Tudou Guarantee Halts Telegram Transactions, Having Handled More Than $12 Billion.
How to Defend Explained Simply
Table of Contents
- Executive Summary: The Rise and Fall of a Digital Black Market
- Real-World Scenario: Anatomy of a Pig-Butchering Scam
- Technical Deep Dive: The Marketplace Ecosystem & MITRE ATT&CK Mapping
- Step-by-Step: How a Fraud Campaign Was Built and Launched
- Common Mistakes & Best Practices for Defense
- Red Team vs. Blue Team View
- Defense Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action
Executive Summary: The Rise and Fall of a Digital Black Market
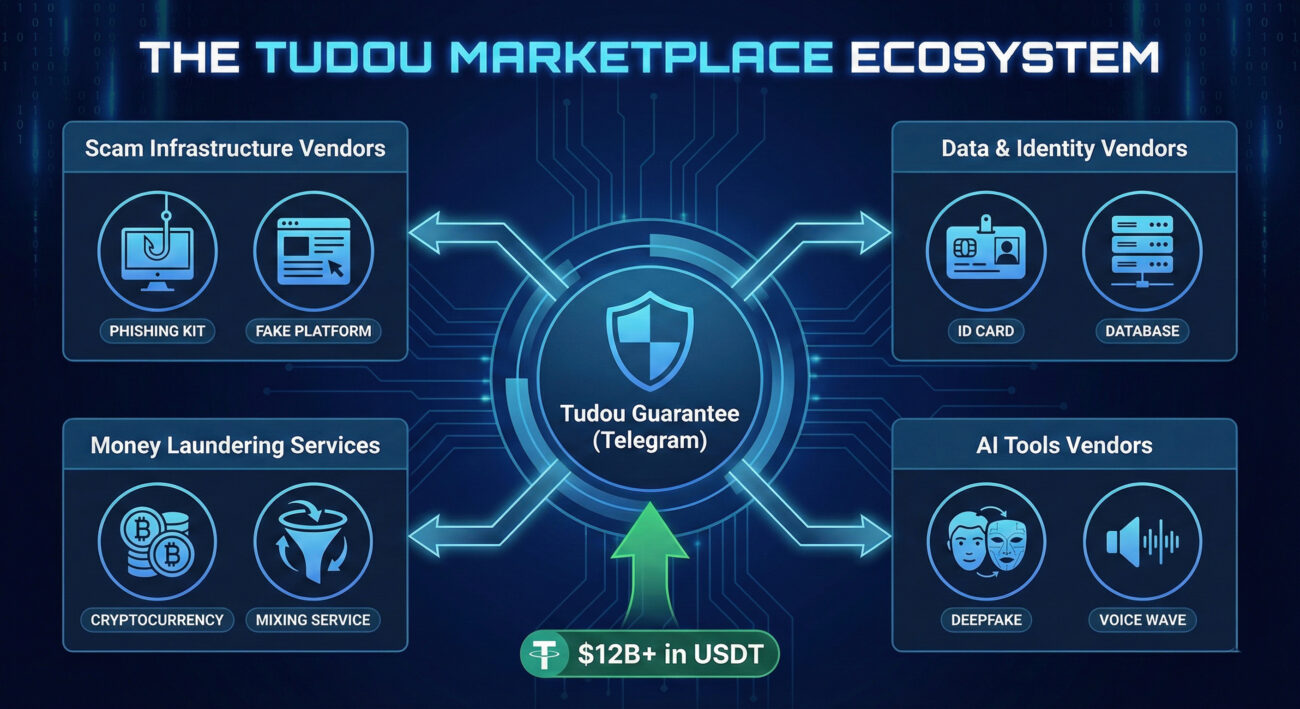
In January 2026, the cybersecurity landscape witnessed a significant event: the operational halt of "Tudou Guarantee," a massive Telegram-based illicit marketplace. Blockchain intelligence firm Elliptic revealed this platform had processed over $12 billion in cryptocurrency transactions, cementing its place as one of the largest cyber fraud hubs in history.
This wasn't just a simple chat group. Tudou Guarantee functioned as a full-service criminal bazaar, offering everything from stolen data and money laundering to AI-powered phishing kits. Its apparent winding down, linked to high-profile law enforcement actions in Southeast Asia, offers a rare, teachable moment. It exposes the inner workings of the modern scam economy and provides a clear map of the tactics, techniques, and procedures (TTPs) that defenders must understand. This analysis will dissect the Telegram cyber fraud marketplace model, link its operations to the MITRE ATT&CK framework, and provide actionable guidance for individuals and organizations to bolster their defenses.
Real-World Scenario: Anatomy of a Pig-Butchering Scam
The services sold on marketplaces like Tudou fuel complex, long-term frauds. The most notorious is the "pig-butchering" scam, which heavily relied on this Telegram cyber fraud marketplace infrastructure. Here’s how a typical campaign unfolded:
- Development & Recruitment: A scam syndicate, often operating from compounds in Southeast Asia, accesses Tudou to purchase pre-built, fraudulent cryptocurrency investment platforms and phishing website kits.
- Identity Forgery: They buy bundles of stolen personal data (names, photos, social profiles) to create believable fake identities for their operatives ("romance baiters").
- AI-Enhanced Engagement: To build trust during video calls with victims, they purchase AI face-swapping and voice-cloning software from the same marketplace, making impersonation flawless.
- Execution & Money Laundering: Once a victim "invests" funds, the syndicate uses money laundering services advertised on Tudou to quickly move and obfuscate the stolen cryptocurrency through mixers and shell entities.
The arrest of Cambodian billionaire Chen Zhi, allegedly connected to these operations, and the subsequent freeze in Tudou's transaction wallets, demonstrates the tangible impact of coordinated law enforcement on this digital underground economy.
Technical Deep Dive: The Marketplace Ecosystem & MITRE ATT&CK Mapping
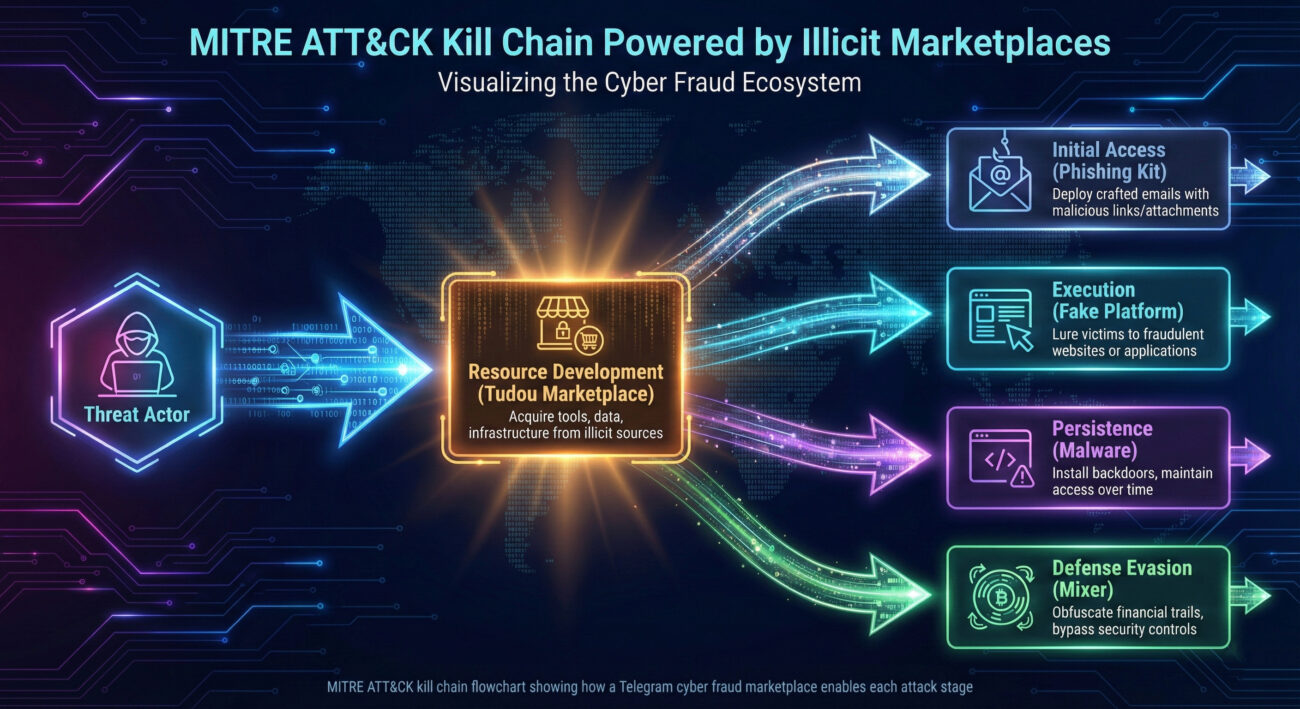
Understanding Tudou's role requires framing it within the MITRE ATT&CK framework. This Telegram cyber fraud marketplace wasn't the point of attack; it was the resource repository that enabled nearly every stage of the kill chain for countless other frauds.
Primary ATT&CK Tactics Facilitated by the Marketplace
| MITRE ATT&CK Tactic | How Tudou Marketplace Enabled It | Example Service/Product |
|---|---|---|
| Resource Development (TA0042) | This is the core function. The marketplace provided all the tools, infrastructure, and services needed to stage operations. | Phishing kits, fake exchanges, bulletproof hosting, compromised data dumps. |
| Initial Access (TA0001) | Sold the means to gain the first foothold with a victim. | Credential lists, phishing-as-a-service (PhaaS) platforms, smishing (SMS phishing) gateways. |
| Execution (TA0002) | Provided the scripts and software to run fraudulent applications. | Custom malware, automated trading bot scripts (for fake platforms), web injectors. |
| Defense Evasion (TA0005) | Offered tools to avoid detection by platforms and law enforcement. | Cryptocurrency tumblers/mixers, forged KYC documents, VPN and proxy services. |
The rise of AI-as-a-service on these platforms, as noted in Chainalysis's 2025 research, represents a quantum leap in threat capability. Tools for deepfakes and voice cloning directly enhance social engineering (ATT&CK Technique: T1586.003 - Acquire Infrastructure: Social Media Accounts), making impersonation attacks terrifyingly effective at scale.
Step-by-Step: How a Fraud Campaign Was Built and Launched
Let's break down the concrete steps a criminal would take to orchestrate a campaign using the Telegram cyber fraud marketplace, translating the abstract into actionable intelligence for defenders.
Step 1: Establish Operational Base & Resources
The threat actor joins Tudou Guarantee or a similar Telegram group. They browse vendor channels, using the platform's escrow service to ensure "safe" transactions. Their first purchases include a cloned, legitimate-looking investment website template and a bundle of thousands of phone numbers for SMS blasting.
Step 2: Forge Identities and Infrastructure
They purchase stolen identity packs (photos, bios) to create fake social media profiles on LinkedIn or dating apps. Simultaneously, they rent a "bulletproof" server to host their fake investment platform, paying with USDT (Tether) to maintain anonymity.
Step 3: Execute the Social Engineering Campaign
Operatives, using the forged identities, initiate contact with potential victims. For high-value targets, they may purchase a one-time use of an AI voice-cloning service to "verify" their identity during a call, a technique directly sourced from the marketplace.
Step 4: Launder and Cash Out Proceeds
Once funds are deposited by victims into the scam platform, the actor contacts a "money mover" service on Tudou. This service takes a 10-20% fee to convert the "dirty" crypto into clean assets through a series of complex cross-chain swaps and fictitious merchant transactions.
Common Mistakes & Best Practices for Defense
The existence of such markets highlights widespread security gaps. Here’s what organizations and individuals often get wrong, and how to fix it.
Common Mistakes (The Vulnerabilities)
- Underestimating Social Engineering: Dismissing AI-enhanced impersonation as science fiction, leaving employees untrained against sophisticated deepfake or voice cloning attacks.
- Weak Cryptocurrency Policies: Allowing business transactions with unvetted crypto wallets or failing to monitor for interactions with known illicit mixing services.
- Over-reliance on Basic Verification: Assuming a video call or a voice note is proof of identity in high-stakes financial or data-sharing scenarios.
- Ignoring Digital Footprint Hygiene: Employees with overly detailed public social profiles provide ample material for fraudsters to craft convincing fake identities.
Best Practices (The Fixes)
- Implement Advanced Identity Proofing: For critical operations, use multi-factor authentication that includes a dynamic challenge (e.g., "hold up three fingers") that is hard for real-time deepfakes to replicate.
- Adopt Blockchain Intelligence Tools: Use services like Elliptic or Chainalysis to screen cryptocurrency payments and wallets for links to sanctioned addresses or illicit service providers.
- Launch Continuous Security Awareness Training: Move beyond annual phishing tests. Use realistic simulations that include modern scam tactics like romance baiting and fake investment opportunities.
- Enforce Strict Social Media Policies: Educate staff, especially executives and finance personnel, on the risks of oversharing and the need for strict privacy settings.
Red Team vs. Blue Team View
The shutdown of Tudou is a tactical victory, but the strategic game continues. Here’s how both sides view the landscape.
The Red Team (Threat Actor) View
- Opportunity: The takedown creates a supply vacuum. Displaced vendors and buyers are actively seeking new, more decentralized platforms (e.g., on darker web forums or newer encrypted apps).
- Adaptation: Operations will fragment and become more resilient. Lessons are learned about wallet operational security (OpSec) from Tudou's blockchain analysis exposure.
- Innovation: The demand for harder-to-trace AI tools and privacy-centric cryptocurrencies will increase, driving further innovation in the criminal tech stack.
- Goal: Re-establish the same "guarantee" and escrow model that built trust on Tudou, but with better anonymity, ensuring the Telegram cyber fraud marketplace model evolves, not dies.
The Blue Team (Defender) View
- Intelligence Windfall: The takedown provides a treasure trove of data, wallet addresses, vendor aliases, transaction patterns, to enrich threat intelligence feeds and improve detection rules.
- Focus Shift: Defense must now monitor for the migration patterns of key vendors to emerging platforms, as highlighted in the U.S. Scam Center Strike Force announcements.
- Collaboration Imperative: Success stemmed from public-private collaboration (Elliptic, Telegram, law enforcement). This model must be sustained and formalized to target the next Tudou.
- Goal: Increase the cost and complexity for fraudsters by hardening potential targets (the public) and disrupting their operational tools, not just their marketplaces.
Defense Implementation Framework
Organizations can operationalize the lessons from this event using this structured framework.
| Defense Pillar | Actions & Controls | Tools & Resources |
|---|---|---|
| People & Awareness | Implement bi-annual, scenario-based training on advanced social engineering and crypto-scams. Establish a clear "challenge protocol" for unusual financial requests, even from executives. | Security awareness platforms (KnowBe4, Proofpoint), Internal reporting hotlines. |
| Process & Governance | Formalize cryptocurrency transaction policies requiring blockchain screening. Integrate indicators from marketplaces (wallet addresses, vendor names) into threat intelligence platforms (TIPs). | Blockchain analytics APIs (Elliptic, Chainalysis), Threat Intelligence Platforms (MISP, Anomali). |
| Technology & Monitoring | Deploy AI-powered media forensics tools to detect deepfakes in video interviews or verification calls. Monitor external social media and dark web for mentions of company executives or brands in fraud-related chatter. | Deepfake detection SDKs, Dark web monitoring services (Digital Shadows, Recorded Future). |
| Collaboration & Response | Establish a point of contact for reporting to law enforcement initiatives like the U.S. Scam Center Strike Force. Participate in sector-specific Information Sharing and Analysis Centers (ISACs). | FBI Internet Crime Complaint Center (IC3), Telegram's abuse reporting channels. |
Frequently Asked Questions (FAQ)
Q1: If Tudou is shut down, is the threat gone?
No. The underlying demand and criminal networks remain. As Elliptic noted, the activity will likely disperse to other guarantee marketplaces. The model is proven and profitable; the ecosystem will reconstitute.
Q2: I'm not a large corporation. Why should I care about this?
These marketplaces enable frauds that target individuals directly (romance scams, fake investments). Understanding the sophistication of the tools for sale (like AI cloning) makes you a harder target. It also highlights the risks of casual cryptocurrency transactions with unknown parties.
Q3: How can I, as an individual, check if a crypto wallet is suspicious?
While not foolproof, you can use public blockchain explorers or basic versions of screening tools. For significant transactions, consider using an exchange or service that performs compliance checks. The key principle is due diligence, treat sending crypto to a new wallet address with the same caution as wiring money to a stranger's bank account.
Q4: What's the role of Telegram in this? Are they liable?
Telegram provides the encrypted communication platform. They have taken action to shutter thousands of public channels (as with HuiOne). However, the private, invite-only nature of some groups makes complete eradication difficult. Their role is governed by their Terms of Service and local laws, and they collaborate with law enforcement under legal orders.
Key Takeaways
- The takedown of the Telegram cyber fraud marketplace "Tudou Guarantee" reveals a mature, service-based criminal economy capable of processing tens of billions of dollars.
- These platforms are not attack vectors themselves but critical Resource Development hubs within the MITRE ATT&CK framework, enabling every subsequent stage of fraud campaigns.
- The integration of AI-powered tools (deepfakes, voice cloning) for sale represents a significant escalation in social engineering threats, demanding new verification strategies.
- Effective defense requires a multi-pillar approach: awareness training against advanced scams, technical controls for identity proofing and crypto screening, and active collaboration with industry and law enforcement partners.
- While a tactical win, the strategic threat is persistent and adaptive. Vigilance and intelligence-sharing are paramount as criminal operations migrate to new platforms.
Call to Action
Fortify Your Defenses Today
The landscape illuminated by the Tudou case is complex, but actionable. Don't wait to become a statistic.
For Individuals: Audit your social media privacy settings this week. Have a conversation with family members about the red flags of "too-good-to-be-true" online investments.
For Security Teams: Schedule a tabletop exercise next quarter simulating a Business Email Compromise (BEC) attack that uses AI voice cloning. Review if your threat intel feeds include indicators from illicit crypto marketplaces.
For Everyone: Stay informed. Follow reputable sources like The Hacker News, MITRE ATT&CK, and official law enforcement bulletins to understand the evolving threat landscape.
Cybersecurity is a shared responsibility. Understanding the adversary's toolkit is the first step toward building an effective defense.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































