UAT-7290 Telecom Attack
Inside China-Linked Linux Malware & ORB Espionage Explained Simply
In the complex landscape of modern cyber-espionage, the UAT-7290 telecom attack stands out as a sophisticated and multi-faceted campaign. Targeting critical telecommunications infrastructure in South Asia and Southeastern Europe, this threat actor leverages a unique blend of Linux-based malware and the creation of secret Operational Relay Box (ORB) networks. For cybersecurity professionals and beginners alike, understanding this attack is crucial, as it reveals how state-aligned groups burrow deep into networks not just to steal secrets, but to build infrastructure for future attacks by other actors.
Table of Contents
- Executive Summary: The UAT-7290 Campaign
- Technical Breakdown: The Malware Toolset
- Mapping to MITRE ATT&CK: A Defender's Guide
- The Attack Lifecycle: Step-by-Step Intrusion
- Red Team vs. Blue Team Perspectives
- Practical Defense Framework & Best Practices
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The UAT-7290 Campaign
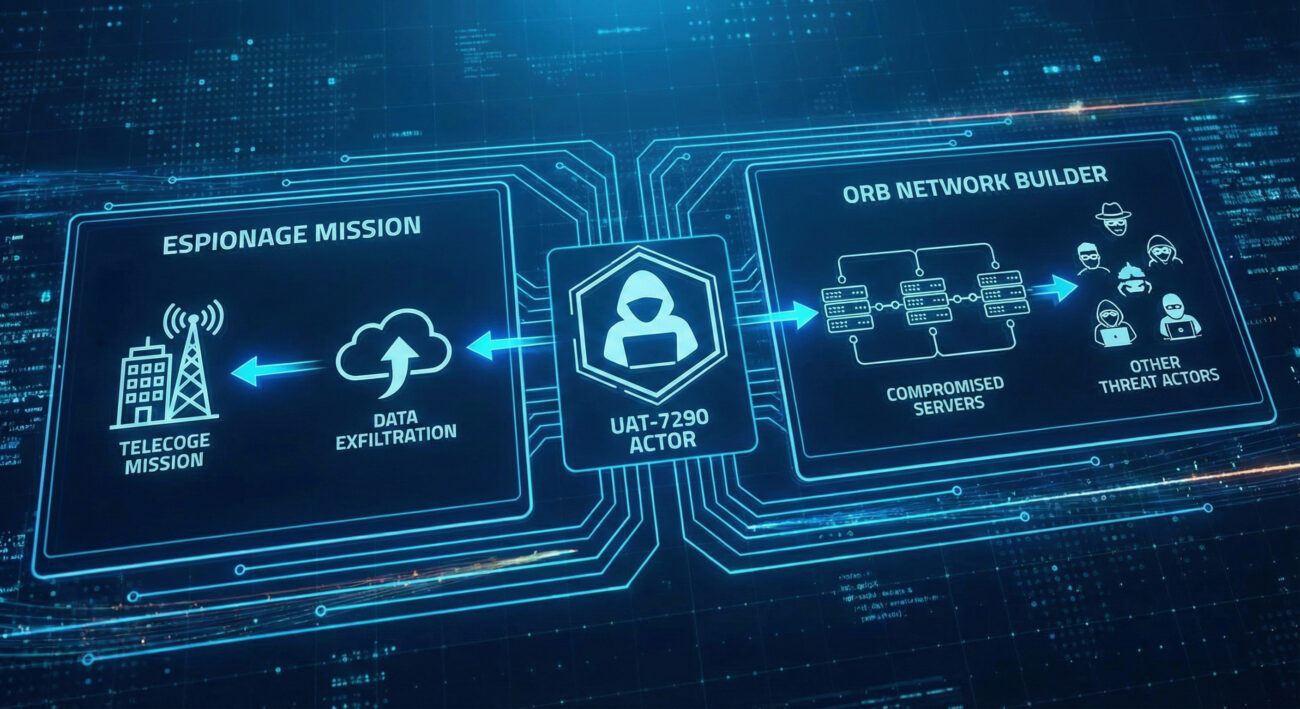
Attributed to a China-nexus threat actor, UAT-7290 (also tracked as CL-STA-0969) has been active since at least 2022. Their primary mission is twofold: conduct long-term espionage against telecommunications firms and transform compromised edge devices into a covert network of ORB nodes. These ORB nodes act as anonymous relay points, which can then be leased or used by other threat actors to obscure the origin of their own attacks, making UAT-7290 both an espionage group and an "initial access broker" on a grand scale.
The group's tradecraft is notable for its pragmatism and efficiency. Instead of relying solely on expensive zero-day exploits, UAT-7290 frequently uses "one-day" exploits, publicly disclosed vulnerabilities for which proof-of-concept code is available. They combine this with targeted SSH brute-force attacks against public-facing servers, demonstrating a focus on low-cost, high-impact intrusion methods.
Technical Breakdown: The Linux Malware Toolset
Unlike many espionage groups that focus on Windows, the UAT-7290 telecom attack heavily utilizes a suite of Linux malware, tailored for attacking servers and network edge devices commonly found in telecom infrastructure.
Core Malware Components
- RushDrop (aka ChronosRAT): This is the initial dropper. Its job is to establish a foothold on the compromised system and deploy the next stage of malware. It's a modular ELF binary capable of basic reconnaissance and execution.
- DriveSwitch: This component acts as a loader or "peripheral malware." It is deployed by RushDrop and is specifically responsible for executing the main backdoor, SilentRaid, onto the system.
- SilentRaid (aka MystRodX): This is the primary, feature-rich backdoor. Written in C++, it provides persistent access and uses a plugin-style architecture to offer various capabilities like remote shell, port forwarding, file exfiltration, and keylogging.
The ORB Creator: Bulbature Backdoor
A distinct tool in their arsenal is Bulbature. This backdoor's singular purpose is to convert a compromised device, like a router or a server, into an ORB node. Once installed, it configures the device to relay traffic for other malicious actors, effectively making it a stealthy proxy within the victim's own network. This is a prime example of "living off the land" and creating breach multiplier effects.
| Malware Name | Type | Primary Function | Key Attribute |
|---|---|---|---|
| RushDrop | Dropper | Initial infection, deploys next stage | Modular, Linux ELF binary |
| DriveSwitch | Loader | Executes the SilentRaid backdoor | Bridge between dropper and backdoor |
| SilentRaid | Backdoor | Persistence, remote access, data theft | C++, plugin-based architecture |
| Bulbature | Backdoor | Creates ORB (proxy) nodes | Infrastructure-focused |
Mapping to MITRE ATT&CK: A Defender's Guide
Understanding the UAT-7290 telecom attack through the MITRE ATT&CK framework provides a structured blueprint for defense. Below are the key tactics and techniques associated with this campaign.
| MITRE ATT&CK Tactic | Technique (ID) | How UAT-7290 Implements It | Defensive Insight |
|---|---|---|---|
| Reconnaissance | Active Scanning (T1595) | Extensive technical probing of target networks and public-facing assets. | Monitor for unusual scanning patterns from new or suspicious IP ranges. |
| Initial Access | Exploit Public-Facing Application (T1190) | Uses one-day exploits for vulnerabilities in edge devices (e.g., firewalls, VPNs). | Patch public-facing devices aggressively; a one-day delay is a major risk. |
| Initial Access | Brute Force (T1110) | Targeted SSH brute-force attacks against identified servers. | Enforce strong password policies and implement MFA for SSH where possible. |
| Persistence | Server Software Component (T1505) | Installs Bulbature and SilentRaid on compromised servers and edge devices. | Regular integrity checks on system binaries and server configurations. |
| Command and Control | Proxy (T1090) | Uses self-created ORB nodes (via Bulbature) to relay C2 traffic, hiding origins. | Network traffic analysis for unusual outbound connections from internal devices acting as proxies. |
The Attack Lifecycle: A Step-by-Step Intrusion Breakdown
Let's walk through how a typical UAT-7290 telecom attack unfolds, from initial probing to establishing a hidden ORB network. This step-by-step view is critical for defenders to recognize the sequence of events.
Step 1: Reconnaissance & Target Selection
The actor conducts extensive reconnaissance to map the target telecom's external digital footprint. They identify public-facing edge devices (like firewalls, VPN gateways, or web servers), note software versions, and hunt for known vulnerabilities.
Step 2: Initial Compromise
Using the intelligence gathered, they gain initial access. This is typically achieved through one of two methods: 1) Deploying a public proof-of-concept exploit for a recently patched vulnerability (a "one-day"), or 2) Launching a focused SSH brute-force attack against a server with weak credentials.
Step 3: Malware Deployment & Foothold
Once on a system, the RushDrop dropper is deployed. It then calls upon DriveSwitch to install the SilentRaid backdoor. SilentRaid establishes persistence, communicates with its command-and-control (C2) server, and awaits further instructions.
Step 4: Internal Reconnaissance & Pivoting
With a persistent backdoor in place, the actor performs internal reconnaissance to understand the network layout, locate valuable data (call records, customer data, network maps), and identify other critical systems, particularly other edge devices suitable for ORB conversion.
Step 5: ORB Network Construction
On selected devices, the actor deploys the Bulbature backdoor. This software reconfiguresthe device to act as a covert proxy or relay. Multiple such compromised devices across different victim networks can be linked to form a resilient, hard-to-trace ORB network for future operations by UAT-7290 or other groups.

Red Team vs. Blue Team Perspectives
Red Team (Threat Actor View)
Objectives: Steal sensitive telecom data for espionage. Create a hidden, resilient ORB infrastructure for future profit or use by allied groups.
Core Strategy: Cost-effective operations. Maximize impact by focusing on known vulnerabilities (one-days) and weak credentials rather than investing in zero-days. Emphasize stealth and long-term persistence.
Key Tools/TTPs:
- Open-source intelligence (OSINT) and scanning for target profiling.
- Leveraging public exploit code (one-days) for rapid initial access.
- Deploying lean, modular Linux malware (RushDrop, SilentRaid).
- Prioritizing the installation of infrastructure malware (Bulbature) to create long-term value.
Blue Team (Defender View)
Objectives: Prevent initial compromise. Detect lateral movement and malware execution. Identify and dismantle covert ORB nodes within the network.
Core Strategy: Secure the attack surface. Assume breach and hunt for anomalies. Focus on hardening edge devices and monitoring for proxy behaviors.
Key Defensive Actions:
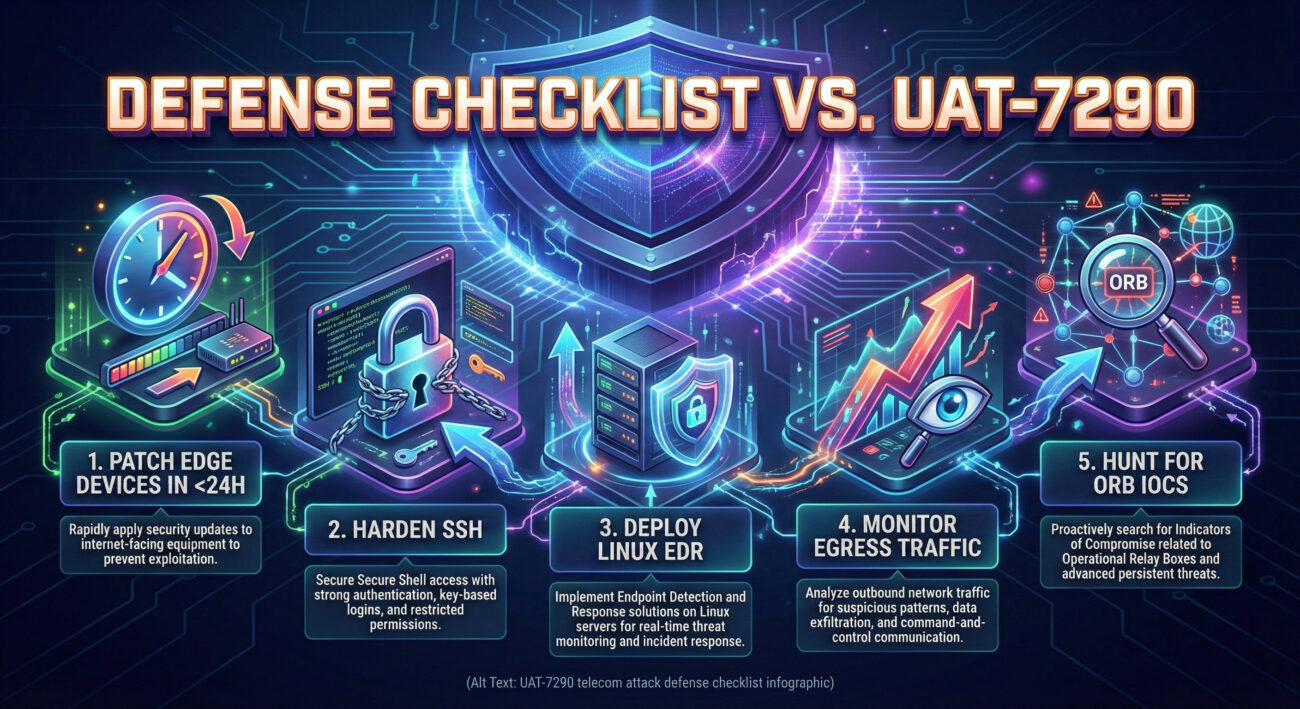
- Implement aggressive, sub-24-hour patching cycles for all public-facing devices.
- Enforce strong password and key-based authentication for SSH; use network ACLs to limit access.
- Deploy Endpoint Detection and Response (EDR) tools on Linux servers, not just Windows workstations.
- Monitor network egress traffic for devices acting as unexpected proxies or relays.
Practical Defense Framework & Best Practices
To defend against the UAT-7290 telecom attack and similar advanced persistent threats (APTs), organizations must move beyond basic hygiene. Here is a mix of common pitfalls and actionable best practices.
Common Mistakes & Best Practices
Common Mistakes (To Avoid)
- Slow Patching Cycles: Treating edge device patching as a monthly or quarterly task, leaving a wide window for one-day exploits.
- Ignoring Linux Security: Assuming only Windows endpoints need advanced EDR and monitoring, leaving servers vulnerable.
- Weak Authentication on Servers: Allowing password-based SSH authentication without rate-limiting or MFA.
- Limited Network Egress Monitoring: Not analyzing outbound traffic for patterns indicative of proxy/C2 communication.
- Overlooking Known IOCs: Failing to hunt for published indicators of compromise (IOCs) related to RushDrop, SilentRaid, or Bulbature.
Best Practices (To Implement)
- Zero-Trust for Edge Devices: Apply the principles of Zero-Trust Network Access (ZTNA) to firewalls, VPNs, and gateways. Verify explicitly, assume breach.
- Extended Patching SLA: Establish a Service Level Agreement (SLA) to patch critical public-facing vulnerabilities within 24 hours of patch release.
- Linux EDR & HIDS: Deploy Endpoint Detection and Response (EDR) or Host-based Intrusion Detection Systems (HIDS) on all critical Linux servers to spot malicious processes and file changes.
- Network Traffic Analysis (NTA): Use tools to baseline normal internal and egress traffic. Alert on internal devices initiating high volumes of connections to external IPs (possible ORB/proxy activity).
- Threat Intelligence Integration: Subscribe to feeds and proactively hunt for tactics and IOCs associated with China-nexus groups like UAT-7290, Stone Panda, and RedFoxtrot.
Frequently Asked Questions (FAQ)
Q1: Why are telecom companies specifically targeted by UAT-7290?
Telecommunications providers are high-value targets for espionage. They hold vast amounts of sensitive metadata, customer information, and control critical national infrastructure. Furthermore, their networks are rich with high-bandwidth, usually well-maintained servers that make perfect, inconspicuous ORB nodes for global malicious operations.
Q2: What's the real-world impact of an ORB network being built inside a company?
Beyond the immediate data theft, your company's infrastructure becomes an unwitting accomplice in cyber attacks against other organizations worldwide. This can lead to severe legal, reputational, and regulatory consequences. It also complicates forensic investigations for both your company and law enforcement, as malicious traffic appears to originate from your compromised servers.
Q3: As a beginner, what's the first thing I should check for in my network?
Start with the basics that UAT-7290 exploits:
- Audit all public-facing devices (firewalls, VPNs, web servers) for unpatched critical/High-severity vulnerabilities from the last 6 months.
- Review SSH authentication logs for failed login attempts from unexpected geographic locations.
- Check if your Linux servers have any security or monitoring agents installed, if not, this is a major gap to address.
For a deeper technical dive on Linux threat hunting, consider resources from the SANS Institute Blog.
Q4: How can I stay updated on the latest tactics used by groups like UAT-7290?
Follow trusted threat intelligence sources. The original analysis for this campaign came from Cisco Talos. Other excellent resources include Mandiant's Blog and the MITRE ATT&CK® website itself, where you can track techniques used by various APT groups.
Key Takeaways & Call to Action
Summary of Critical Lessons
- The Threat is Dual-Purpose: UAT-7290 isn't just stealing data; they are building infrastructure within victim networks. Defenders must look for signs of both espionage and unauthorized proxy/relay services.
- Linux is a Prime Target: Advanced actors are increasingly targeting Linux servers in critical infrastructure. Your Linux security posture needs to be as robust as your Windows posture.
- Speed of Defense is Key: The actor's reliance on "one-day" exploits means the time between vendor patch release and your implementation is a critical risk window. Automate and accelerate patching.
- Beyond Initial Access: Defense cannot stop at the perimeter. Assume initial compromise will happen and deploy monitoring to detect lateral movement, unusual process execution, and anomalous network flows indicative of ORB activity.
Your Call to Action
Don't let this be just another report you read. The UAT-7290 telecom attack provides a clear playbook of both the threat and the defense.
This Week: Conduct an urgent review of your external attack surface. Identify your ten most critical public-facing devices and verify their patch status for the last three months.
This Month: Initiate a project to extend advanced security monitoring (like EDR or rigorous file integrity monitoring) to your most critical Linux servers. Begin a threat hunting exercise looking for historical SSH brute-force attempts or unknown outbound connections from your network.
Cybersecurity is a continuous process. By understanding sophisticated adversaries like UAT-7290, you empower yourself to build more resilient defenses. For ongoing learning, explore our internal resource on Network Hardening Fundamentals and Linux Threat Hunting 101.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































