Lotus Blossom’s Notepad++ Supply Chain Attack: A Deep Dive into the Chrysalis Backdoor

In mid-2025, the Lotus Blossom hacking group breached Notepad++’s hosting provider, hijacking update traffic to deliver the Chrysalis backdoor. This beginner-friendly post breaks down the attack flow, maps MITRE ATT&CK techniques, and provides red/blue team insights to help you defend against similar supply chain threats.
341 Malicious ClawHub Skills Exposed in OpenClaw Supply Chain Attack

Security researchers uncovered 341 malicious skills on ClawHub, an OpenClaw marketplace, distributing Atomic Stealer malware via fake prerequisites. This post explains the attack, its impact, and how to defend.
LinkedIn Messages Deliver Malware Via DLL Sideloading

In a disturbing evolution of social engineering, hackers have turned the world’s largest professional network into a weapon. A sophisticated new LinkedIn malware attack campaign is actively targeting professionals by weaponizing seemingly legitimate LinkedIn messages to deliver dangerous malware payloads. This attack bypasses traditional email phishing defenses by leveraging the inherent trust and professional context of LinkedIn communications.
Malicious Chrome extension spreads ModeloRAT via fake crash lures.

In the ever-evolving landscape of cyber threats, a new, sophisticated form of attack has emerged, exploiting one of the most trusted components of our daily digital routine: the browser extension. The recent “CrashFix” campaign represents a dangerous escalation in social engineering, weaponizing user frustration and trust in legitimate software to deploy a powerful Remote Access Trojan (RAT). This malware, known as ModeloRAT, grants threat actors complete control over compromised systems, turning a simple search for an ad blocker into a catastrophic corporate breach.
StealC Panel Flaw Let Researchers Monitor Hackers

In a stunning twist of cyber irony, a significant security vulnerability was discovered not in a corporate firewall or a popular app, but within the very control panel used by hackers to manage the notorious Stealc information-stealing malware. This bug (CVE-2025-2022) essentially left the backdoor wide open, allowing cybersecurity researchers, and potentially defenders, to access the threat actors’ own data, geolocate their servers, and even hijack their operations. This post provides a deep, beginner-friendly analysis of this vulnerability, its implications in the attack chain (mapped to MITRE ATT&CK), and the crucial lessons it teaches both red and blue teams about operational security.
LOTUSLITE Backdoor Targets U.S. Policy Groups with Venezuela-Themed Phishing

In the shadowy world of cyber espionage, a new and sophisticated tool has emerged, specifically targeting a sensitive sector: U.S. foreign policy research organizations, or “think tanks.” Dubbed the LotusLite backdoor, this malware represents a significant threat due to its stealth, persistence, and targeted nature. This blog post will dissect this threat, explain its inner workings in beginner-friendly terms, and provide a concrete defense blueprint for cybersecurity professionals and students alike.
Attackers Abuse c-ares DLL Side-Loading Vulnerability to Evade Defenses and Deploy Malware

In the ever-evolving landscape of cybersecurity, attackers continuously refine their tradecraft, seeking the path of least resistance. One of the most persistent and effective techniques involves abusing trusted Windows mechanisms to bypass security controls. The recent exploitation of the popular c-ares DNS library via a DLL side-loading attack is a textbook example of this threat. This post will dissect this attack vector, explain its mechanics in beginner-friendly terms, and provide actionable defense strategies.
New Malware Campaign Delivers Remcos RAT Through Multi-Stage Windows Attack

A new and sophisticated malware campaign delivering the Remcos RAT (Remote Access Trojan) has emerged as a significant threat to organizations worldwide. This campaign represents an evolution in delivery techniques, leveraging clever social engineering and multi-stage payload deployment to bypass traditional security measures. The latest Remcos RAT malware campaign primarily targets corporate networks through phishing emails containing malicious attachments, demonstrating how threat actors continue to refine their approaches.
WhatsApp Worm Spreads Astaroth Banking Trojan Across Brazil via Contact Auto-Messaging
In early 2026, a sophisticated WhatsApp worm attack demonstrated a dangerous evolution in cybercrime, turning the world’s most popular messaging app into a vehicle for a devastating banking trojan. This campaign, primarily targeting Brazil, leveraged human trust and automated messaging to spread the notorious Astaroth malware (also known as Guildma).
China-Linked UAT-7290 Targets Telecoms with Linux Malware and ORB Nodes
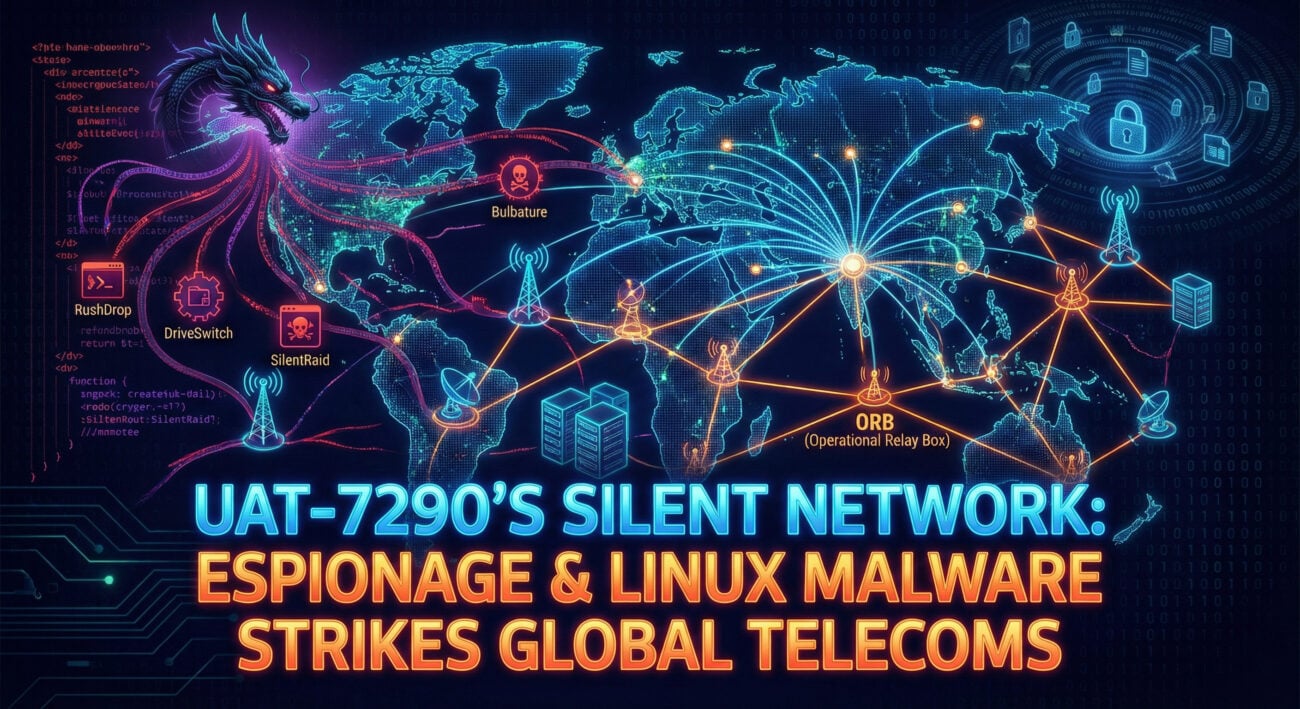
In the complex landscape of modern cyber-espionage, the UAT-7290 telecom attack stands out as a sophisticated and multi-faceted campaign. Targeting critical telecommunications infrastructure in South Asia and Southeastern Europe, this threat actor leverages a unique blend of Linux-based malware and the creation of secret Operational Relay Box (ORB) networks. For cybersecurity professionals and beginners alike, understanding this attack is crucial, as it reveals how state-aligned groups burrow deep into networks not just to steal secrets, but to build infrastructure for future attacks by other actors.











































