Stop AI-Generated Default Credentials Now
The Botnet Threat Explained Simply
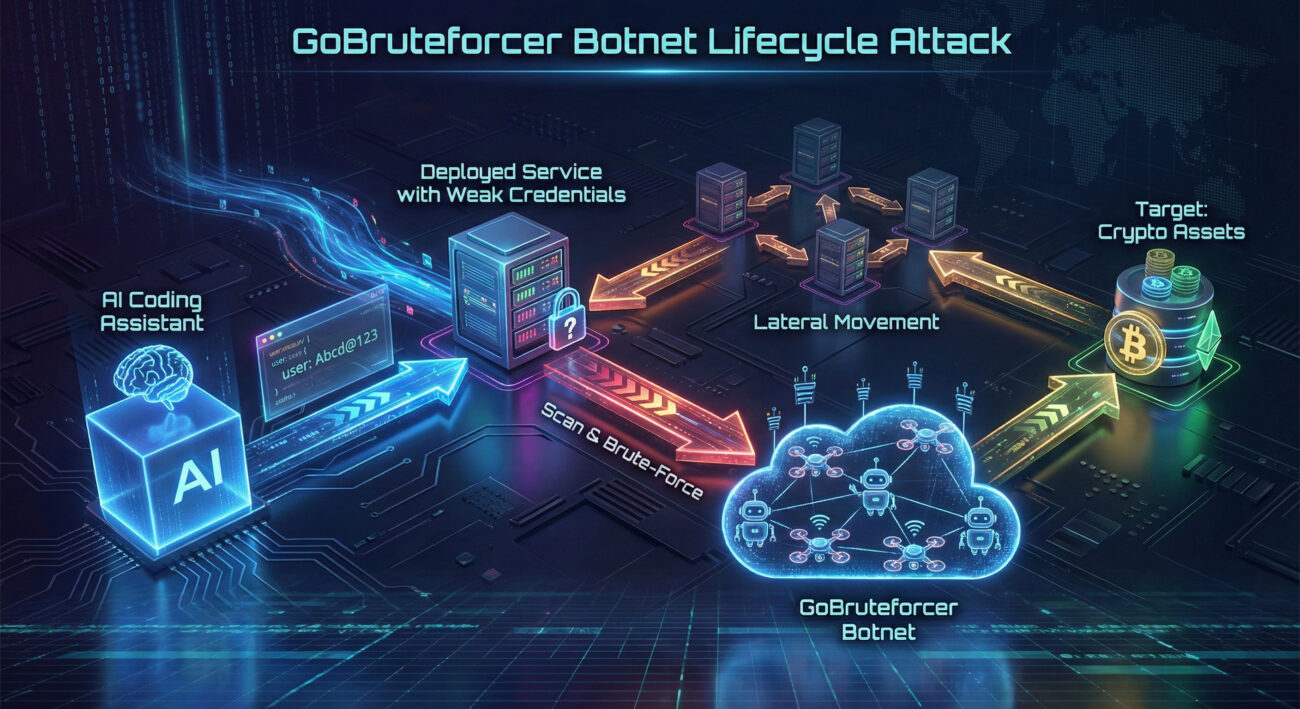
A new, sophisticated wave of cyberattacks is exploiting an unexpected vulnerability: the default credentials found in AI-generated code snippets. The GoBruteforcer botnet is systematically targeting cryptocurrency projects and other online services by brute-forcing passwords that were never meant to be used in production. This campaign highlights a critical intersection between modern development practices and classic security failures, turning helpful AI coding assistants into an unwitting accomplice for cybercriminals.
Table of Contents
- The Attack Lifecycle: From AI Suggestion to Botnet Node
- Technical Deep Dive & MITRE ATT&CK Mapping
- The Root Cause: The AI-Generated Default Credentials Problem
- Defense Framework: A Step-by-Step Guide to Protection
- Red Team vs. Blue Team Perspective
- Common Mistakes & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
The Attack Lifecycle: From AI Suggestion to Botnet Node
Understanding the GoBruteforcer campaign requires seeing it not as a single attack, but as a ruthless automation of a common oversight. The cycle begins long before the first malicious connection attempt, rooted in the way we now develop software.
Phase 1: The Poisoned Seed (AI-Generated Defaults)
Developers and admins often use AI tools to quickly generate configuration examples or deployment scripts for services like FTP servers, MySQL, or phpMyAdmin. These models are trained on vast datasets of public code, tutorials, and vendor documentation, which frequently contain placeholder credentials like myuser:Abcd@123 or admin:admin123456. The AI dutifully reproduces these weak defaults. When a developer copies this code without changing the credentials, they plant a poisoned seed in their infrastructure.
Phase 2: The Automated Hunt (Scanning & Bruteforcing)
The GoBruteforcer botnet, a network of previously compromised machines, constantly scans the internet for exposed services (FTP, MySQL, PostgreSQL, phpMyAdmin). It uses highly targeted wordlists that are curated from the same pool of AI-generated and tutorial default credentials. This includes crypto-specific usernames like "cryptouser" or "appcrypto," making blockchain projects a prime target. The botnet's efficiency comes from this focused intelligence on what credentials are likely to be in use.
Phase 3: Infection & Botnet Recruitment
Once successful, the attacker uploads a PHP web shell (like those often left in vulnerable XAMPP stacks) to the compromised host. This shell downloads and executes the core GoBruteforcer malware, a Golang-based IRC bot. This gives the attacker persistent remote access and enrolls the server into the botnet for one of three purposes:
- To run the brute-force module and scan for more victims.
- To act as a payload host, serving malware to other compromised systems.
- To function as a resilient command-and-control (C2) node for the IRC botnet.
Phase 4: The Ultimate Objective
While the botnet can be used for various purposes, Check Point Research observed a module designed to query balances of TRON blockchain addresses. This indicates a direct financial motive: identifying and likely later targeting cryptocurrency wallets with funds. The initial breach via weak credentials becomes a stepping stone to potential asset theft.
Technical Deep Dive & MITRE ATT&CK Mapping
The GoBruteforcer botnet is a masterclass in pragmatic, low-sophistication malware that achieves high impact. Its technical components map clearly to the MITRE ATT&CK framework, a globally recognized knowledge base of adversary tactics.
Malware Evolution & Capabilities
Since its discovery in 2023, GoBruteforcer has evolved. The newer variants analyzed in 2025 are written in Go (Golang), making them cross-platform (targeting x86, x64, ARM) and harder to analyze. Key features include:
- Heavy Obfuscation: The IRC bot code is obfuscated to evade signature-based detection.
- Improved Persistence: Uses mechanisms to ensure it survives reboots on the infected Linux server.
- Process Masking: Hides its running processes to avoid detection by system administrators.
- Dynamic Credential Lists: The wordlists for brute-forcing are fetched and updated regularly, allowing attackers to rotate targets.
Mapping to MITRE ATT&CK
This table breaks down the GoBruteforcer attack chain using the MITRE ATT&CK framework, providing a common language for defenders to understand and counter the threat.
| MITRE Tactic | MITRE Technique | GoBruteforcer Implementation |
|---|---|---|
| Reconnaissance | T1595: Scanning IP Blocks | Botnet nodes scan the internet for open ports 21 (FTP), 3306 (MySQL), 5432 (PostgreSQL), and 80/443 (web panels). |
| Initial Access | T1110: Brute Force | Uses targeted wordlists of AI-generated and common default credentials to gain access to services. |
| Execution | T1059.004: Command and Scripting Interpreter (Unix Shell) | Executes downloaded shell scripts to deploy the malware based on system architecture (x86, ARM). |
| Persistence | T1543.002: Systemd Service | Installs itself as a system service on Linux to restart automatically after a reboot. |
| Command & Control | T1132.001: Standard Encoding (IRC) | Uses Internet Relay Chat (IRC), a legacy but effective protocol, for covert communication with operators. |
The Root Cause: The AI-Generated Default Credentials Problem
This campaign exposes a profound systemic risk. The attackers are not guessing; they are strategically exploiting known, predictable weaknesses that AI tools are inadvertently standardizing.
Large Language Models (LLMs) are trained on publicly available data. When countless tutorials and vendor docs use "admin/admin" or "root/12345" as examples, the model learns these as plausible answers. A developer asking, "Show me an example of an FTP config," will receive functional code with these insecure placeholders. The urgency to deploy often overrides the basic security step of changing them.
Furthermore, threat actors are now scanning for misconfigured LLM endpoints and AI tooling itself. As noted in the original report, separate campaigns are hunting for exposed proxy servers that could grant unauthorized access to commercial AI APIs from providers like OpenAI and Anthropic. This creates a dangerous feedback loop: AI tools that leak access can be abused to generate more malicious code or data, while the code they produce creates more vulnerabilities to scan for.
Defense Framework: A Step-by-Step Guide to Protection
Defending against threats like GoBruteforcer requires moving beyond simple advice. Here is a actionable, step-by-step framework to build resilience.
Step 1: Immediate Credential Hygiene
Action: Audit all internet-facing services (FTP, databases, admin panels) for default or weak credentials. Tools: Use offline password managers like KeePass or Bitwarden to generate and store unique, complex passwords for every service. Enforcement: Implement a policy that absolutely prohibits the use of credentials found in tutorials or AI-generated code snippets in any production or test environment.
Step 2: Harden Exposed Services & Reduce Attack Surface
Action: Do not expose management interfaces (phpMyAdmin, FTP) directly to the internet. Solution: Place them behind a VPN or use a secure bastion host (jump server). For legacy stacks like XAMPP, assume they are for development only and never deploy them in production. Use cloud provider firewall rules or tools like Fail2ban to block IPs after repeated failed login attempts.
Step 3: Proactive Monitoring & Detection
Action: Assume some scanning will get through, so you must detect intrusion attempts. Tools: Deploy an Intrusion Detection System (IDS) like Snort or Suricata with rules tuned to detect brute-force patterns and IRC traffic from servers (which is almost always malicious). Monitor system logs for unusual process creation or network connections to unfamiliar IPs.
Step 4: Implement a Secure Development Lifecycle (SDL)
Action: Integrate security checks into your CI/CD pipeline. Tools: Use Secrets Detection tools like Gitleaks or TruffleHog to scan every code commit for accidentally committed passwords or default credentials. Use Infrastructure as Code (IaC) scanning tools to check for insecure configurations in deployment templates before they are ever provisioned.
Red Team vs. Blue Team Perspective
Red Team / Threat Actor View
- Objective: Maximize return on investment (ROI) by exploiting the lowest-hanging fruit, widespread, known default credentials.
- Strategy: Weaponize convenience. Target credentials that developers find convenient to copy-and-paste from AI and tutorials. There's no need for zero-days when "Abcd@123" is so common.
- Tooling: Use adaptable, modular malware (like the Go-based bot) that can be updated with new credential lists as trends change. Leverage compromised hosts as infrastructure to make takedowns difficult.
- Success Metric: Number of new bots recruited; number of high-value targets (like crypto wallets) discovered through compromised infrastructure.
Blue Team / Defender View
- Objective: Eliminate the easy wins for the attacker by enforcing credential hygiene and reducing the attack surface.
- Strategy: Assume breach and deny foothold. Even if a service is exposed, strong, unique credentials and network segmentation should prevent a single compromise from leading to a catastrophic breach.
- Tooling: Deploy multi-factor authentication (MFA) everywhere possible. Use privileged access management (PAM) solutions to control and audit access to critical systems. Implement robust logging and SIEM solutions for correlation and alerting.
- Success Metric: Reduction in brute-force alert noise; zero findings of default credentials in routine audits; rapid detection and containment of any anomalous activity.
Common Mistakes & Best Practices
❌ Common Mistakes to Avoid
- Blindly trusting AI-generated code for production configuration without a thorough security review.
- Exposing development or database administration interfaces (phpMyAdmin, Adminer) directly to the public internet.
- Using the same password across different services or environments (development, staging, production).
- Assuming that because a server is "just a test" or "internal," it doesn't need strong security measures.
- Focusing only on perimeter defense and not monitoring for anomalous activity inside the network once a foothold is gained.
✅ Best Practices to Implement
- Treat credentials as secrets: Store all passwords, API keys, and tokens in a dedicated vault (Hashicorp Vault, AWS Secrets Manager) and never in code or config files.
- Enforce Zero Trust principles: Verify explicitly, grant least-privilege access, and assume the network is hostile. Use network segmentation to isolate critical assets.
- Mandate the use of Multi-Factor Authentication (MFA) for all administrative access, without exception.
- Conduct regular, automated vulnerability scans and penetration tests that specifically include checks for default credentials and misconfigurations.
- Establish and practice a clear incident response plan so your team knows how to quickly isolate a compromised host and investigate the scope of a breach.
Frequently Asked Questions (FAQ)
Q: Is using an AI coding assistant inherently insecure?
A: No, the tool is not insecure, but how we use it can be. The risk lies in accepting its output without critical review, especially for security-sensitive configurations like credentials and network settings. Treat AI as a junior developer who is brilliant but has memorized every bad example from the internet, always audit its code.
Q: My service is behind a firewall and only accessible on a private IP. Am I safe from GoBruteforcer?
A: You are safe from external internet scans. However, if the botnet or similar malware gets inside your network (e.g., via a phishing email), it can then perform the same brute-force attacks internally. This is why internal network segmentation and strong credentials are critical even for private services.
Q: What's the single most effective thing I can do to prevent this type of attack?
A: Beyond using strong passwords, implement MFA (Multi-Factor Authentication). If MFA is not supported by the service (like some legacy FTP servers), the next best step is to not expose it to the internet at all. Use a VPN as a gateway to access it. This single change nullifies the entire internet-scale scanning approach used by GoBruteforcer.
Key Takeaways & Call to Action
The GoBruteforcer campaign is a stark reminder that the most potent threats often exploit the simplest oversights. The automation of default credential attacks, fueled by the unintended consequences of AI-generated code, represents a significant shift in the threat landscape.
Core Lessons:
- The Attack Vector is Now Programmatic: Weak credentials are no longer just a human error; they are being systematically propagated by AI and systematically exploited by botnets.
- Security Must Keep Pace with Development Speed: The convenience of AI-assisted coding demands an equal or greater investment in automated security review and hardening.
- Resilience Beats Perfect Prevention: Since total prevention is impossible, building systems that detect and contain breaches quickly (through MFA, segmentation, and monitoring) is essential.
Your Call to Action:
This week, perform one critical action:
- Choose one internet-facing service you manage (a server, a database, a router).
- Change its password to a long, random passphrase from a password manager.
- Check its access logs for the past 30 days. Look for failed login attempts from unfamiliar IP addresses.
- If it's an admin panel, research how to put it behind a VPN or enable MFA.
By taking this step, you're not just securing one service; you're actively dismantling the business model of automated botnets like GoBruteforcer. Share this knowledge with your team and make credential hygiene a non-negotiable part of your development and operations culture.
For further reading on secure configuration, consult the NIST Cybersecurity Framework and the OWASP Top Ten for web application security.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































