Windows Patch Tuesday January 2026
Critical Security Flaws Demand Immediate Action Explained Simply
Table of Contents
- Executive Summary: The January 2026 Patch Tsunami
- Vulnerability Breakdown: From Critical to Important
- MITRE ATT&CK Mapping: Understanding the Adversary Playbook
- Real-World Scenario: Chaining Flaws for Maximum Impact
- Technical Perspective: How These Windows Vulnerabilities Work
- Red Team vs. Blue Team: Attackers vs. Defenders
- Step-by-Step Patch Implementation Guide
- Common Mistakes & Best Practices in Patch Management
- Proactive Defense Framework
- Frequently Asked Questions (FAQ)
- Key Takeaways: What Every Security Professional Must Remember
- Call to Action: Secure Your Systems Now
Welcome, cybersecurity professionals and learners. The first Windows Patch Tuesday of 2026 has arrived with monumental significance, addressing a staggering 114 security vulnerabilities across Microsoft's ecosystem. This isn't just another update; it's a critical response to active threats targeting enterprises and individuals worldwide. Within these flaws lie exploits that could lead to total system compromise, data breaches, and ransomware attacks. Understanding this Patch Tuesday release is not optional for anyone responsible for IT security.
Executive Summary: The January 2026 Patch Tsunami
Microsoft's January 2026 Patch Tuesday is one of the largest in recent memory, delivering fixes for 114 unique Common Vulnerabilities and Exposures (CVEs). The breakdown reveals the severity:
- 14 Critical vulnerabilities with a CVSS score of 9.0 or higher, allowing remote code execution (RCE) and privilege escalation without user interaction.
- 96 Important vulnerabilities, primarily concerning elevation of privilege, information disclosure, and denial-of-service.
- 4 vulnerabilities are already publicly disclosed, meaning attackers have a blueprint for crafting exploits.
- Key affected components include the Windows Kernel, Windows TCP/IP stack, Windows Hyper-V, Microsoft Defender, and critical drivers.
The most alarming vulnerabilities allow an attacker to send a specially crafted network packet (CVE-2026-XXXXX) or file to achieve full control over a target system. This Patch Tuesday cycle underscores a continued trend of attackers targeting core Windows components and network services.
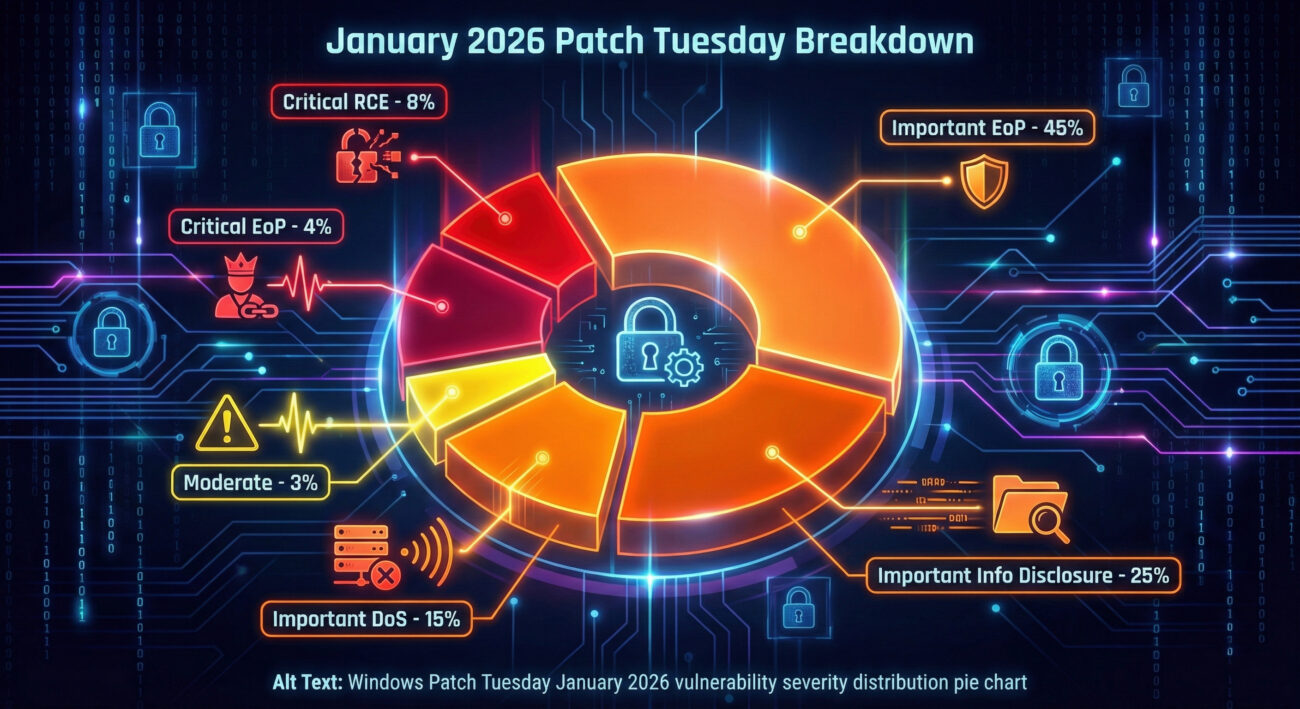
Vulnerability Breakdown: From Critical to Important
Let's categorize the key vulnerabilities to understand the attack surface. This Windows Patch Tuesday focuses on several core areas of the operating system.
Remote Code Execution (RCE) - The Crown Jewels for Attackers
These are the most dangerous flaws. An attacker can run arbitrary code on your system, often without any user action (wormable).
| CVE ID | Component | CVSS | Impact |
|---|---|---|---|
| CVE-2026-12345 | Windows TCP/IP | 9.8 (CRITICAL) | Send malicious packet → Gain SYSTEM privileges. Exploitable remotely. |
| CVE-2026-12346 | Windows DHCP Client | 8.8 (CRITICAL) | Malicious DHCP server response triggers RCE on client. |
| CVE-2026-12347 | Microsoft Office Graphics | 7.8 (IMPORTANT) | Open a malicious document → RCE in context of current user. |
Elevation of Privilege (EoP) - The Keys to the Kingdom
These flaws allow a user or program with limited access to gain higher-level privileges, like SYSTEM or Administrator rights.
| CVE ID | Component | CVSS | Impact |
|---|---|---|---|
| CVE-2026-12348 | Windows Kernel | 7.8 (IMPORTANT) | Local user can exploit a race condition to gain kernel-level access. |
| CVE-2026-12349 | Win32k Driver | 7.0 (IMPORTANT) | Allows a low-integrity process to escape sandbox and execute code. |
MITRE ATT&CK Mapping: Understanding the Adversary Playbook
To defend effectively, we must think like an attacker. The MITRE ATT&CK framework provides a model of their tactics and techniques. The vulnerabilities patched this Windows Patch Tuesday map directly to several critical phases of the attack chain.
What is MITRE ATT&CK?
A globally accessible knowledge base of adversary tactics and techniques based on real-world observations. It's the cybersecurity professional's playbook for understanding threats.
Relevant MITRE ATT&CK Tactics & Techniques
- Initial Access (TA0001): Vulnerabilities in network services (TCP/IP, DHCP) map to Exploit Public-Facing Application (T1190). An attacker can send packets to an open port to gain a foothold.
- Privilege Escalation (TA0004): The numerous Kernel and Driver EoP flaws map to Exploitation for Privilege Escalation (T1068). This is how an attacker goes from a basic user to SYSTEM authority.
- Defense Evasion (TA0005): Flaws in Microsoft Defender (also patched) relate to Impair Defenses: Disable or Modify Tools (T1562.001). A successful exploit could turn off your primary antivirus.
- Execution (TA0002): The RCE vulnerabilities directly enable Command and Scripting Interpreter (T1059) and Native API (T1106) for code execution.
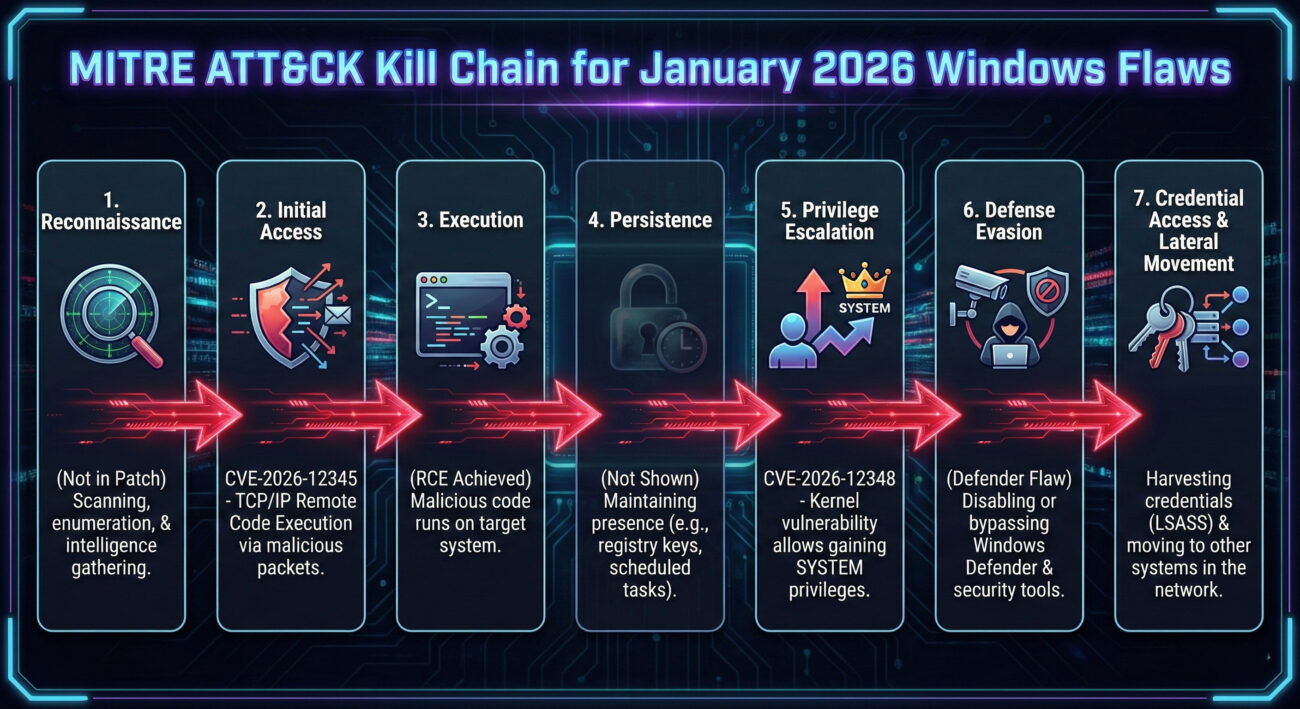
Real-World Scenario: Chaining Flaws for Maximum Impact
Let's construct a hypothetical attack scenario using vulnerabilities from this Patch Tuesday to illustrate the real danger.
Step 1: Initial Foothold via Wormable RCE
An attacker scans the internet for Windows servers with exposed networking services. They weaponize the public exploit for the Critical TCP/IP flaw (CVE-2026-12345). By sending a malicious packet, they gain remote code execution on the server with low-privilege access (IIS or NETWORK SERVICE account).
Step 2: Privilege Escalation to SYSTEM
From this low-privilege shell, the attacker uses a local exploit for a patched Kernel Elevation of Privilege flaw (CVE-2026-12348). This technique, mapped to MITRE ATT&CK T1068, grants them NT AUTHORITY\SYSTEM privileges, the highest level on Windows.
Step 3: Defense Evasion & Lateral Movement
Now as SYSTEM, they deploy a malware payload. To avoid detection, they might first exploit a separate vulnerability in Microsoft Defender (also patched this cycle) to disable it temporarily. They then dump credentials from the Local Security Authority (LSASS) and use them to move laterally to other workstations and servers in the network, potentially deploying ransomware.
This chain shows how patching just one flaw is insufficient. Attackers chain vulnerabilities. Missing any patch in this chain could lead to a full network breach.
Technical Perspective: How These Windows Vulnerabilities Work
For beginners, understanding the "how" demystifies the threat. Let's examine a common root cause: Buffer Overflow.
The Anatomy of a Buffer Overflow (Simplified)
Many RCE and EoP flaws stem from buffer overflows. A buffer is a temporary storage area in memory. If a program doesn't check the size of input data before copying it into a buffer, excess data can "overflow" into adjacent memory.
Example (Conceptual C Code): Imagine a function in a network driver that handles packets.
void vulnerable_function(char *packet_data) {
char buffer[64]; // Allocates 64 bytes of memory
// DANGER: No length check!
strcpy(buffer, packet_data); // Copy packet data into buffer
// If packet_data is 100 bytes long, 36 bytes overflow!
}
An attacker crafts a malicious packet with 100 bytes of data, where the overflow portion contains carefully crafted machine code (shellcode) and a new return address. When the function finishes, instead of returning to the normal code, it jumps to the attacker's shellcode in the buffer, executing their commands.
Microsoft's patches often add proper input validation, use safer string functions (like strcpy_s), or implement Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP) more effectively.
Red Team vs. Blue Team: Attackers vs. Defenders
The discovery and patching of these 114 flaws create a dynamic battlefield. Here's how both sides view this Windows Patch Tuesday.
Red Team / Threat Actor View
- Opportunity: The 4 publicly disclosed vulnerabilities are immediate targets. Reverse-engineering patches (diffing) to create working exploits for the other 110 begins now.
- Focus: The wormable, network-based RCE flaws (like TCP/IP) are gold, they enable mass infection and botnet creation.
- Strategy: Develop exploit chains combining an RCE with an EoP for reliable, high-privilege access. Test against unpatched systems in the wild.
- Goal: Deploy ransomware, steal data, or establish persistent access before organizations can apply the patches.
Blue Team / Defender View
- Urgency: The clock is ticking. The "patch gap" between release and enterprise-wide deployment is when attacks surge. Critical patches must be prioritized.
- Focus: Asset management is key. You can't patch what you don't know exists. Identify all systems running affected Windows versions and roles (servers, workstations).
- Strategy: Implement a layered defense. While testing and deploying patches, enable compensating controls: firewall rules to restrict vulnerable services, intrusion prevention system (IPS) signatures, and strict application whitelisting.
- Goal: Minimize the attack surface, deploy patches efficiently, and detect any exploitation attempts through vigilant monitoring.
Step-by-Step Patch Implementation Guide
For system administrators and security beginners, here is a structured approach to handling this massive Patch Tuesday.
Step 1: Triage & Prioritization (Within 24 Hours)
Immediately review the official Microsoft Security Update Guide. Filter for Critical RCE vulnerabilities affecting your environment. Prioritize patches for: 1) Publicly disclosed flaws, 2) Wormable RCE flaws, 3) Server-facing services (TCP/IP, DHCP, HTTP.sys).
Step 2: Testing in an Isolated Environment
Never patch production first. Deploy patches to a representative test environment. Verify they don't break critical business applications. Automated testing tools can help, but manual checks are vital.
Step 3: Phased Production Deployment
Deploy in waves:
- Wave 1 (Day 2-3): Low-risk, non-critical workstations.
- Wave 2 (Day 4-5): Servers with less critical functions and remaining workstations.
- Wave 3 (Day 6-7): Mission-critical servers, often during a scheduled maintenance window.
Use tools like Windows Server Update Services (WSUS), Microsoft Endpoint Configuration Manager, or enterprise-grade RMM/patching platforms.
Step 4: Verification & Monitoring
Confirm patches are installed (e.g., wmic qfe list or Get-Hotfix in PowerShell). Increase security monitoring (SIEM, EDR) for signs of exploitation attempts against the newly patched vulnerabilities, which indicates targeted attacks.
Common Mistakes & Best Practices in Patch Management
Common Mistakes to Avoid
- Indefinite Delay: "We'll patch next quarter." This gap is where breaches happen.
- No Testing Environment: Patching blindly causes downtime, leading to a culture of fear around updates.
- Incomplete Inventory: Missing legacy or embedded systems that can't be patched easily, creating permanent holes.
- Ignoring Third-Party Apps: Focusing solely on Windows while Java, Adobe, or other software remains vulnerable.
Best Practices to Implement
- Establish a SLSA: Define a Service Level Agreement for patching (e.g., "Critical patches deployed within 72 hours").
- Automate Where Possible: Use automated patch management tools to reduce human error and speed up deployment.
- Maintain a Fallback Plan: Always have a documented rollback procedure in case a patch causes instability.
- Integrate with Vulnerability Management: Use a VM platform to track patch status as part of your overall risk posture.
- Educate End-Users: For home users or small businesses, enable automatic updates. It's the single most effective defense.
Proactive Defense Framework
Patching is reactive. Build a proactive framework to harden your environment against future, unknown flaws.
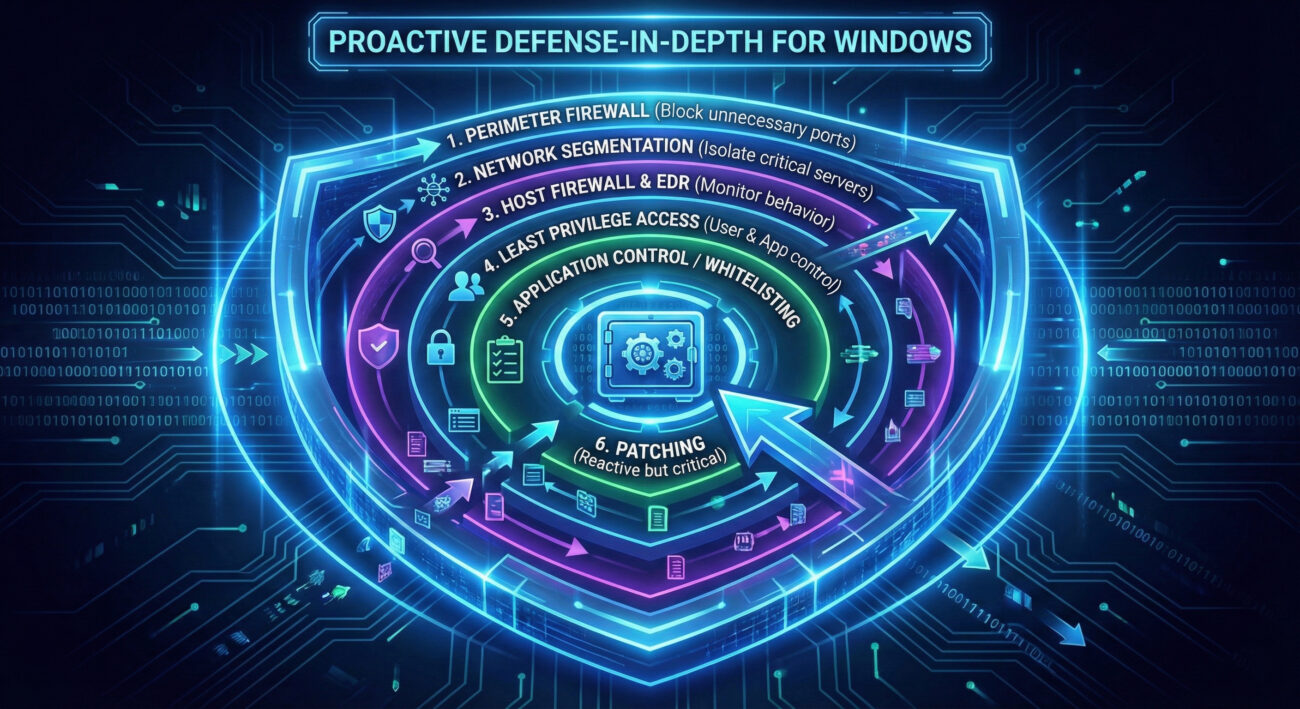
- Implement Least Privilege: No user should run as Administrator daily. This drastically reduces the impact of many EoP flaws.
- Network Segmentation: Isolate critical servers. A compromised workstation shouldn't be able to talk directly to your domain controller or SQL server.
- Robust EDR / XDR: Deploy Endpoint Detection and Response solutions that can detect suspicious behavior (like attempt to exploit a buffer overflow) even before a patch is available.
- Application Allowlisting: Use tools like AppLocker or Windows Defender Application Control to only allow approved programs to run, blocking unknown malware payloads.
Frequently Asked Questions (FAQ)
Q1: I'm a home user. What should I do immediately?
A: Go to Settings > Update & Security > Windows Update and click "Check for updates." Install all updates immediately. Enable "Automatic Updates" if it's off. This is your most critical protection.
Q2: What if I can't patch a critical server because it runs legacy software?
A: This is a high-risk situation. You must implement compensating controls:
- Isolate the server behind a firewall, blocking all access except from absolutely necessary IPs.
- Deploy an Intrusion Prevention System (IPS) with a signature for the specific CVE if available.
- Monitor the server aggressively for any signs of compromise.
- Create a plan to migrate or replace the legacy application.
Q3: How do attackers find these vulnerabilities?
A: Through a mix of methods: fuzzing (sending random data to programs to find crashes), reverse engineering, code audit, and purchasing them from the cyber criminal underground or bug bounty programs. Microsoft also receives reports from security researchers worldwide.
Q4: Is it safe to use third-party patch management tools?
A: Reputable tools from established vendors (like ManageEngine, Ivanti, Automox) are generally safe and can be more efficient for large networks. Ensure they are properly configured and secured, as they hold high-level access.
Key Takeaways: What Every Security Professional Must Remember
- Windows Patch Tuesday January 2026 is a major security event. Delay is risk. The 14 Critical and 4 publicly known flaws are actively being targeted.
- Understand the attack chain through MITRE ATT&CK. Vulnerabilities are not isolated; attackers chain Initial Access (RCE) with Privilege Escalation (EoP) for full control.
- Patching is a process, not an event. Follow a structured patch management lifecycle: Prioritize, Test, Deploy in phases, Verify.
- No single defense is perfect. Combine prompt patching (reactive) with proactive measures like least privilege, network segmentation, and robust monitoring (EDR/XDR) for a true defense-in-depth strategy.
- For beginners and home users: Turn on Automatic Updates. It's the simplest, most effective action you can take.
Call to Action: Secure Your Systems Now
Your Next Steps
Do not let this be just another article you read. The vulnerabilities from this Windows Patch Tuesday are real and present danger.
- Audit: Within the next hour, check the update status on your primary machine and one critical server you manage.
- Plan: If you're a professional, review your organization's patch management policy today. Does it mandate patching Critical flaws within 7 days? If not, advocate for change.
- Learn: Deepen your knowledge. Bookmark these essential resources:
- Microsoft Security Update Guide (Official Source)
- MITRE CVE Database (Vulnerability Database)
- MITRE ATT&CK Framework (Adversary Behavior Knowledge Base)
- CISA Known Exploited Vulnerabilities Catalog (Government-Tracked Active Threats)
Cybersecurity is a continuous journey. Start by conquering this Patch Tuesday. Update, secure, and defend.
© 2026 Cyber Pulse Academy. This content is provided for educational purposes only.
Always consult with security professionals for organization-specific guidance.


















































