StealC Panel Flaw Let Researchers Monitor Hackers
Stealc Malware Panel Vulnerability Explained Simply
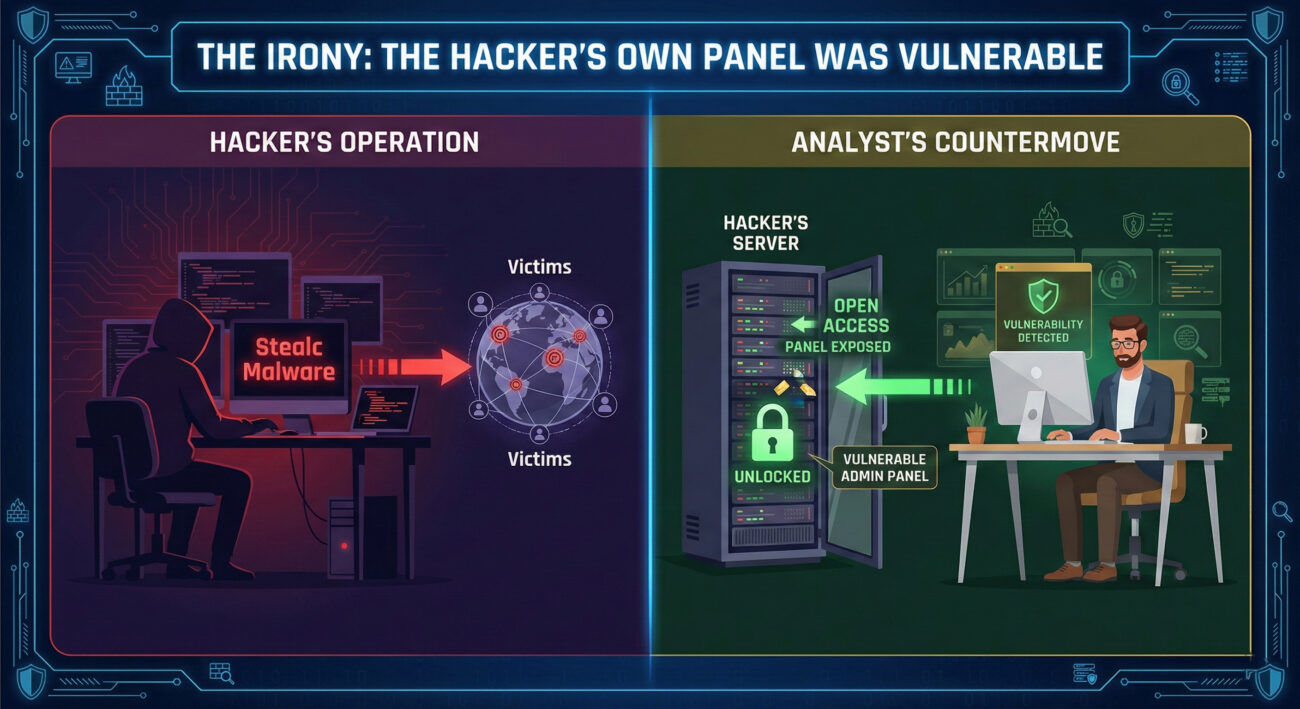
In a stunning twist of cyber irony, a significant security vulnerability was discovered not in a corporate firewall or a popular app, but within the very control panel used by hackers to manage the notorious Stealc information-stealing malware. This bug (CVE-2025-2022) essentially left the backdoor wide open, allowing cybersecurity researchers, and potentially defenders, to access the threat actors' own data, geolocate their servers, and even hijack their operations. This post provides a deep, beginner-friendly analysis of this vulnerability, its implications in the attack chain (mapped to MITRE ATT&CK), and the crucial lessons it teaches both red and blue teams about operational security.
Table of Contents
- Executive Summary: The Irony of a Hacker's Mistake
- Stealc Malware Background: A Modern Info-Stealer
- Technical Breakdown: The Panel Authentication Bypass (CVE-2025-2022)
- MITRE ATT&CK Mapping: From Initial Access to Exfiltration
- Real-World Scenario & Attack Flow
- Red Team vs. Blue Team Perspective
- Proactive Defense & Implementation Framework
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The Irony of a Hacker's Mistake
Imagine a thief who masterfully picks locks but forgets to lock their own vault. This is precisely what happened with the operators of the Stealc malware service. A critical vulnerability in their web-based command-and-control (C2) admin panel, discovered by researchers, allowed unauthorized access to the panel's data. This flaw didn't just leak technical data; it exposed the complete operational logs of the attackers, lists of infected victims, stolen credentials, cryptocurrency wallet details, and even the hackers' own server IP addresses.
The Stealc malware panel vulnerability is a profound lesson in operational security (OpSec). It demonstrates that cybercriminals, despite their technical prowess, often fall victim to the same security oversights they exploit in others. For defenders, it represents a rare opportunity for intelligence gathering and "hacking back" in a legal, ethical manner by analyzing exposed data to understand threat patterns.
Stealc Malware Background: A Modern Info-Stealer
Stealc is a sophisticated information-stealing malware distributed as a Malware-as-a-Service (MaaS). First identified in early 2023, it quickly became popular in the cybercrime underworld due to its efficiency, user-friendly panel, and comprehensive data theft capabilities. It is designed to harvest a wide array of sensitive information from infected Windows machines.
What Stealc Steals:
- Saved credentials from browsers (Chrome, Edge, Firefox, etc.)
- Autofill data, cookies, and browsing history
- Cryptocurrency wallet files and related information
- FTP client credentials and configuration files
- Telegram and Discord session tokens
- System information and screenshots
The stolen data is exfiltrated to a command-and-control (C2) server controlled by the threat actor. The actor then accesses a web-based admin panel to view, manage, and monetize the loot from their victims. It was this very admin panel that contained the critical vulnerability.
Technical Breakdown: The Panel Authentication Bypass (CVE-2025-2022)
The core of the Stealc malware panel vulnerability was a broken authentication mechanism in the PHP-based web panel. The panel's access control logic was fundamentally flawed, allowing unauthorized users to bypass login checks and directly access administrative endpoints.
How the Vulnerability Worked (Step-by-Step)
Step 1: The Flawed Login Check
The panel's PHP code likely included a file (e.g., auth_check.php) that was supposed to run on every protected page to verify if a user was logged in. The bug was that this check could be circumvented if the script incorrectly validated session variables or user roles.
Step 2: Direct Access to API/Admin Routes
Researchers discovered that by directly navigating to specific URLs (e.g., /panel/admin/victims.php or API endpoints like /api/getLogs) without a valid session, the panel would still return sensitive data. This is a classic Missing Authentication vulnerability.
Step 3: Exploitation and Data Exposure
By exploiting this, an unauthenticated attacker (in this case, a security researcher) could access:
- A full list of infected victim IDs and machine information.
- Logs of all stolen data (credentials, wallets, etc.).
- Panel configuration, revealing the server's file paths and IP addresses.
- Statistics about the malware's success rate.
Simplified Code Example of the Flaw
Below is a simplified, hypothetical representation of the flawed logic, not the actual Stealc code.
// FILE: victims.php - THE VULNERABLE VERSION
<?php
// INTENDED: Include authentication check
// include('auth_check.php'); // THIS LINE WAS INEFFECTIVE OR MISSING
// DIRECT DATABASE QUERY WITHOUT PROPER AUTH
$query = "SELECT * FROM stolen_data";
$result = $conn->query($query);
// Output all stolen data as JSON
echo json_encode($result->fetch_all(MYSQLI_ASSOC));
?>
The correct version should have enforced a strict authentication check before any database interaction.
MITRE ATT&CK Mapping: From Initial Access to Exfiltration
Understanding where this panel vulnerability fits into the broader attack lifecycle is crucial. We can map the Stealc malware operation and the subsequent panel compromise to specific MITRE ATT&CK tactics and techniques.
| MITRE ATT&CK Tactic | Technique Code & Name | How It Applies to Stealc Operations |
|---|---|---|
| Initial Access | T1566.001 Phishing: Spearphishing Attachment |
Stealc is often delivered via phishing emails with malicious attachments (e.g., DOCX, PDF) containing downloaders. |
| Execution | T1204.002 User Execution: Malicious File |
The victim executes the malicious attachment, triggering the malware installation. |
| Collection | T1555 Credentials from Password Stores |
Stealc's primary function: harvesting credentials from browser storage and system files. |
| Command and Control | T1071.001 Application Layer Protocol: Web Protocols |
Stealc uses HTTP/HTTPS to communicate with its C2 server (the panel's backend). |
| Exfiltration | T1041 Exfiltration Over C2 Channel |
Stolen data is sent back to the attacker over the same C2 channel. |
| Discovery (Against Attackers) | T1087 Account Discovery |
The panel vulnerability allowed defenders to discover attacker accounts and victim lists. |
| Collection (Against Attackers) | T1530 Data from Cloud Storage |
Researchers collected attacker data from the poorly secured panel (acting as a cloud service). |
Real-World Scenario & Attack Flow
Let's walk through a complete scenario showing both the threat actor's intended flow and how the panel vulnerability interrupted it.
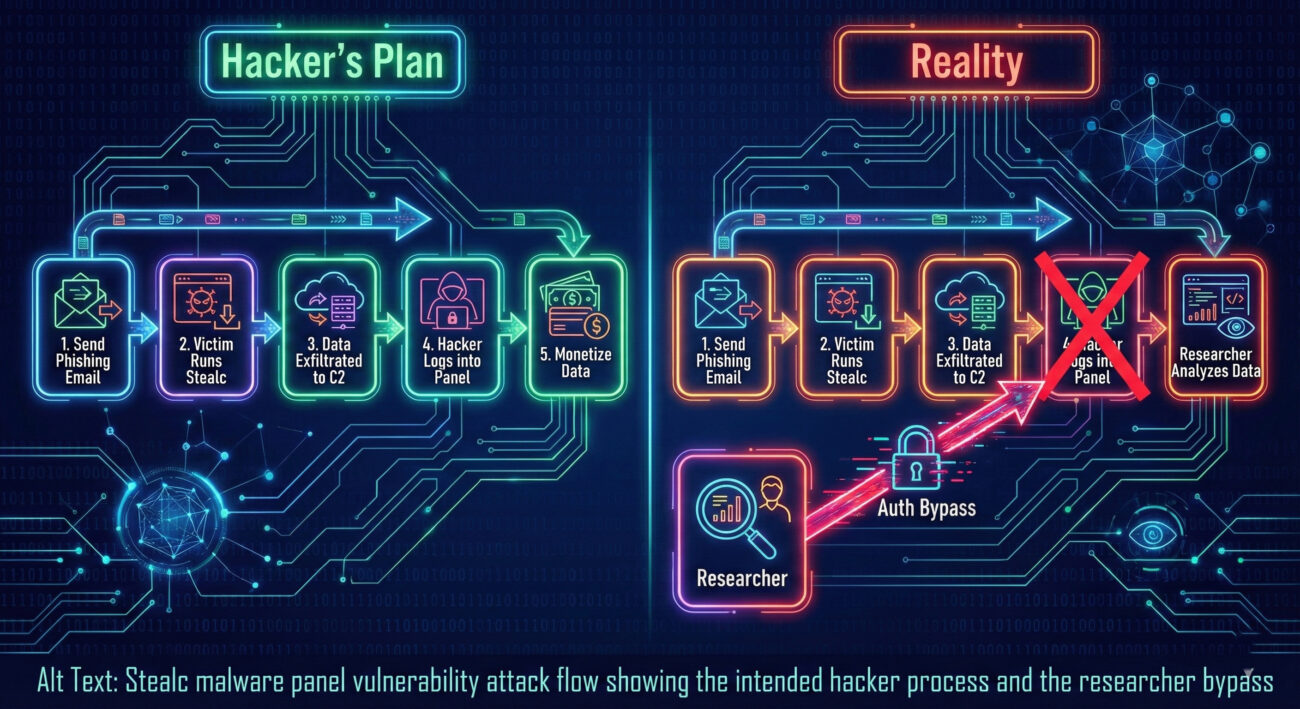
The Defender's Opportunity
Upon discovering an active Stealc C2 server (e.g., through threat intelligence feeds or malware sandbox logs), a defender could:
- Test for the known panel vulnerability by accessing common panel paths.
- If vulnerable, collect intelligence: IP addresses, victim identifiers, types of stolen data.
- Use this information to:
- Notify potential victims whose identifiers are visible.
- Submit attacker infrastructure details to blocklists.
- Enrich internal security analytics with the latest threat indicators (IOCs).
Red Team vs. Blue Team Perspective
Red Team / Threat Actor View
The Critical OpSec Failure: For red teams and ethical hackers, this incident is a masterclass in what NOT to do in operational security.
- Overconfidence in Stealth: Assuming your attack tools are the only point of vulnerability is a fatal mistake. Your management infrastructure is equally critical.
- Lack of Secure Development: The panel was likely developed quickly without secure coding practices (input validation, proper auth). Red teams must ensure any custom C2 tools are rigorously tested.
- Poor Network Segmentation: The C2 panel was directly exposed and linked to the core data repository. Segregating the panel backend from the main data store could have limited the blast radius.
Blue Team / Defender View
The Intelligence Windfall: For blue teams, this vulnerability is a reminder to think creatively about defense.
- Active Threat Intelligence: Proactively hunt for and test known adversary infrastructure for misconfigurations. Resources like urlscan.io or Shodan can help find exposed panels.
- Legal "Counter-Intelligence": Accessing such data must be done carefully, within legal boundaries, often in collaboration with law enforcement or as part of sanctioned research.
- IOC Enrichment & Victim Notification: The exposed data is a goldmine for extracting IOCs (IPs, hashes, domains) to block and potentially identifying other victims to warn.
Proactive Defense & Implementation Framework
How can organizations leverage lessons from the Stealc malware panel vulnerability? Here’s a practical framework.
1. Enhance Endpoint Protection
- Deploy advanced Endpoint Detection and Response (EDR) solutions that can recognize information-stealer behaviors (e.g., mass credential access from browser paths).
- Use application allowlisting to prevent unauthorized executables, common with malware droppers.
2. Implement Robust Network Monitoring
- Monitor outbound traffic for connections to known-bad IPs (from threat intel feeds) and anomalous data uploads to unknown domains.
- Utilize tools like Zeek (Bro) or commercial NDR platforms to baseline normal traffic and flag C2-like communication.
3. Foster Threat Intelligence
- Subscribe to reliable threat intelligence sources that provide IOCs for active stealers like Stealc.
- Consider participating in trusted Information Sharing and Analysis Centers (ISACs).
4. User Education & Phishing Defense
Since Stealc often arrives via phishing, regular, engaging security awareness training is non-negotiable. Simulated phishing campaigns help gauge resilience.
Common Mistakes & Best Practices
Common Mistakes (Learn from the Attackers)
- Neglecting OpSec for Attack Infrastructure: Treating your C2 servers and panels as disposable without hardening them.
- Using Default or Weak Credentials for admin panels (a related common issue).
- Failing to Update and Patch self-developed tools, assuming they are "safe by obscurity".
- Exposing Admin Interfaces Directly to the Internet without a VPN or strict IP allowlisting.
- Lack of Logging and Monitoring on their own systems to detect unauthorized access.
Best Practices for Defenders
- Assume Breach & Hunt Proactively: Regularly hunt for IOCs and anomalous behavior inside your network.
- Implement Multi-Factor Authentication (MFA) universally, especially for all administrative access.
- Follow the Principle of Least Privilege: Ensure users and systems have only the access they absolutely need.
- Maintain an Updated Incident Response (IR) Plan that includes procedures for dealing with info-stealer infections.
- Encrypt Sensitive Data at Rest: While Stealc can harvest decrypted data, full-disk encryption raises the barrier for physical theft.
Frequently Asked Questions (FAQ)
Q1: Is it legal to "hack back" by accessing a vulnerable malware panel like this?
A: This is a complex legal area. Actively exploiting the vulnerability to disrupt, delete, or modify data is almost certainly illegal in most jurisdictions. However, passive reconnaissance, accessing publicly exposed information without authentication, is often analyzed on a case-by-case basis. The safest approach for organizations is to collect intelligence and immediately report the findings to law enforcement (e.g., the FBI's IC3 or similar). Security researchers often operate under responsible disclosure protocols.
Q2: How can I check if my organization has been infected by Stealc?
A: Look for these indicators:
- Unusual outbound network connections to unknown IPs on ports 80/443.
- EDR/AV alerts for known Stealc file hashes or behaviors (check resources like Malpedia).
- Unexplained loss of saved browser passwords or cryptocurrency wallet files.
Q3: Does this vulnerability mean Stealc is no longer a threat?
A: Absolutely not. The vulnerability was in the attacker's panel, not in the malware itself. Stealc binaries remain fully functional. Furthermore, only some panels may have been exposed or unpatched. The threat from information stealers is more prevalent than ever.
Q4: What's the main cybersecurity lesson from this event?
A: Operational security is paramount for everyone, including attackers. For defenders, it reinforces that adversaries are not infallible; their tools and infrastructure can contain critical flaws that provide valuable defensive intelligence. Always practice defense-in-depth.
Key Takeaways & Call to Action
Summary of Key Points
- The Stealc malware panel vulnerability (CVE-2025-2022) was a severe authentication bypass in the hacker's own management interface.
- It allowed unauthorized access to victim data, attacker logs, and server information, providing a treasure trove of threat intelligence.
- The incident maps to MITRE ATT&CK tactics, highlighting both the attacker's techniques and the defender's opportunity for discovery.
- It serves as a critical lesson in OpSec for red teams and a case study in proactive intelligence gathering for blue teams.
- Defense against info-stealers requires layered security: EDR, network monitoring, user training, and robust credential management.
Your Call to Action
Don't wait to become a statistic. Use this incident as a catalyst to review your organization's defenses against information-stealing malware.
- Audit your endpoints for signs of compromise using the latest Stealc IOCs.
- Review your external threat intelligence sources and ensure they cover MaaS operations.
- Train your team on phishing identification and the dangers of executing unknown files.
- Consider implementing a password manager with MFA to reduce the impact of credential theft from browsers.
Cybersecurity is a continuous battle of adaptation. By learning from both our mistakes and the mistakes of our adversaries, we build a more resilient digital world.
External Resources & Further Reading:
- MITRE ATT&CK Framework v14 - The definitive knowledge base for adversary tactics.
- CISA Known Exploited Vulnerabilities Catalog - Track actively exploited flaws.
- AlienVault OTX - Open Threat Intelligence exchange.
- Have I Been Pwned - Check if your credentials have been exposed in breaches (like those stolen by Stealc).
- The Hacker News - For daily cybersecurity news and updates.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































