AI-Assisted VoidLink Linux Malware Surpasses 88,000 Lines of Code
The AI-Powered Threat Reshaping Cyber Defense
The discovery of the VoidLink Linux malware framework marks a pivotal moment in cybersecurity. It represents one of the first advanced, fully functional malware strains assessed to be predominantly generated by Artificial Intelligence (AI). This analysis will dissect VoidLink, explain its operational mechanisms, map its techniques to the MITRE ATT&CK® framework, and provide actionable defense strategies for both seasoned professionals and those new to the field.
Table of Contents
- Executive Summary: The VoidLink Paradigm Shift
- Mapping VoidLink to MITRE ATT&CK
- Technical Breakdown: How VoidLink Operates
- Red Team vs. Blue Team: Attack & Defense Perspectives
- Common Mistakes & Best Practices for Defense
- The AI Cybercrime Future & Defense Framework
- Visual Guide: The VoidLink Attack Chain
- Frequently Asked Questions (FAQ)
- Key Takeaways & Call to Action
Executive Summary: The VoidLink Paradigm Shift
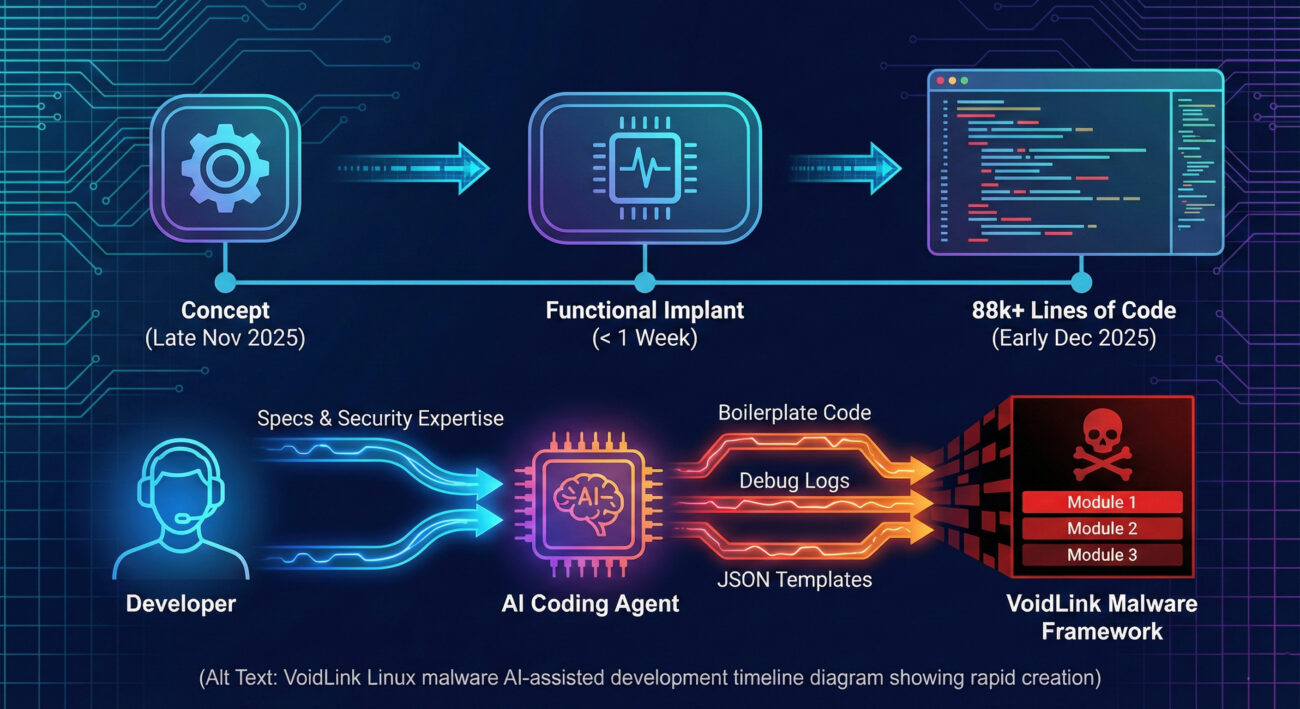
In late 2025, cybersecurity researchers uncovered VoidLink, a sophisticated malware framework specifically designed for stealthy, long-term presence in Linux-based cloud environments. What sets it apart is its origin: evidence strongly suggests it was built by a single developer using an AI coding agent to accelerate the process, reaching over 88,000 lines of functional Zig code in a matter of weeks.
This isn't about AI creating new, unimaginable attack methods. Instead, it's about democratization and acceleration. VoidLink demonstrates how AI lowers barriers, enabling a single threat actor to produce tooling that once required the resources of a coordinated team or nation-state. The framework is built for persistence, featuring capabilities like rootkit-like hiding, credential theft, and container escape, posing a significant risk to cloud infrastructure.
Mapping the VoidLink Linux Malware to MITRE ATT&CK®
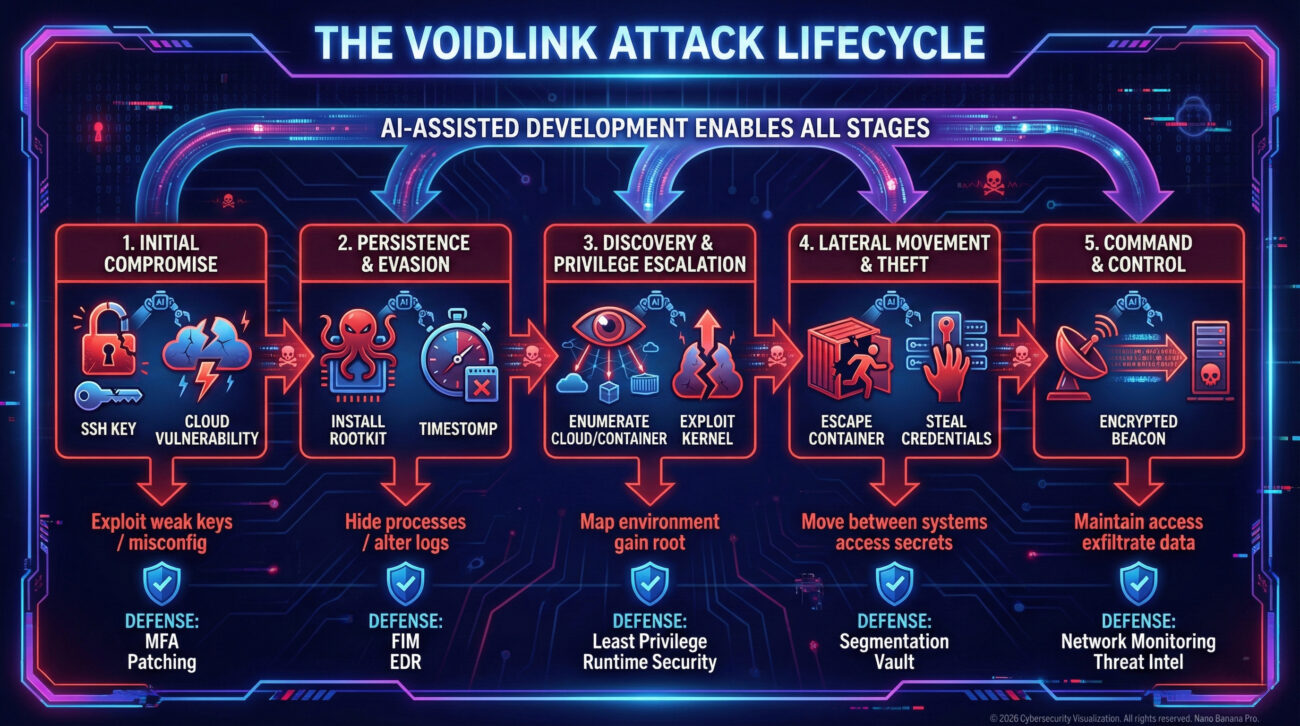
Understanding VoidLink through the lens of the MITRE ATT&CK framework is crucial for defenders. It allows us to categorize its behaviors and prepare targeted detections. VoidLink's design spans multiple tactical phases.
| MITRE ATT&CK Tactic | VoidLink Technique / Implementation | Description & Impact |
|---|---|---|
| Persistence (TA0003) | Kernel Module Rootkit, Systemd Service Installation | Installs itself deeply into the system to survive reboots and evade casual inspection, ensuring long-term access for the attacker. |
| Defense Evasion (TA0005) | Direct System Calls (Syscalls), Timestomping, Log Manipulation | Uses advanced programming to bypass user-mode monitoring tools and alters file timestamps/logs to erase traces of its activity and breach. |
| Discovery (TA0007) | Container & Cloud Environment Enumeration | Probes the compromised system to identify if it's running in a container (Docker, Kubernetes) and maps the cloud environment for lateral movement. |
| Privilege Escalation (TA0004) | Exploitation of Kernel Vulnerabilities | Contains modules designed to leverage known Linux kernel flaws to gain root-level privileges from a lower-access entry point. |
| Lateral Movement (TA0008) | Credential Theft, Container Escape | Steals SSH keys, cloud access tokens, and attempts to "break out" of a compromised container to infect the underlying host and other systems. |
| Command and Control (TA0011) | Encrypted Beaconing to Hardcoded IPs | Periodically calls back to hacker-controlled servers using encrypted channels to receive instructions and exfiltrate data. |
Technical Breakdown: How the VoidLink Malware Framework Operates
Let's look under the hood. VoidLink is written in the Zig programming language, chosen for its performance and low-level control, which is ideal for writing stealthy rootkits. Analysis by Check Point and Sysdig revealed tell-tale signs of AI-assisted development:
- Excessively Consistent Formatting: Debug logs and output across all modules were perfectly uniform, lacking the minor inconsistencies typical of human-written code.
- Placeholder Data: Use of generic names like "John Doe" in template responses, commonly found in AI training datasets.
- Uniform Versioning: All API modules were labeled "_v3" (e.g., BeaconAPI_v3), suggesting a template-like generation process.
The developer followed a "Spec Driven Development (SDD)" workflow: they planned the architecture, broke it into tasks, and used an AI agent (like TRAE SOLO) to generate the implementation code. This allowed rapid iteration from concept to a complex, working malware implant in under a week.
Code Analysis: A Glimpse into AI-Generated Malware
The structure of the code often reveals its generative origins. Below is a simplified, illustrative example of the kind of consistent, templatized structure found in VoidLink, particularly in its configuration and communication modules.
Example: Templatized Configuration Structure
Note: This is a representative example, not the actual VoidLink code.
// AI-generated code often shows extreme consistency in structure
typedef struct BeaconConfig_v3 {
char campaign_id[32]; // Always 32 bytes, zero-padded
char primary_c2[64]; // Format: "ip:port" always
int beacon_interval_sec; // Field name style is uniform
bool enable_encryption; // Boolean flag
char fallback_domain[128]; // Another perfectly sized array
} BeaconConfig_v3;
// Notice the pattern: _v3 suffix, perfectly aligned comments,
// and systematic field sizing. Human code often has minor variations.
This level of uniformity across thousands of lines of code is a strong forensic indicator of AI-assisted generation, as noted by researchers.
Red Team vs. Blue Team: Attack & Defense Perspectives on VoidLink
The Red Team / Attacker View
For a threat actor, VoidLink represents a force multiplier.
- AI as a Co-pilot: The AI handles tedious boilerplate code, complex logging systems, and standardized API structures, allowing the human to focus on core attack logic and evasion techniques.
- Rapid Prototyping: New modules for credential theft or container escape can be spec'd out and generated quickly, enabling fast adaptation to target environments.
- Operational Efficiency: A single skilled developer can now manage a project of a scale previously needing a team, reducing operational overhead and risk of exposure.
- Consistency is a (Double-Edged) Strength: The uniform code is less prone to human error bugs but may also create detectable patterns for defenders.
The Blue Team / Defender View
For defenders, the rise of AI-generated malware like VoidLink changes the threat landscape.
- Shift from "What" to "How": The specific malware variant is less important than understanding its behavioral patterns (the MITRE ATT&CK tactics).
- Detect Patterns, Not Signatures: Look for the behavioral indicators: unusual direct syscall activity, patterns of consistent templatized log entries, or suspicious container escape attempts.
- Enhance Baseline Monitoring: Know what "normal" looks like in your cloud environments. VoidLink's discovery and enumeration activities can create subtle anomalies in process trees and network calls.
- Leverage AI Defensively: Use AI-powered security tools to analyze vast amounts of system and network data for these subtle, pattern-based anomalies that traditional rules might miss.
Common Mistakes & Best Practices for Defense
❌ Common Defense Mistakes
- Over-Reliance on Signature-Based AV: Assuming traditional antivirus will catch novel, AI-generated malware like VoidLink.
- Neglecting Linux/Cloud Security: Treating Linux systems as inherently secure and not applying the same rigor of monitoring and patching as Windows environments.
- Poor Credential Hygiene: Using static, long-lived credentials in cloud environments, which are prime targets for theft by tools like VoidLink.
- Ignoring Container Security: Running containers with excessive privileges or not monitoring for container escape behaviors.
- Unmonitored Network Egress: Not logging or alerting on outbound connections to unknown or suspicious IP addresses.
✅ Essential Best Practices
- Adopt Behavioral Detection (EDR/XDR): Implement Endpoint/Extended Detection and Response solutions that focus on malicious activities (MITRE ATT&CK) rather than just file hashes.
- Rigorous Patch Management: Promptly apply security patches, especially for the Linux kernel and container runtimes, to close vulnerabilities VoidLink exploits.
- Enforce Principle of Least Privilege: Use role-based access control (RBAC) and just-in-time access. Replace static secrets with dynamically rotated credentials or managed identities.
- Harden Container Environments: Run containers as non-root users, use read-only filesystems where possible, and employ tools like Tracee for runtime security.
- Implement Network Segmentation & Monitoring: Segment cloud networks and use tools to monitor for anomalous outbound traffic and command-and-control beaconing.
The AI Cybercrime Future & A Proactive Defense Framework
VoidLink is a harbinger. As Group-IB's research states, AI is supercharging a "fifth wave" of cybercrime, industrializing malware development, phishing, and impersonation.
A 4-Pillar Defense Framework for the AI Era
Pillar 1: Assume Sophistication & Speed
Shift your mindset. Assume adversaries can generate complex tools rapidly. Your defense must be proactive and resilient, not just reactive to known threats.
Pillar 2: Build Behavior-Centric Visibility
Instrument your environment (endpoints, cloud, identity) to feed data into a centralized security platform (SIEM/XDR). Focus on detecting tactical behaviors (e.g., privilege escalation, lateral movement) mapped in frameworks like MITRE ATT&CK.
Pillar 3: Automate Response & Hardening
Use automation to enforce security baselines. This includes auto-remediating misconfigurations, enforcing strong password and MFA policies, and isolating compromised assets based on behavioral alerts.
Pillar 4: Foster Continuous Education
The threat landscape evolves daily. Engage with resources like the SANS Institute Blog and the CISA Alerts to stay informed. Train your team to recognize and respond to advanced threats.
Visual Guide: The VoidLink Linux Malware Attack Chain
Frequently Asked Questions (FAQ)
Q1: Is my personal Linux laptop at risk from VoidLink?
A: The current analysis suggests VoidLink is targeted at cloud and server environments for long-term espionage or resource theft. While its techniques are dangerous, the immediate risk to individual personal computers is lower. However, it underscores the importance of keeping all systems updated.
Q2: Can AI really write complex malware from scratch?
A: Not from a vague idea. As seen with VoidLink, it follows Spec Driven Development. A skilled human provides the architecture, security knowledge, and detailed specifications. The AI then acts as a super-efficient junior programmer, generating the vast amounts of structured code to bring the spec to life quickly. The "brain" is still human; the "brawn" is AI.
Q3: How can I detect something as stealthy as a rootkit?
A: Rootkits are challenging. Look for indirect anomalies: unexpected network connections from a system, slight performance hits, or failures in system integrity checks. Tools that leverage hardware-assisted security (like Intel TXT) or boot from known-good media can help detect kernel-level compromises.
Q4: Does this mean we need AI to fight AI in cybersecurity?
A: Not exclusively, but it's a powerful force multiplier for defense. Defensive AI excels at sifting through terabytes of logs and network data to find the subtle, patterned anomalies that tools like VoidLink might generate. Human expertise is still vital for strategy, investigation, and response, but AI is becoming an essential tool in the defender's arsenal.
Key Takeaways & Call to Action
Summary of Critical Points:
- VoidLink is a Benchmark: It's a tangible example of sophisticated, AI-generated malware targeting critical Linux cloud infrastructure.
- AI Lowers Barriers: It enables smaller actors to develop advanced tools, increasing the volume and sophistication of threats.
- Defense Must Evolve: Move beyond signatures to behavior-based detection (MITRE ATT&CK) and assume a faster, more automated adversary.
- Cloud & Linux are Prime Targets: These environments require focused security hardening, monitoring, and credential management.
- Consistency Can Be a Weakness: The very uniformity of AI-generated code can create detectable patterns for alert defenders.
Your Call to Action today:
- Assess Your Posture: Review your cloud and Linux security. Are you monitoring for behavioral anomalies, not just known bad files?
- Prioritize Patching: Ensure your kernel and cloud service security updates are applied promptly.
- Educate Your Team: Share this analysis. Discuss what AI-powered threats mean for your organization's defense strategy.
The era of AI-powered cyber threats is not a distant future, it's here. VoidLink proves it. By understanding its mechanics and adapting our defenses accordingly, we can ensure that AI empowers defenders just as much as it does attackers.
© Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.
Latest News
- All Posts
- News


















































