealthy, long-term access to target networks for espionage.
- Opportunity: An unpatched, unknown (zero-day) flaw in a widely trusted CMS provides a perfect, low-noise entry point.
- Technique: Weaponize the deserialization bug. Use RCE to deploy a custom backdoor that mimics legitimate traffic to avoid network security tools.
- Advantage: Defenders are unaware of the vulnerability, so traditional signature-based defenses like antivirus are ineffective at the initial stage.
- Goal: Maintain persistence and move laterally to high-value data stores.
Blue Team (Defenders) View
- Challenge: Defending against an unknown attack vector for which there is no patch initially.
- Strategy: Rely on strong proactive and behavioral security measures.
- Detection: Monitor for anomalous process creation from web server accounts (e.g., w3wp.exe spawning cmd.exe). Use network sensors to look for unusual outbound HTTPS patterns from web servers.
- Mitigation: Apply the principle of least privilege to service accounts. Implement robust web application firewalls (WAFs) with behavioral analysis capabilities to block suspicious deserialization attempts.
- Response: Have an incident response plan ready for suspected web server compromises, including isolation, forensics, and recovery steps.
Common Mistakes & Best Practices for CMS Security
Many organizations fall into common traps that make them vulnerable to such attacks. Here’s what to avoid and what to implement.
Common Mistakes (The "Don'ts")
- Slow Patching Cadence: Delaying the application of security updates for CMS platforms and underlying frameworks.
- Excessive Privileges: Running the CMS web application with administrator or high-privilege system accounts.
- Lack of Input Validation: Assuming all input to the CMS is trusted, not sanitizing or validating user/serialized data.
- Minimal Monitoring: Not monitoring web server logs, process creation events, or outbound network traffic from CMS servers.
- Default Configurations: Using default installation paths, admin URLs, and credentials, making reconnaissance easier for attackers.
Best Practices (The "Dos")
- Implement a Rigorous Patch Management Policy: Update and patch all software, especially CMS cores, plugins, and server OS, as soon as patches are available and tested.
- Adopt the Principle of Least Privilege (PoLP): Run the CMS under a dedicated service account with only the permissions it absolutely needs.
- Harden the Web Application: Use a secure configuration. Employ a Web Application Firewall (WAF) to filter and monitor HTTP traffic, blocking common exploit patterns.
- Enable Detailed Logging & Use SIEM: Aggregate logs and use a Security Information and Event Management (SIEM) system to detect anomalies like unexpected RCE patterns.
- Conduct Regular Vulnerability Scans & Penetration Tests: Proactively find and fix weak spots before attackers do.
Frequently Asked Questions (FAQ)
Q: What is a zero-day vulnerability/exploit?
A: A zero-day vulnerability is a software flaw that is unknown to the vendor or for which no patch is available. A zero-day exploit is the method attackers use to take advantage of this flaw before it is fixed. This gives defenders "zero days" to prepare, making it highly dangerous.
Q: How can I check if my Sitecore instance is vulnerable to this specific attack?
A: First, immediately check the official Sitecore Trust Center and your version's release notes for any security advisories. You should also consult with your IT security team to review logs for any suspicious activity related to serialization processes or unexpected outbound connections from your web servers.
Q: As a beginner, what's the single most important thing I can do to protect a web server?
A: Implement a disciplined and timely patch management process. The vast majority of exploits target known vulnerabilities for which patches already exist. Keeping software updated is your most effective shield.
Q: Where can I learn more about the MITRE ATT&CK framework?
A: The best resource is the official MITRE ATT&CK® website. For practical learning, explore free resources like the TryHackMe or Hack The Box platforms, which have modules dedicated to ATT&CK.
Key Takeaways
- No Platform is Immune: Enterprise CMS like Sitecore are high-value targets for APT groups due to their widespread use and access to sensitive data.
- Insecure Deserialization is Critical: Flaws in how applications process serialized data can lead directly to devastating Remote Code Execution.
- Behavior Over Signatures: Defending against zero-day attacks requires focusing on abnormal behavior (e.g., web servers executing command line) rather than just known malware signatures.
- Layered Defense is Key: Combine timely patching, strict access controls (least privilege), network segmentation, proactive monitoring, and a robust WAF to build resilience.
- Know Your Adversary's Playbook: Using frameworks like MITRE ATT&CK helps anticipate attack techniques and implement targeted defenses.
Call-to-Action: Fortify Your Defenses
Don't wait for a breach to happen. Take proactive steps today:
- Audit Your External-Facing Software: Inventory all public-facing applications, like your CMS, and verify their versions and patch status.
- Review and Harden Configurations: Ensure service accounts follow the principle of least privilege. Configure your WAF with rules specific to your applications.
- Simulate an Attack: Consider engaging a professional penetration testing service to ethically test your defenses against techniques like those used by UNC4034.
- Continuous Learning: Stay informed. Follow trusted security blogs like The Hacker News, Krebs on Security, and the CISA Advisories.
Knowledge is the first line of defense. Share this analysis with your team to start a conversation about improving your organization's security posture.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































