Software (T1592.002)
Ultimate Guide to Gather Victim Host Information - Software: Attack & Defense
Gather Victim Host Information involves collecting technical details about software applications, versions, and configurations present on a target's systems to identify vulnerabilities and plan follow-on attacks.
ATT&CK ID: T1592.002
Tactics: Reconnaissance
Platforms: PRE
Difficulty: 🟢 Easy
Prevalence: High
Table of Contents
- Understanding Gather Victim Host Information in Simple Terms
- Decoding the Jargon: Key Terms for Gather Victim Host Information
- The Attacker's Playbook: Executing Gather Victim Host Information
- The Defender's Handbook: Stopping Gather Victim Host Information
- Building Resilience: Mitigation Strategies for Gather Victim Host Information
- Gather Victim Host Information Cheat Sheet
- Conclusion and Next Steps
Understanding Gather Victim Host Information in Simple Terms
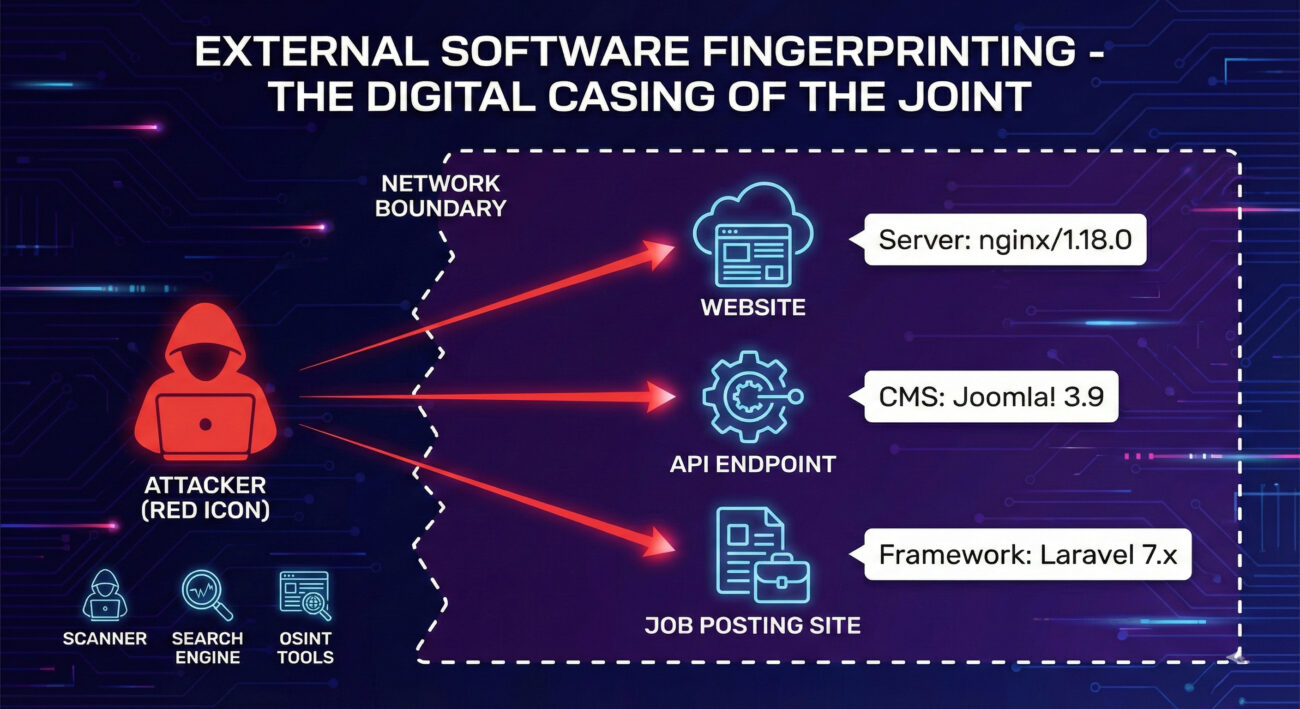
Imagine a burglar casing a neighborhood not just to find which houses look wealthy, but to read the stickers on the windows that show what security system is installed. Gather Victim Host Information is exactly that digital reconnaissance phase. Before launching any real attack, adversaries need to know what they're up against.
This technique specifically focuses on identifying the software running on a target's systems, web server versions (like Apache 2.4.49), CMS platforms (WordPress 5.7), or business applications. Knowing this allows an attacker to search for known, unpatched vulnerabilities (CVEs) in those exact versions, dramatically increasing their chance of a successful breach.
Decoding the Jargon: Key Terms for Gather Victim Host Information
| Term | Simple Definition | Why It Matters |
|---|---|---|
| Banner Grabbing | Connecting to a network service (like web, SSH, FTP) and recording the version information it willingly announces. | The most direct way to get accurate software version data. Often the first step in this reconnaissance. |
| Fingerprinting | Deducing software/OS details by analyzing subtle differences in how systems respond to network probes. | Used when banners are hidden. Allows identification even when the target tries to hide its stack. |
| OSINT (Open-Source Intelligence) | Information gathered from publicly available sources like websites, forums, and job boards. | Adversaries use OSINT to find tech stack mentions (e.g., "Seeking Django developer") without triggering alarms. |
| Version Disclosure | When an application or server unintentionally reveals its version number in HTTP headers, error messages, or source code comments. | A common security weakness that directly enables this ATT&CK technique. |
The Attacker's Playbook: Executing Gather Victim Host Information
Step-by-Step Breakdown
The process is methodical and often entirely passive or semi-passive to avoid detection.
- Target Scoping: Identify the target organization's public-facing digital assets (domains, IP ranges).
- Passive Enumeration: Use search engines (Google dorking), job sites (LinkedIn, Indeed), and GitHub to find mentions of specific software, frameworks, or technologies used by the company's IT staff or developers.
- Active Fingerprinting: Send carefully crafted probes to the target's web servers, APIs, and other open services. Analyze HTTP response headers, error messages, and file structures (e.g., /robots.txt, /wp-admin/).
- Banner Grabbing: Use tools like Netcat, Telnet, or Nmap to connect to services on non-web ports (SSH-22, FTP-21, SMTP-25) and capture their welcome banners.
- Analysis & Vulnerability Mapping: Compile the harvested software and version data. Cross-reference it with databases of known exploits (like Exploit-DB, NVD) to create a prioritized list of potential attack vectors.
Red Team Analogy & Mindset
Think like a lockpicker surveying a lock brand and model. You don't try every pick at random. First, you visually inspect the lock to see if it's a Medeco, Schlage, or Kwikset. Each brand and model has known weaknesses and requires specific tools. This reconnaissance phase is that inspection. The goal is efficiency: spend minutes on reconnaissance to save hours on failed exploitation attempts later.
Tools & Command-Line Examples
- Nmap: The quintessential network scanner with powerful version detection scripts.
- Wappalyzer / WhatWeb: Specialized tools for fingerprinting web technologies.
- Netcat: The "Swiss army knife" for manual banner grabbing.
Example Nmap Command for Service/Version Detection:
nmap -sV --script banner,http-headers -p 80,443,22,21 target-company.com
Manual HTTP Header & Banner Check with cURL & Netcat:
# Check HTTP headers for server and framework info curl -I https://target-company.com # Grab banner from an SSH service manually nc -nv target-company.com 22
Real-World Campaign Example
APT28 (Fancy Bear), a Russian state-sponsored group, has extensively used this technique. In campaigns targeting government and military organizations, APT28 would first conduct broad reconnaissance to identify externally facing web servers and network services. They used tools to fingerprint software versions, specifically looking for outdated versions of Microsoft Exchange, WordPress plugins, and VPN appliances.
This gathered intelligence was then used to launch tailored exploits, such as the CVE-2017-11882 Microsoft Office vulnerability, against organizations running the identified vulnerable software. This precision targeting, enabled by victim host information gathering, made their attacks far more effective than shotgun-style approaches.
Reference: Mandiant Report on APT28 Exploiting Office Vulnerabilities
The Defender's Handbook: Stopping Gather Victim Host Information
Blue Team Analogy & Detection Philosophy
Your job is not to prevent all looking (that's impossible), but to remove the useful signs. Imagine a secure facility where all equipment has generic labels, not model numbers. A spy can still see the building, but they can't tell if the lock is a 2015 model with a known flaw or a 2023 model with upgraded security. The defender's philosophy here is "information hygiene": minimize the useful data leakage from your public footprint.
SOC Reality Check: What to Look For
You won't see alerts titled "Software Information Gathering." Look for the noise that precedes an attack:
- High volume of probes from a single source to multiple services across your IP range on standard ports (80, 443, 22, 3389).
- Tools like Nmap have a signature. Look for SYN scans (`-sS`) followed by connection attempts to services.
- Web server logs showing requests to uncommon files and paths like `/version`, `/server-status`, `/wp-includes/`, or common exploit probe paths.
Note: This activity often blends with normal internet background noise (bots, researchers). Correlation with other suspicious events (e.g., a probe followed days later by a login attempt) is key.
Threat Hunter's Eye: Practical Query
Here is a Splunk SPL query to hunt for potential web software fingerprinting activity by looking for scans targeting common version disclosure paths across multiple hosts.
## Hunt: Potential Web Software Fingerprinting Scans ## Data Source: Web Server Access Logs (IIS, Apache, Nginx) index=web_logs sourcetype=access_* -- Look for requests to paths that reveal software/version info (uri_path="/server-status" OR uri_path="/phpinfo.php" OR uri_path="/wp-admin/" OR uri_path="*CHANGELOG*" OR uri_path="*version*" OR uri_path="*.git/*") -- Exclude common, legitimate single requests NOT (src_ip IN [10.0.0.0/8, 192.168.0.0/16]) | stats count(uri_path) as PathHits, values(uri_path) as PathsRequested, dc(dest_host) as UniqueHostsScanned by src_ip, _time -- Flag sources hitting multiple version-disclosure paths across multiple hosts | where PathHits > 5 AND UniqueHostsScanned > 3 | table _time, src_ip, UniqueHostsScanned, PathHits, PathsRequested
Key Data Sources for Detection
- Network Device Logs (Firewalls/IPS): For connection attempts to multiple ports from single IPs.
- Web Server Access Logs: Critical for spotting path enumeration and user-agent strings of scanning tools.
- Endpoint Detection & Response (EDR): Usually not applicable for this external reconnaissance, but vital for the next steps after a breach.
- DNS Query Logs: Can reveal subdomain enumeration attempts (another reconnaissance technique).
Building Resilience: Mitigation Strategies for Gather Victim Host Information
Actionable Mitigation Controls
Convert MITRE's generic advice into concrete actions:
- Minimize Version Disclosure:
- Configure web servers (Apache, Nginx, IIS) to remove or genericize the `Server` and `X-Powered-By` HTTP headers.
- Disable verbose error messages that reveal stack traces and framework versions to public users.
- Implement Robust Patch Management: This is the ultimate counter. If an adversary finds you're running Apache 2.4.49, but you patched to 2.4.51 last week, their intelligence is useless. Make timely updates a non-negotiable priority.
- Network Segmentation & Hardening: Limit external exposure. Does your database server really need to be reachable from the internet? Use firewalls and WAFs (Web Application Firewalls) to restrict access to management interfaces and sensitive paths.
- Vulnerability Scanning (Do It To Yourself): Regularly run passive and active scans against your own external footprint using the same tools attackers use (like Nmap, Nessus). You need to see what they see.
Red vs. Blue: A Quick Comparison
| Attacker's Goal (Red Team) | Defender's Action (Blue Team) |
|---|---|
| Identify specific software versions (e.g., WordPress 5.6.2). | Genericize headers and disable version disclosure in public responses. |
| Find unpatched vulnerabilities to exploit. | Implement a rigorous, accelerated patch management cycle for public-facing systems. |
| Map out the external attack surface efficiently. | Conduct regular external penetration tests and vulnerability assessments to find and shrink your own attack surface. |
| Stay undetected during the reconnaissance phase. | Monitor for scanning patterns and correlate low-severity events to build a picture of pre-attack activity. |
Gather Victim Host Information Cheat Sheet
🔴 Red Flag
A single external IP making sequential requests to `/server-status`, `/phpinfo.php`, `/wp-login.php`, and `/console/` across multiple web servers in a short time window. This is a classic fingerprinting scan.
🛡️ Blue's Best Move
Deploy a WAF rule or server configuration to strip detailed version headers (Server, X-AspNet-Version, X-Powered-By) from all external HTTP/S responses. This is a low-effort, high-impact hardening step.
🔍 Hunt Here
Your web server access logs are ground zero. Look for spikes in 404 errors for known technology paths, and use the Splunk hunting query provided above to find suspicious scanners.
Conclusion and Next Steps
Gather Victim Host Information: Software is the critical first domino in the attack chain. While it's a reconnaissance technique and doesn't directly cause damage, it enables every subsequent, more dangerous step. Defending against it isn't about complete prevention, but about raising the adversary's cost and uncertainty.
Your immediate next steps should be operational:
- Audit Your Headers: Use `curl -I` on your public websites right now. What version information are you giving away for free?
- Review Patching SLAs: How quickly are critical public-facing systems patched after a CVE for their software is published?
- Validate Detection: Run a harmless scan (with permission!) against a test external asset. Can your SIEM/WAF logs capture and alert on the activity using logic like the query provided?
Continue building your defensive knowledge by exploring related techniques:
- [Internal-Link: T1592.001 - Gather Victim Host Information: Hardware]
- [Internal-Link: T1589 - Gather Victim Identity Information]
For authoritative guidance on managing external attack surfaces, refer to the NIST Special Publication 800-40 Revision 4: Guide to Enterprise Patch Management Technologies.
Stay vigilant, practice good information hygiene, and remember: the best fight is the one the adversary decides isn't worth starting.
DONATE · SUPPORT
- Cyber Pulse Academy
- February 13, 2026
- No Comments


















































