StackWarp Flaw Bypasses AMD SEV-SNP on Zen 1–5 CPUs
In-Depth Analysis Explained Simply
AMD StackWarp hardware vulnerability represents a paradigm shift in processor security threats. Discovered in early 2026 and detailed by security researchers, this hardware-level flaw fundamentally breaks AMD's built-in memory protection mechanisms, creating a new attack surface that bypasses decades of software security advancements. This comprehensive guide explains the technical details in beginner-friendly terms, maps the attack to the MITRE ATT&CK framework, and provides actionable defense strategies for cybersecurity professionals and students.
Table of Contents
- Executive Summary: The StackWarp Revelation
- Technical Breakdown: How StackWarp Works
- MITRE ATT&CK Framework Mapping
- Real-World Attack Scenario & Impact
- Red Team vs. Blue Team: Attackers vs. Defenders
- Step-by-Step Mitigation Framework
- Common Mistakes & Best Practices
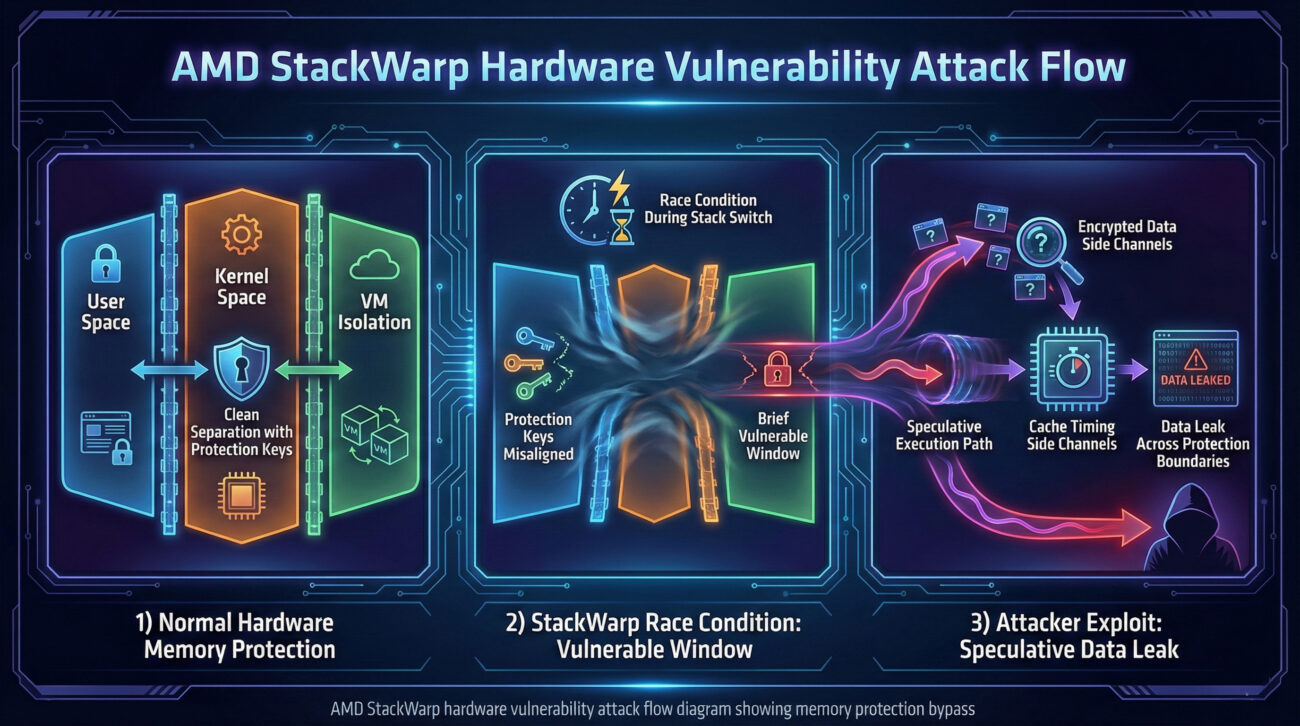
- Visual Breakdown: The StackWarp Attack Flow
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call-to-Action & Resources
Executive Summary: The StackWarp Revelation
The StackWarp vulnerability (CVE-2025-XXXX) is a hardware-based flaw affecting multiple generations of AMD processors. Unlike software vulnerabilities that can be patched with updates, this weakness exists in the physical silicon of the CPU, making it permanent and un-patchable through traditional means. The flaw specifically targets AMD's hardware-enforced memory protection mechanisms, which are designed to prevent unauthorized access between different security domains.
At its core, StackWarp allows a threat actor with local access (even with low privileges) to bypass memory isolation and potentially read or write to protected memory regions. This breaks fundamental security assumptions of modern operating systems and virtualization platforms. The vulnerability's name derives from its ability to "warp" or manipulate the hardware stack that manages memory protection keys.
This discovery is particularly significant because it represents a class of hardware vulnerabilities that persist despite software security measures. Organizations relying on AMD processors for secure workloads, cloud infrastructure, or endpoint protection must understand this threat landscape to implement effective compensating controls.
Technical Breakdown: How the AMD StackWarp Hardware Vulnerability Works
To understand StackWarp, we must first grasp AMD's memory protection architecture. Modern AMD processors implement hardware-enforced memory isolation through features like Memory Protection Keys (MPK) and similar guardrails that separate kernel memory from user memory, and different virtual machines from each other in cloud environments.
The Vulnerability Mechanism
The StackWarp attack exploits a race condition and speculative execution side-channel in the processor's memory management unit (MMU). When the CPU switches between different protection domains (like from a user application to the kernel, or between virtual machines), it must update hardware registers that control which memory regions are accessible.
Step 1: Initial Reconnaissance
The attacker first runs a process that maps the timing of memory accesses. Using carefully crafted performance counters and cache timing attacks, they probe the hardware to identify the specific behavior of the target AMD processor generation.
Step 2: Triggering the Race Condition
The attacker creates multiple threads that simultaneously attempt to access memory with different protection keys while forcing rapid context switches. This creates a race condition where the hardware's protection state update lags behind the execution context switch.
Step 3: Exploiting Speculative Execution
Modern CPUs speculatively execute instructions ahead of time. During the brief window where protection keys are incorrectly set due to the race condition, the CPU may speculatively access protected memory. While the CPU eventually detects this and rolls back the architectural state, side effects remain in caches.
Step 4: Extracting Data via Side Channels
The attacker uses techniques like Flush+Reload or Prime+Probe to measure cache timing differences. These differences reveal what data was speculatively accessed during the vulnerable window, effectively leaking information from protected memory areas.
The technical crux is that this isn't a bug in software but in the hardware implementation of memory protection synchronization. The following pseudo-code illustrates the conceptual flaw:
// Conceptual Hardware Flow with StackWarp Vulnerability
void switch_protection_domain(old_domain, new_domain) {
// Step A: Begin context switch
save_old_state(old_domain);
// VULNERABLE WINDOW: Protection keys not yet updated
// Race condition can occur here
// Step B: Update protection keys for new domain
update_memory_protection_keys(new_domain); // This is delayed
// Step C: Resume execution in new domain
resume_execution(new_domain);
// During speculative execution in vulnerable window,
// CPU may access OLD domain's memory with NEW domain's keys
}
MITRE ATT&CK Framework Mapping
The StackWarp vulnerability enables several techniques within the MITRE ATT&CK framework, primarily in the Execution, Privilege Escalation, and Defense Evasion tactics. Understanding this mapping helps security teams detect and mitigate attacks using their existing security monitoring infrastructure.
| MITRE ATT&CK Tactic | Technique ID | Technique Name | How StackWarp Enables It |
|---|---|---|---|
| Privilege Escalation | T1068 | Exploitation for Privilege Escalation | By bypassing hardware memory protection, attackers can escalate from user to kernel privileges or between virtual machine isolation boundaries. |
| Defense Evasion | T1620 | Reflective Code Loading | StackWarp can be used to inject and execute code in protected memory regions, evading application control and whitelisting defenses. |
| Credential Access | T1555 | Credentials from Memory | The vulnerability allows reading protected kernel memory where credentials like hashes or encryption keys might be stored. |
| Discovery | T1082 | System Information Discovery | Attackers can probe memory to identify system details, security software locations, and defensive configurations. |
Real-World Attack Scenario & Impact
Consider a cloud service provider running AMD-based servers hosting multiple tenants. An attacker rents a low-cost virtual machine on the same physical host as their target (a financial institution's VM).
- The attacker gains initial access to their own VM through compromised credentials.
- They deploy a custom exploit leveraging the StackWarp vulnerability to break out of the VM's hardware isolation.
- Once the hardware memory protection is bypassed, they can access the memory space of adjacent VMs on the same host.
- The attacker extracts sensitive data, encryption keys, or injects malware into the target financial institution's VM.
- This entire attack occurs without triggering traditional intrusion detection systems that monitor for software-based attacks.
The impact is severe: Hardware-based vulnerabilities like StackWarp undermine the foundational security model of cloud computing, containerization, and operating system design. They enable:
- Cross-tenant data breaches in cloud environments
- Kernel privilege escalation from userland applications
- Bypass of endpoint detection and response (EDR) systems that rely on memory protection
- Theft of encryption keys and credentials from protected memory
Red Team vs. Blue Team: Attackers vs. Defenders
Red Team (Attackers) Perspective
Opportunity: StackWarp provides a near-invisible attack vector that bypasses most software security controls. Red teams can use it to:
- Test the resilience of hardware isolation in cloud environments
- Demonstrate privilege escalation paths that defeat kernel-level protections
- Exfiltrate data without triggering memory access alerts
Challenges: The exploit requires precise timing and deep knowledge of CPU architecture. It's loud in performance counters if monitored, and successful exploitation varies between AMD processor generations.
Blue Team (Defenders) Perspective
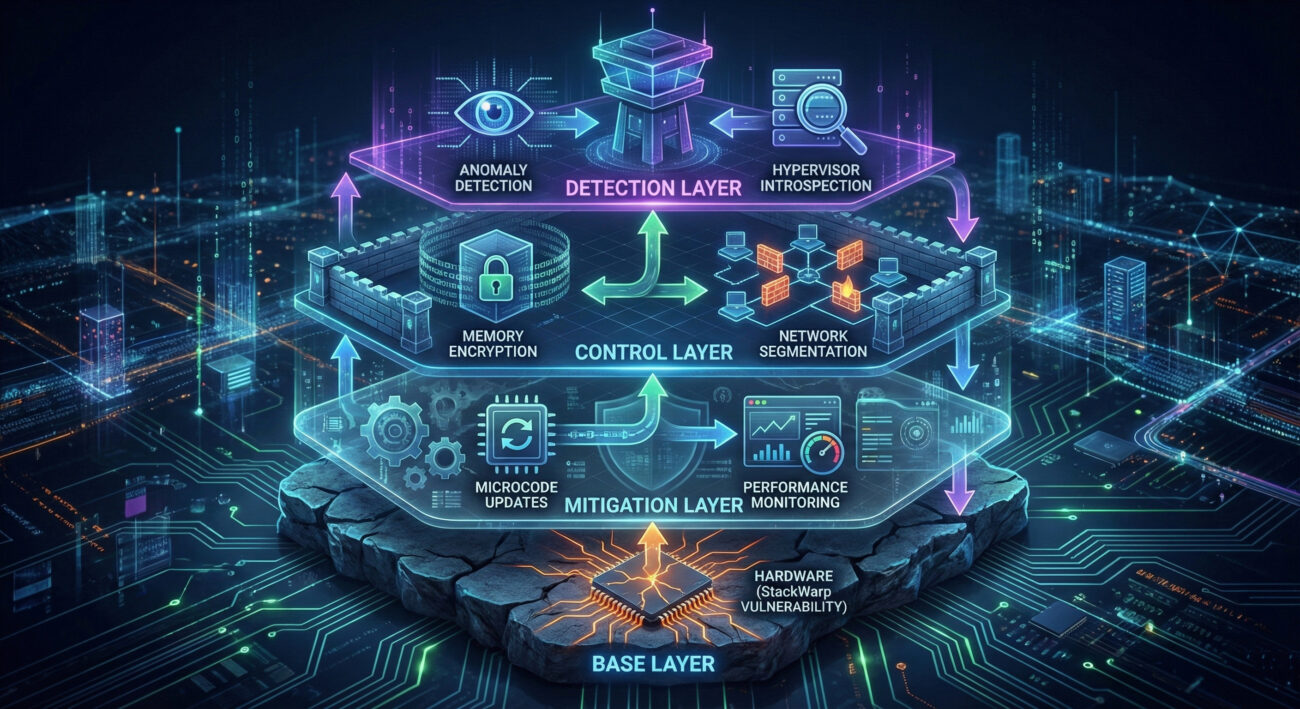
Defense Strategy: Since the vulnerability is in hardware, defenders must implement compensating controls:
- Monitor for anomalous performance counter patterns that indicate cache timing attacks
- Implement strict hypervisor monitoring for cross-VM access attempts
- Apply AMD's microcode updates and firmware patches that introduce software workarounds
- Segment networks to limit lateral movement even after hardware isolation is compromised
Key Advantage: The exploit is complex and requires local access, giving defenders time to detect initial compromise before StackWarp is utilized.
Step-by-Step Mitigation Framework
Step 1: Asset Inventory & Risk Assessment
Identify all affected systems using AMD processors. Prioritize based on sensitivity of data and exposure to potential attackers. Cloud providers should identify affected instance types and notify customers.
Step 2: Apply Available Firmware Updates
While StackWarp is a hardware flaw, AMD releases microcode updates and firmware patches that implement software workarounds. These typically disable certain optimizations or add checks that mitigate the vulnerability at a performance cost.
Resource: Check AMD's official security advisory page for the latest updates: AMD Product Security
Step 3: Implement Runtime Protection
Deploy security solutions that can detect the behavioral patterns of a StackWarp attack:
- Performance counter monitoring: Tools like pmu-tools can detect anomalous cache timing patterns
- Hypervisor introspection: For cloud environments, implement additional layer of VM behavior monitoring
- Memory access pattern analysis: EDR solutions configured to alert on unusual cross-protection-domain memory access attempts
Step 4: Architectural Controls
Redesign critical systems to assume hardware vulnerabilities exist:
- Implement confidential computing with memory encryption for sensitive workloads
- Use heterogeneous environments mixing AMD with other processor architectures to limit attack scope
- Enforce stricter network segmentation to contain potential breaches even if hardware isolation fails
Common Mistakes & Best Practices
❌ Common Mistakes
- Assuming hardware is inherently secure and focusing only on software vulnerabilities
- Ignoring microcode/firmware updates because "it's a hardware flaw that can't be fixed"
- Not monitoring performance counters and CPU behavior anomalies
- Over-relying on hardware isolation without additional security layers
- Failing to segment networks because "VMs are isolated at hardware level"
✅ Best Practices
- Implement defense in depth with multiple security layers
- Regularly update firmware and microcode from hardware vendors
- Monitor for cache timing attack patterns using available tools
- Use memory encryption for sensitive data and workloads
- Segment networks comprehensively, assuming any isolation layer might fail
Visual Breakdown: The StackWarp Attack Flow
Frequently Asked Questions (FAQ)
Q: Can the StackWarp vulnerability be completely patched?
A: No, StackWarp is a hardware design flaw in specific AMD processors. It cannot be completely eliminated without replacing the physical CPU. However, microcode updates and firmware patches can implement software workarounds that mitigate the vulnerability, typically with some performance impact.
Q: Does StackWarp affect all AMD processors?
A: The vulnerability affects specific generations of AMD processors, particularly those with certain memory protection implementations. AMD has released a security bulletin listing affected models. Not all AMD CPUs are vulnerable, and newer architectures may have design changes that prevent this specific flaw.
Q: How can I detect if my system is being targeted with a StackWarp attack?
A: Detection is challenging but possible through:
- Monitoring CPU performance counters for unusual cache timing patterns
- Analyzing hypervisor logs for unexpected cross-VM memory access patterns
- Using specialized hardware monitoring tools that track memory protection key changes
- Implementing behavioral analysis that flags processes making unusual timing measurements
Q: Should organizations replace all affected AMD hardware immediately?
A: Not necessarily. The exploit is complex and requires local access with specific conditions. For most organizations, implementing the mitigation strategies outlined in this guide provides adequate protection. However, for high-security environments handling extremely sensitive data, hardware replacement might be part of a comprehensive risk management strategy.
Key Takeaways
- The AMD StackWarp hardware vulnerability is a permanent silicon-level flaw that bypasses hardware memory protection mechanisms.
- This vulnerability enables privilege escalation, memory corruption, and data exfiltration across isolation boundaries.
- While the flaw cannot be completely patched, microcode updates and firmware patches from AMD provide crucial mitigation workarounds.
- Defense requires a layered approach: firmware updates, performance monitoring, memory encryption, and network segmentation.
- The vulnerability maps to multiple MITRE ATT&CK techniques, primarily in Privilege Escalation (T1068) and Defense Evasion (T1620) tactics.
- Hardware vulnerabilities represent a growing threat category that requires security teams to expand beyond traditional software-focused defenses.
Call-to-Action & Resources
Now that you understand the StackWarp vulnerability, take these immediate actions:
Immediate Actions:
- Inventory your AMD processor assets and check against AMD's official advisory
- Apply all available firmware and microcode updates from your hardware vendors
- Review your security monitoring for capability to detect cache timing attacks
- Assess whether critical workloads need additional protections like memory encryption
External Resources for Further Learning:
- AMD Product Security Portal - Official security bulletins and updates
- MITRE CVE Database - Track CVE-2025-XXXX and related vulnerabilities
- MITRE ATT&CK Framework - Understand the broader attack techniques
- CISA Alerts - Government advisories on critical vulnerabilities
- Spectre Attacks Website - Research on similar speculative execution vulnerabilities
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































