Notepad++ Update Hijack: Critical Supply Chain Attack Exposed

In February 2026, Notepad++ revealed a sophisticated supply chain attack where the official update mechanism was hijacked to deliver malware to selected users. This post breaks down the attack flow, MITRE ATT&CK mapping, and essential defenses for developers and security teams.
New Advanced Linux VoidLink Malware Targets Cloud and container Environments

In the ever-evolving landscape of cyber threats, a new sophisticated adversary has emerged targeting the backbone of modern IT: Linux servers. Dubbed VoidLink, this advanced malware represents a significant leap in the attack capabilities of threat actors focusing on high-value, critical infrastructure and corporate networks. This guide provides a comprehensive, beginner-friendly breakdown of the VoidLink Linux malware, explaining its inner workings, mapping its techniques to the MITRE ATT&CK framework, and delivering actionable defense strategies for cybersecurity professionals and students alike.
What Should We Learn From How Attackers Leveraged AI in 2025?
The most effective cybersecurity strategy doesn’t just build walls; it studies the attackers trying to climb them. To truly learn from attacker techniques is to undergo a fundamental mindshift, from reactive patching to proactive anticipation. This approach is crystallized in frameworks like MITRE ATT&CK, which provides a standardized encyclopedia of adversary behavior. By understanding how threat actors operate, from initial access to data exfiltration, defenders can transform their security posture from fragile to resilient.
VS Code Forks Recommend Missing Extensions, Creating Supply Chain Risk in Open VSX
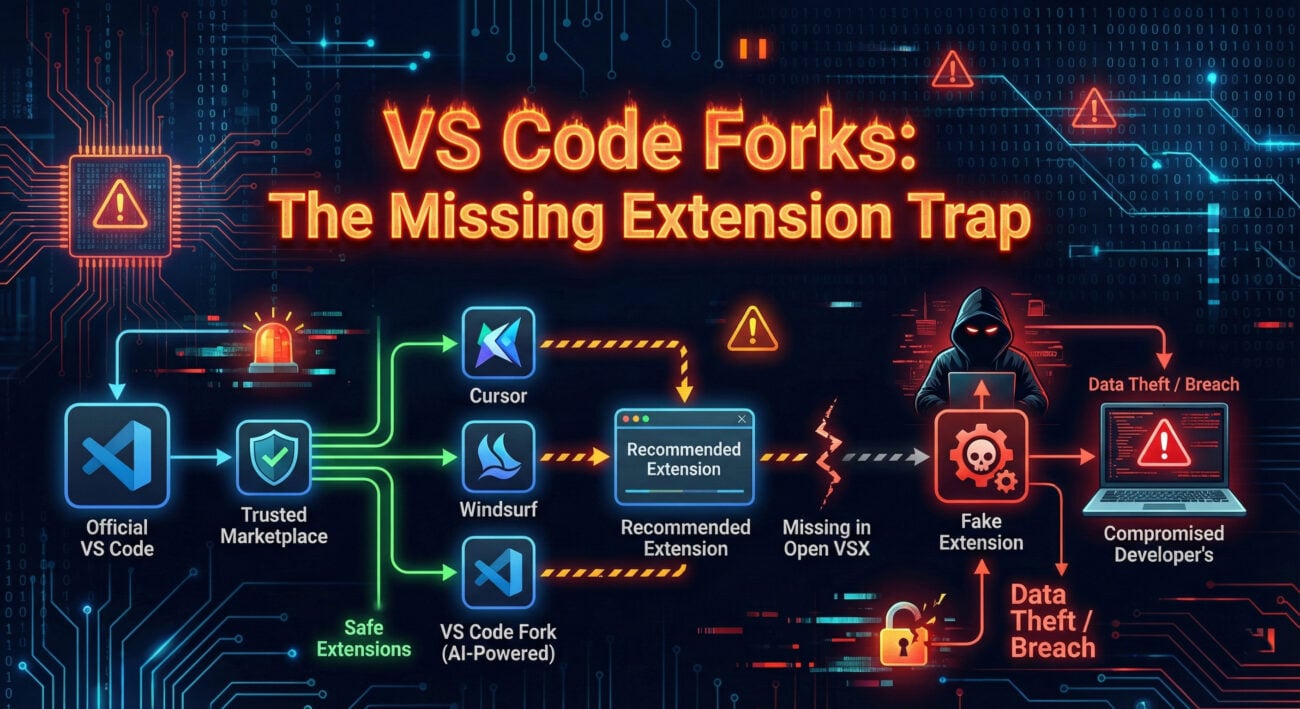
Your Visual Studio Code editor, the very tool you use to build secure applications, has become a prime target for sophisticated cyber attacks. A critical vulnerability in the VS Code extension security ecosystem allows malicious actors to distribute weaponized extensions through forked repositories, bypassing conventional security checks. This isn’t just theoretical, thousands of developers have already been exposed to this supply chain attack vector.
The core issue lies in how VS Code’s extension recommendation system can sometimes suggest forked versions of popular extensions. These forked extensions appear legitimate but contain hidden malware designed to steal credentials, exfiltrate source code, or establish persistent backdoors in development environments. Understanding this threat is crucial for every developer, from beginners to seasoned professionals, because your code editor has become the new attack surface.
New VVS Stealer Malware Targets Discord Accounts via Obfuscated Python Code

In the ever-evolving landscape of cyber threats, a new and particularly insidious malware named VVS Stealer has emerged, setting its sights on one of the world’s most popular communication platforms: Discord. This isn’t just another piece of nuisance software; it’s a sophisticated information-hacker’s tool designed to vacuum up your digital life, from passwords and authentication tokens to precious cryptocurrency wallets. For cybersecurity professionals, students, and beginners alike, understanding this threat is the first critical step in building an effective defense.

















































